I have my vm:s up and running now, but I like my rig to be patched and updated, even if I only have 7 machines I want to centralize update procedure. I have chosen to do this with Ansible. As this is a demo site that I am setting up. Security of some configuration is not the best, but in this case I do not care. This is a proof of concept not a customer installation. I am also new at Ansible, but I love to know more.
Lets start with a picture:

The linux client was really easy to implement even if I never seen this before. So we start with that. Kali is the client and Ansible is the server.
What do you need on the Ansible server
- Ansible
- ssh access with keys to the ansible clients (kali)
What do you need on the clients that you want to patch with Ansible?
- Create a user (in my case ansible)
- Configure ssh login from ansible machine with keys
- The ansible user on the clients need to be able to get to root
First we start with the ansible server
- Install Ansible
sudo apt install ansible

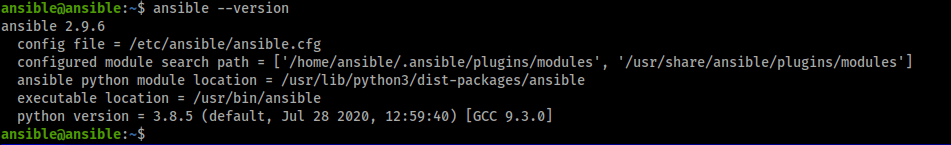
Thats it from the server side right know. Even I solved that one!
Ansible clients we want updates on.
- Enable ssh
- Add user ansible
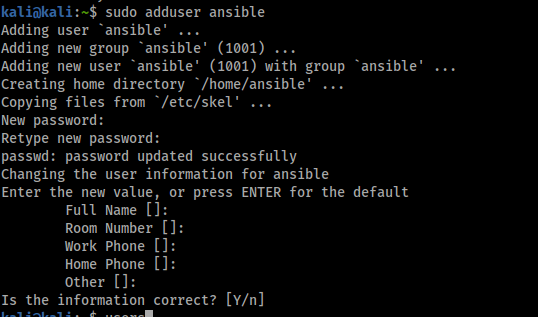
3. Then we need to make the ansible user ability to sudo without password.
echo "ansible ALL=(ALL) NOPASSWD:ALL" | sudo tee /etc/sudoers.d/ansible
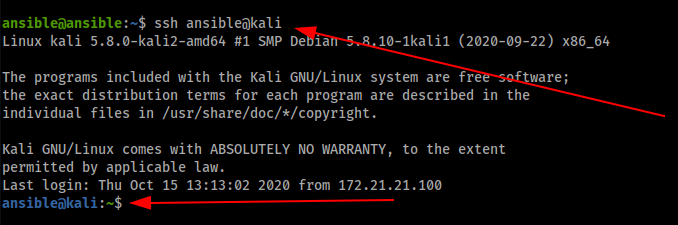
From the ansible server
ssh-copy-id ansible@kali
Now the Ansible user from Ansible server can access the kali box thru ssh with private and public key.
From the Ansible server try it.
ssh ansible@kali
Time to configure Ansible server
- Log in on ansible server as ansible
- create a directory (jobs)
- Go to jobs directory
- create a file named linux-hosts
- create a file named linux-update.yml
- create a file named linux-autoremove.yml
Content of the linux-host file:
#set up ssh user name and pyhton# [all:vars] ansible_user='ansible' ansible_become=yes ansible_become_method=sudo ansible_python_interpreter='/usr/bin/env python3' #ip or server name [servers] kali parrot online kracken jump ansible
Content of the linux-update file:
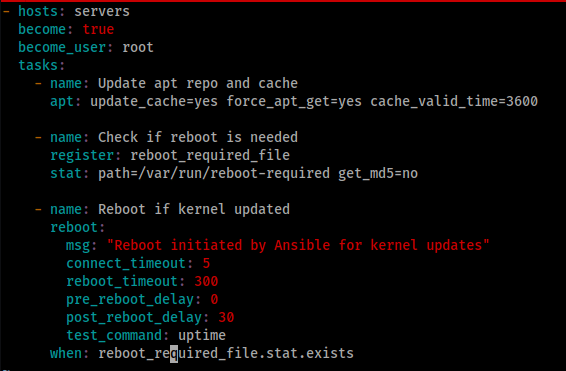
Time to update all servers at the same time! And 5 server out of 6 had update that installed in one command.
ansible-playbook -i ./linux-hosts linux-update.yml

Now you want to do autoremove of old packages! Like you do with apt autoremove
The content of the linux-autoremove
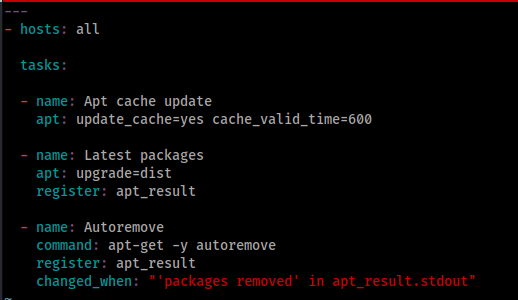
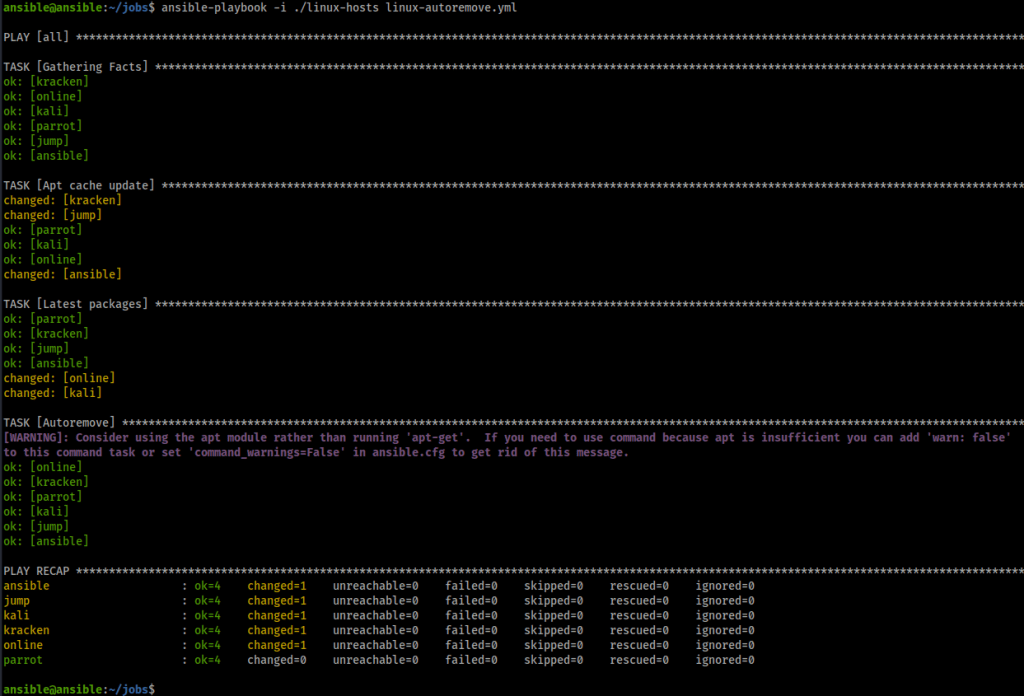
Time to clean the clients of application that are not needed!
ansible-playbook -i ./linux-hosts linux-autoremove.yml
Time to update my Windows 10 box
On the ansible server we need to install ansible package:
ansible-galaxy collection install ansible.windows
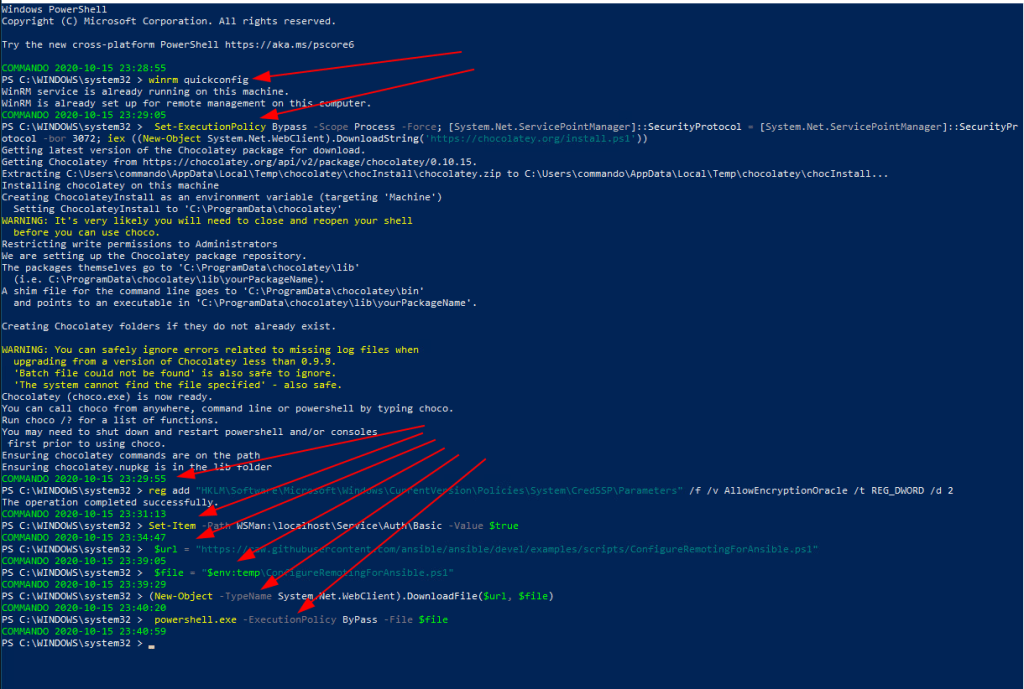
On the Windows 10 box we need to do some unsecure stuff!
Start PowerShell as Administrator and past below:
Set-ExecutionPolicy Bypass -Scope Process -Force; [System.Net.ServicePointManager]::SecurityProtocol = [System.Net.ServicePointManager]::SecurityProtocol -bor 3072; iex ((New-Object System.Net.WebClient).DownloadString('https://chocolatey.org/install.ps1'))
In the same Powershell shell type the following
winrm quickconfig reg add "HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System\CredSSP\Parameters" /f /v AllowEncryptionOracle /t REG_DWORD /d 2 Set-Item -Path WSMan:\localhost\Service\Auth\Basic -Value $true $url = "https://raw.githubusercontent.com/ansible/ansible/devel/examples/scripts/ConfigureRemotingForAnsible.ps1" $file = "$env:temp\ConfigureRemotingForAnsible.ps1" (New-Object -TypeName System.Net.WebClient).DownloadFile($url, $file) powershell.exe -ExecutionPolicy ByPass -File $file winrm enumerate winrm/config/Listener
Now it is time to create som files for Ansible. I ended up ing it like this:
On the Ansible server with ansible username under jobs directory I created a file win-hosts:
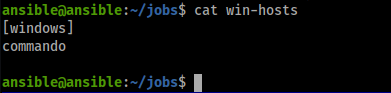
Then we need to create playbookfile
ansible@ansible:~/jobs$ cat windows_baseline.yaml
name: Windows Baseline
hosts: “{{ target }}”
connection: winrm
gather_facts: true
vars:
ansible_user: “{{ user }}”
ansible_password: “{{ password }}”
ansible_connection: winrm
ansible_winrm_transport: basic
ansible_winrm_server_cert_validation: ignore tasks:
name: Install Baseline Packages
include_role:
name: install
name: Perform Updates
include_role:
name: updates

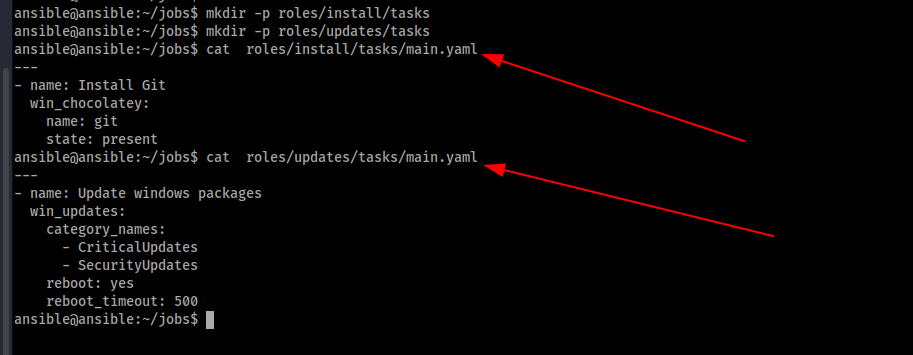
Create these two directory under jobs
mkdir -p roles/install/tasks mkdir -p roles/updates/tasks Then create two files main.yaml under these directory vi roles/install/tasks/main.yaml vi roles/updates/tasks/main.yaml
Finaly we can try this autmation of updates. Yes we have only one machine. But just add more then.
ansible-playbook -i ./win-hosts -e target=windows -e user=ansible -e password=secret windows_baseline.yaml
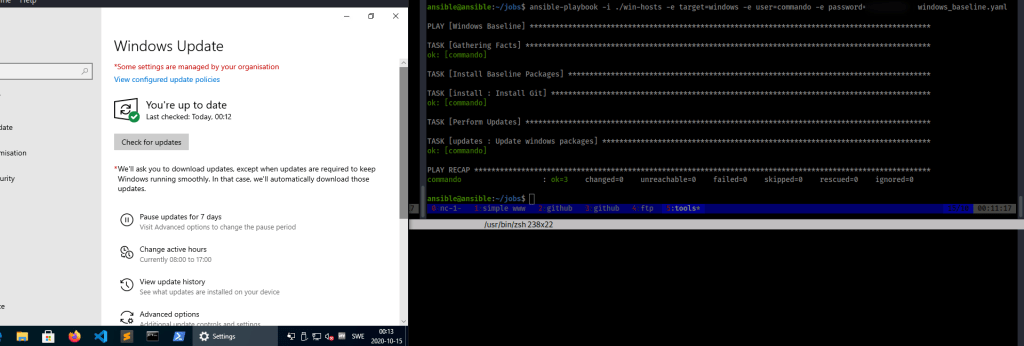
Now we have patched our hacking rig. Both Windows and Linux machine with ansible!

Leave a comment