I must thank @BHinfoSecurity to get my interest in this. There webinars is great, especially 30 minutes before the real webinar begins.
Now lets get started. As you have seen I did installation of 16.04 version before. My mistake, to tired! No I have to do this again with the new version. Like 16.04 version this is easy to install. That’s the easy part. Then you need to learn all the stuff that is in SecurityOnion. But that’s for another day. Installation today.
We start with a picture
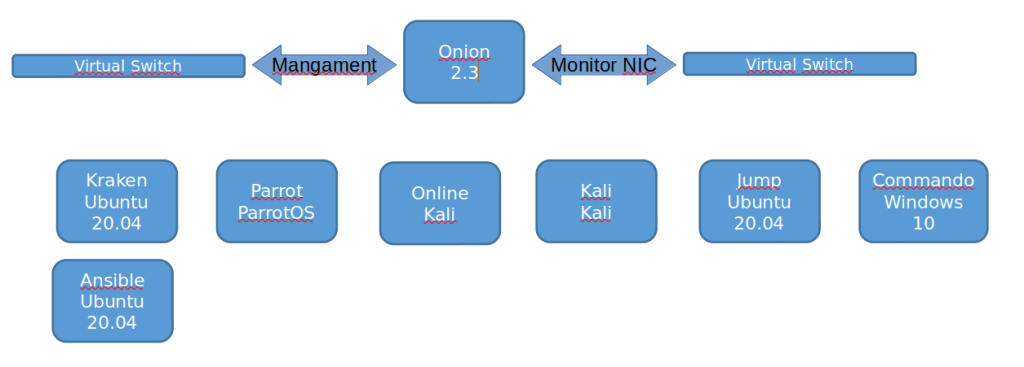
As before we created a VM with two nics. The cpu and memory you get what you want. RTFM for more information.
https://docs.securityonion.net/en/2.3/
I got the newer CD downloaded and started the installation.
https://github.com/Security-Onion-Solutions/securityonion
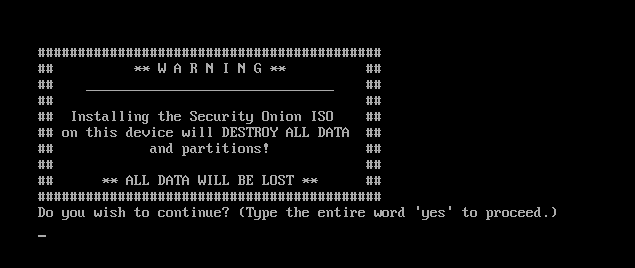
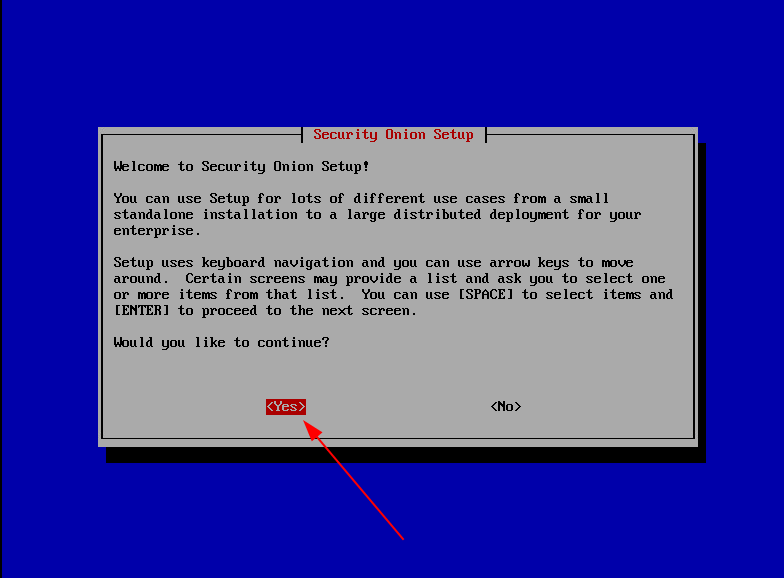
First screen that pops up is this, and yes I want to do it!
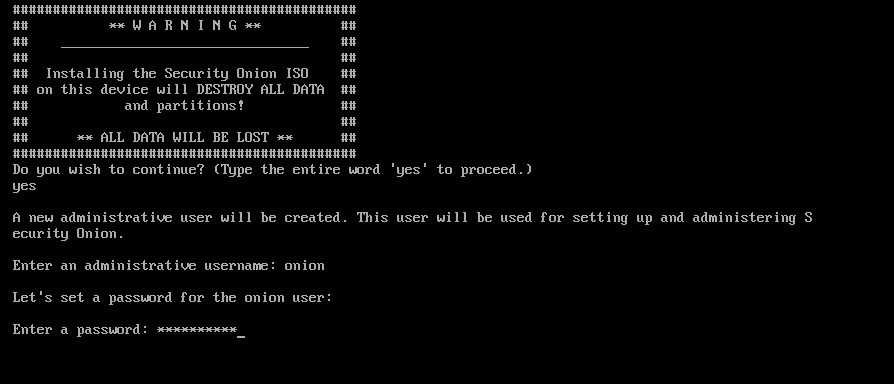
And then we also need to add a user to the system
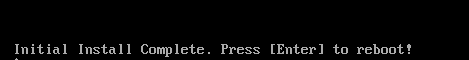
After some time you get this, and guess what I did?
After reboot you login with your account and get this screen and choose yes
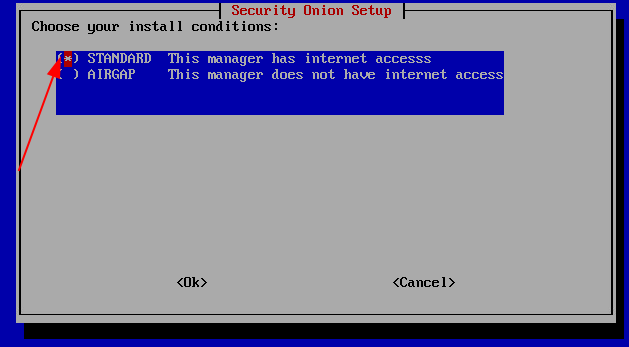
The we shall make a choice of what type installation this is. You can do a POC or production setup distributed or stand alone.

Do you have internet access on this host? I do so I will go for standard.
I know that we have Ansible in this setup but I will go for automatic update on this one. We never know what happens to that box in the future.

Set your hostname for this machine, onion in my case.

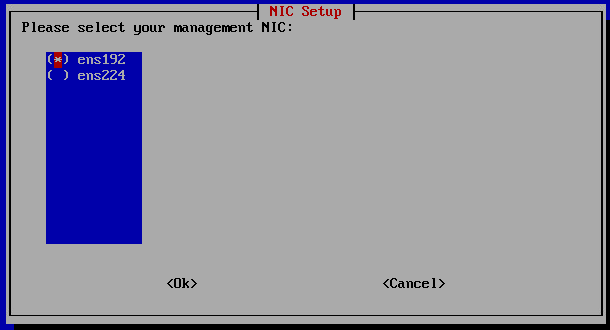
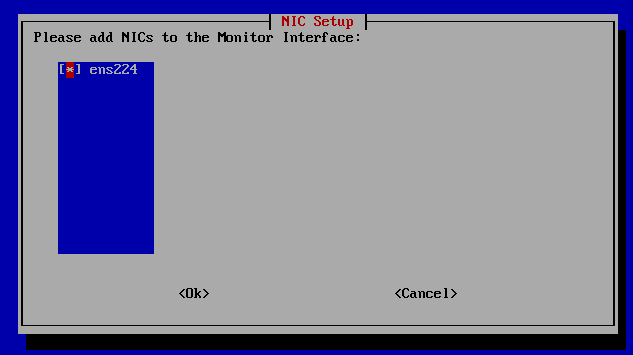
We have two nics one for management and one for sniffing traffic. In my case ens192 is my management and ens224 is sniffer.
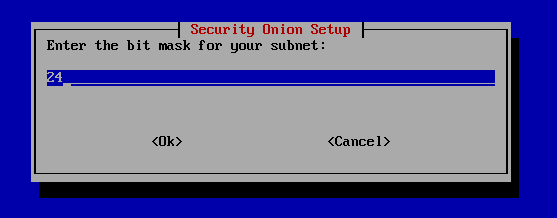
Setup the management ip addres on the onion box.
You need to know this:
IP adress
Mask
Default Gateway
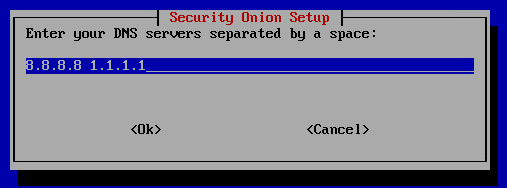
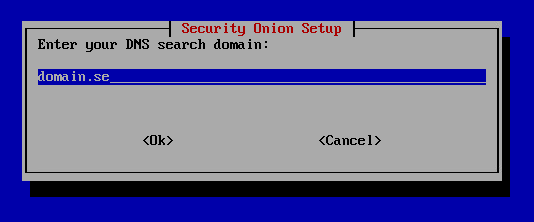
DNS
Search domain name



It is time to get to the sniffing. What card do you want to use? I only got 1 to select. The other one is for management!
Specify your private networks, I go for the standard.

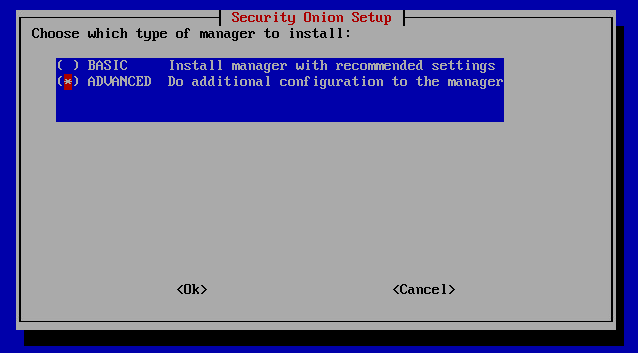
I will go for the advanced setup of the manage because I am cool.
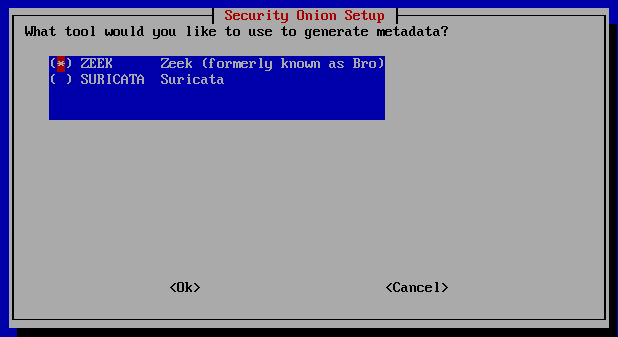
Zeek is my man
I have not yet a subscriptions for the rules, So I will stick to the free ones.

What logs do you want to send. Standard is everything in that list.

YES we want to try everything!

Put our email adress, as the text says it is used for some logins and functions in SecurityOnion
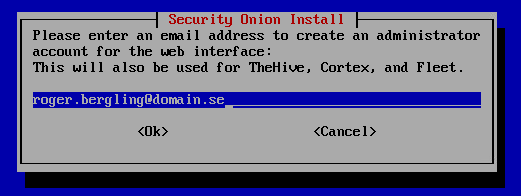
Set password for above user

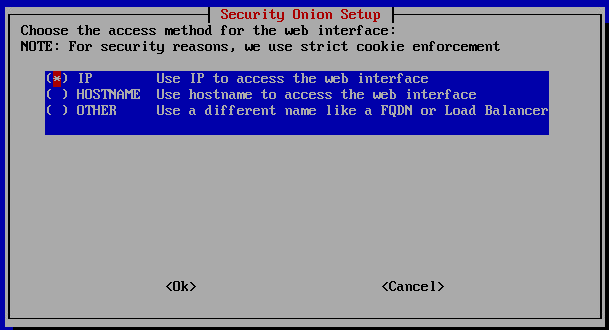
How are you gonna access the management interface? IP hostname och FQDN. I use ip because this is a closed environment.
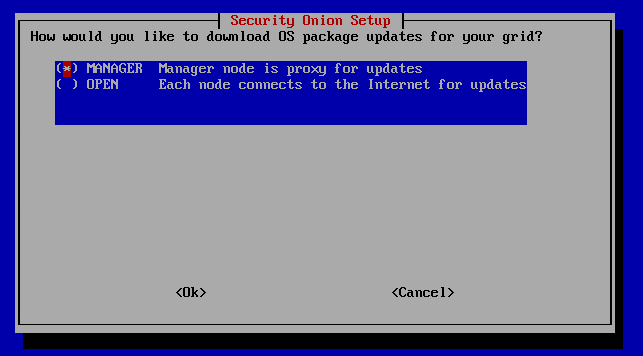
Are you installing SecurityOnion distributed, how do you want your updates to get to the nodes. Thru the Manager or directly. I have only 1 Manager so easy for me.
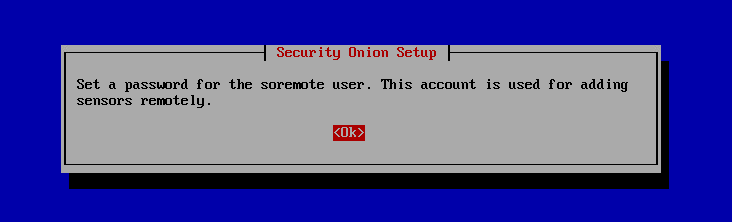
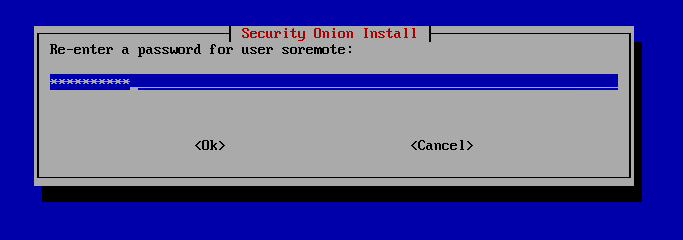
To be able to add remote sensor in the future you need a user for that. We create this here.
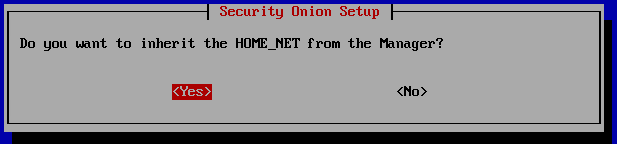
Yes I want this, or if you know that private network is different on the nodes pleas add those. I will go for yes.
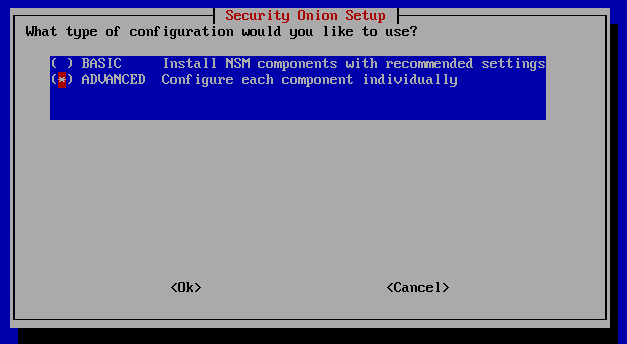
I fell hardcore today, I will do the advance config.
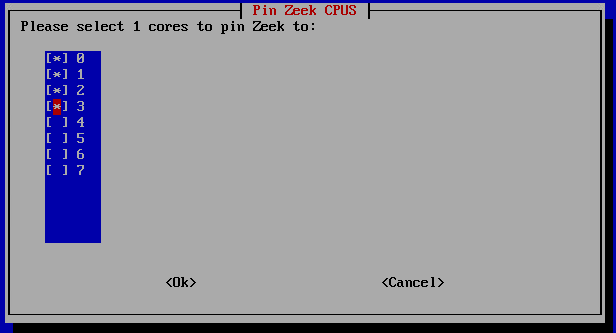
How many cores will zeek be pinned to? i will pin it to 4 cores.
Suricata will get 2 cores pinned

I have not implemented jumbo frames in this setup so I will go for the standard MTU size. 1500

I am still feeling cool so I will configure my searchnode with advanced mode.

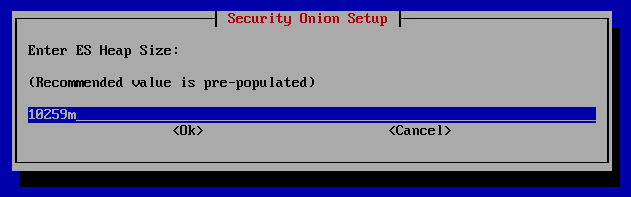
Set the ES Heap size. How much memory is gonna be used in elastic search for the java process. I will go with what the installation says.
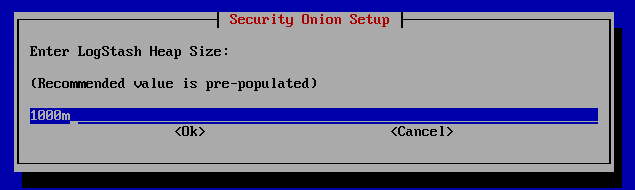
LogStash memory in java will get this.
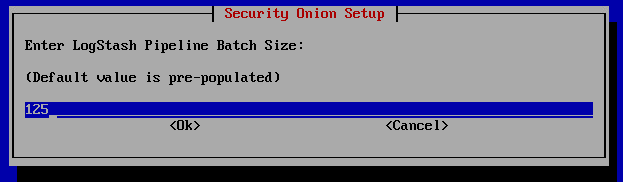
LogStash split up the work with virtual pipelines. To get more speed.
If you want to know more:
https://www.elastic.co/guide/en/logstash/current/pipeline-to-pipeline.html


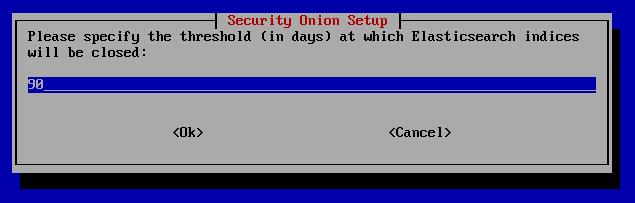
How many days will indices be open. Standard is 30. I will raise this to 90.
I only configure this machine with 1 TB so 576GB for Elsticsearch data.

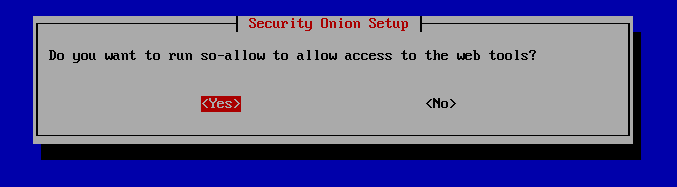
Yes I want to be able to access the management
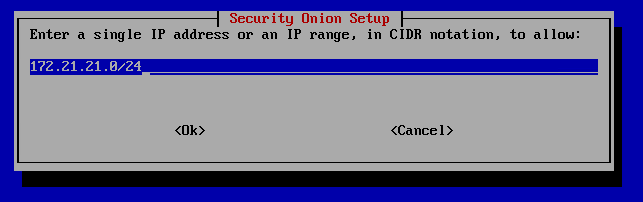
I will enable my closed private network to allow access.
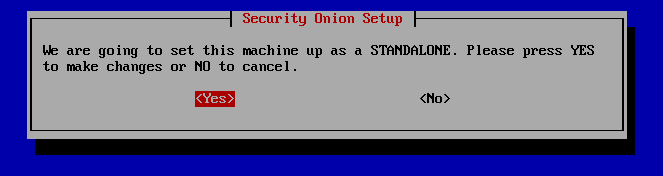
Standalone it is!
Coffee time! For this machine it took
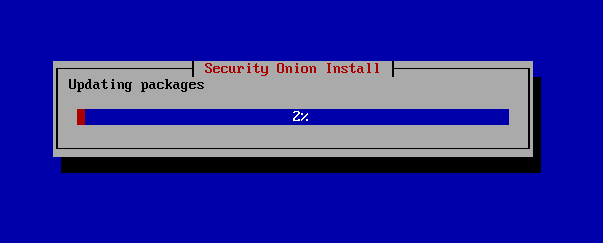
Around 10 minutes later it is done! Time to reboot and access the webinterface!

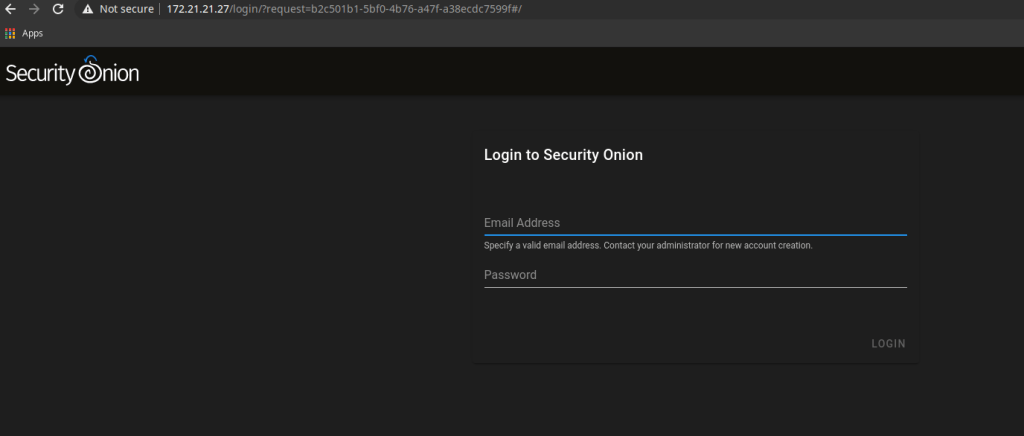
Efter reboot I use a web browser to access SecurityOnion
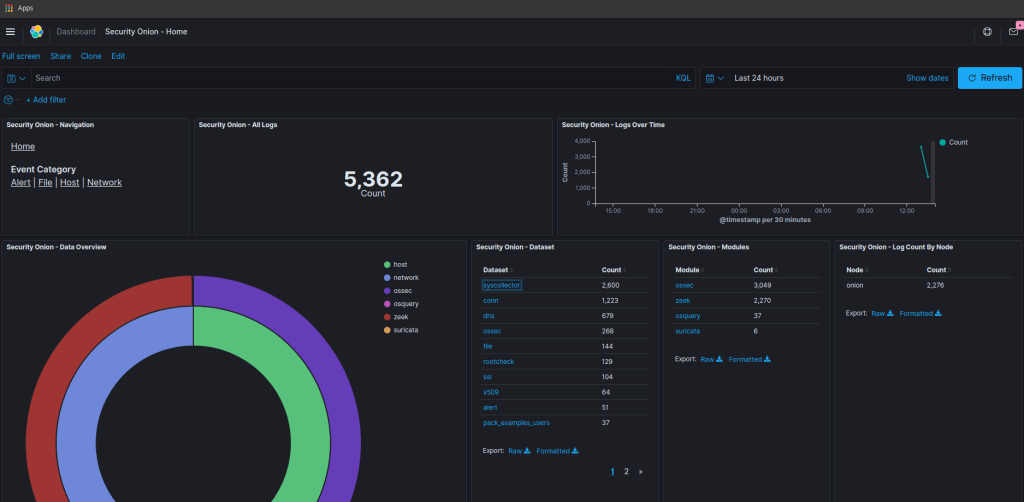
After the login we are up and running, time to play around
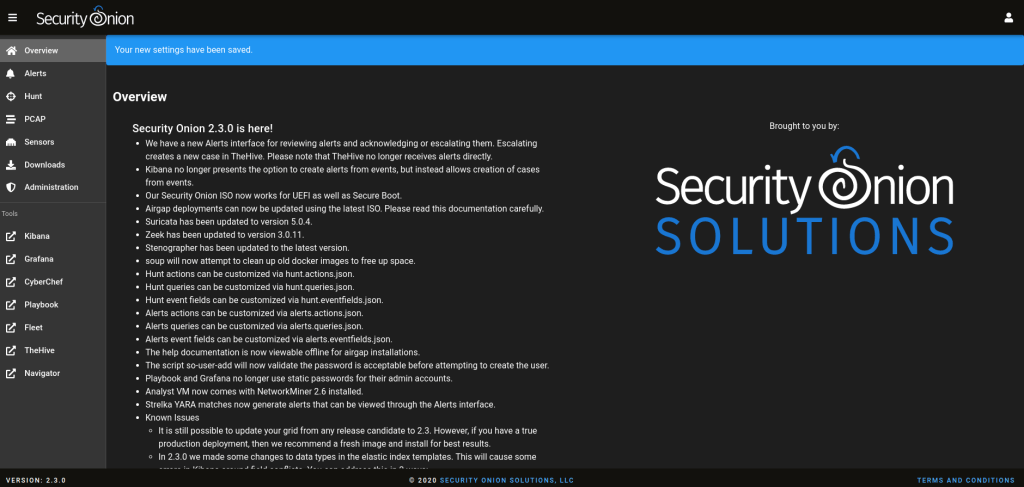
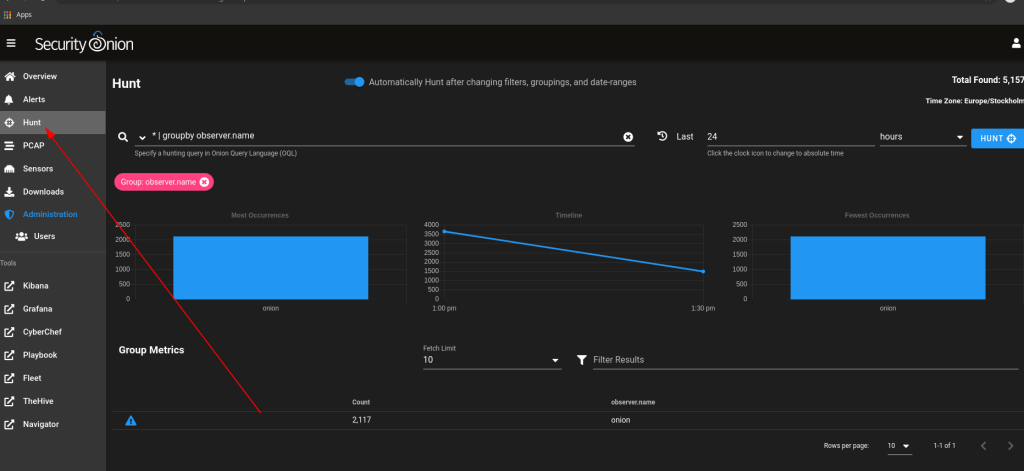
We can start to hunt stuff
We have the kibana interface
Grafana interface

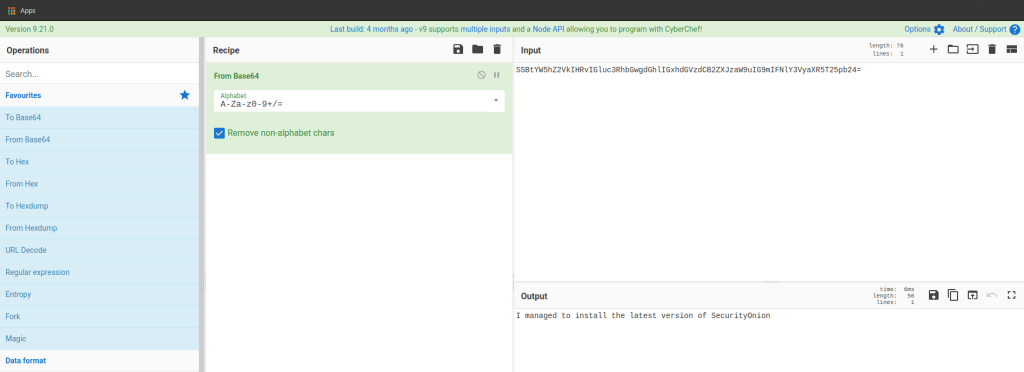
Cyberchef is included
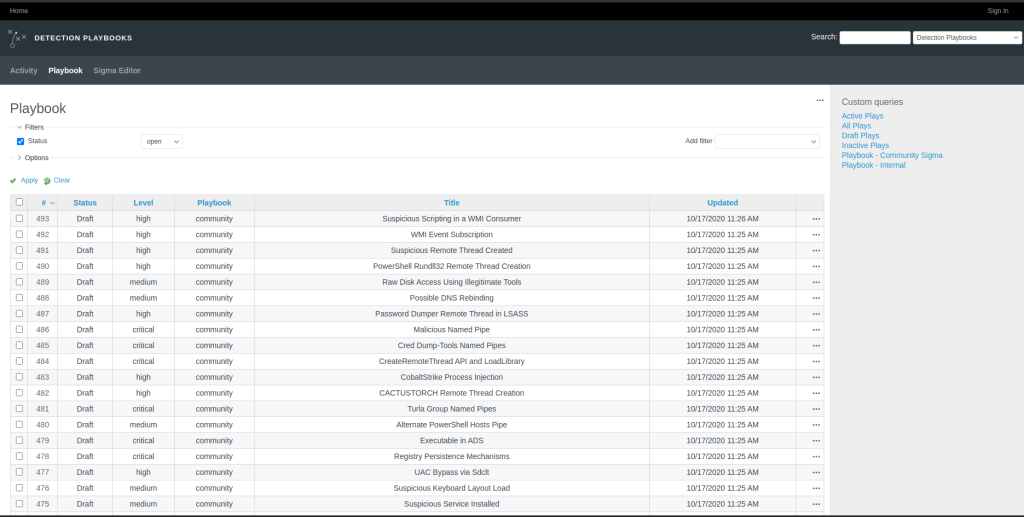
Detection Playbooks
Kolide Fleet

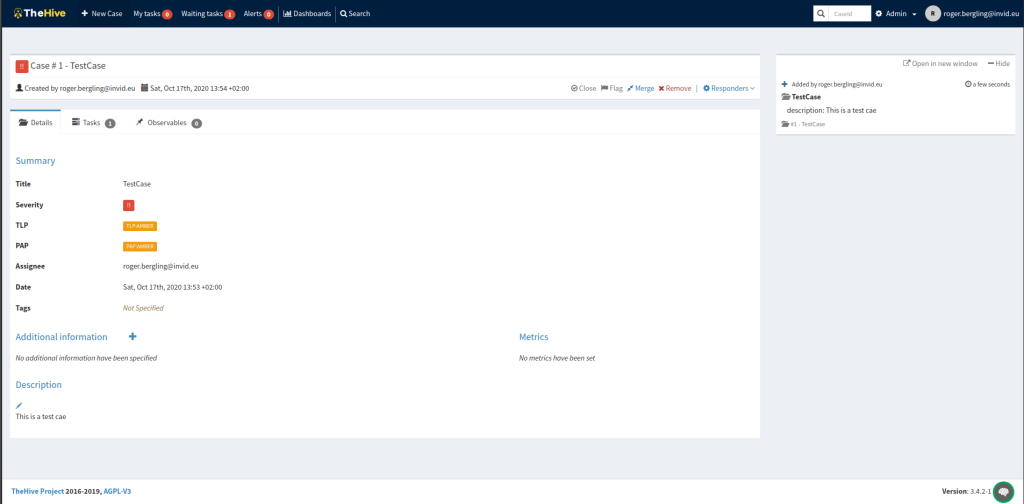
The Hive with a test case
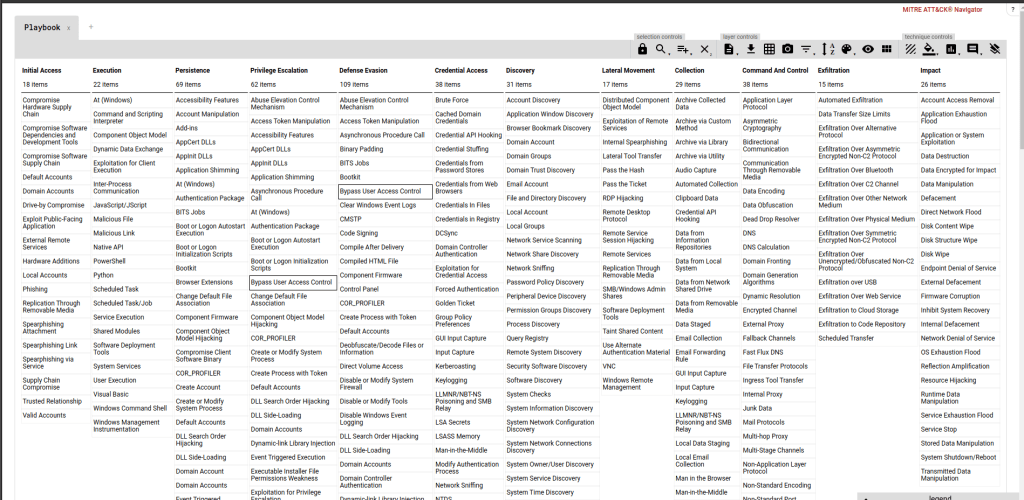
Mitre Attack Navigator
So the installation is done and everything seems to work. Now dig in the different applications and try to understand stuff!
Have a great day!

Hi Can you help me in creating custom logstash configurations in Security Onion 2?
Thanks
LikeLike
If I find some time in the furture, but now I am looking at C2 enviroments. Comming soon…
LikeLike