It is time to test LogonTracer from @jpcert_en you can get your copy from https://github.com/JPCERTCC/LogonTracer
From the website:
LogonTracer is a tool to investigate malicious logon by visualizing and analyzing Windows active directory event logs.
We start with a new installation of ubuntu. The servername for this is Logon. The installation is not in this post.
LogonTracer for me is like Bloodhound for event logfiles.
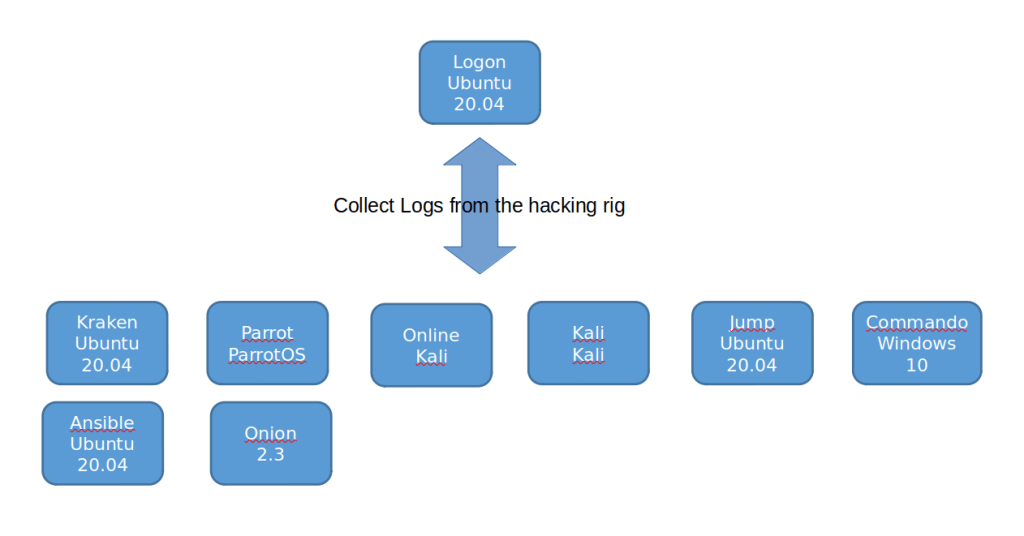
We start with a picture
First I tried to do the installation, but i was a pain in the ass to get this up and running under ubuntu 20.04. So I switched to docker instead.
First install some stuff to get docker up and running.
sudo apt-get install \
apt-transport-https \
ca-certificates \
curl \
gnupg-agent \
software-properties-common
Then import the key from docker
sudo curl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo apt-key add -
Add repo for docker
sudo add-apt-repository \
"deb [arch=amd64] https://download.docker.com/linux/ubuntu \
$(lsb_release -cs) \
stable"
Then we install docker
sudo apt-get install docker-ce docker-ce-cli containerd.io
Finally we pull the LogonTracer from docker
sudo docker pull jpcertcc/docker-logontracer
Then we run LogonTracer docker instance
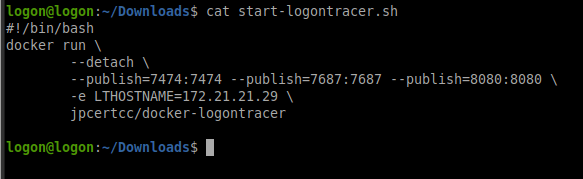
sudo docker run \ --detach \ --publish=7474:7474 --publish=7687:7687 --publish=8080:8080 \ -e LTHOSTNAME=172.21.21.29 \ jpcertcc/docker-logontracer
We create a sh file so it is easy to start:
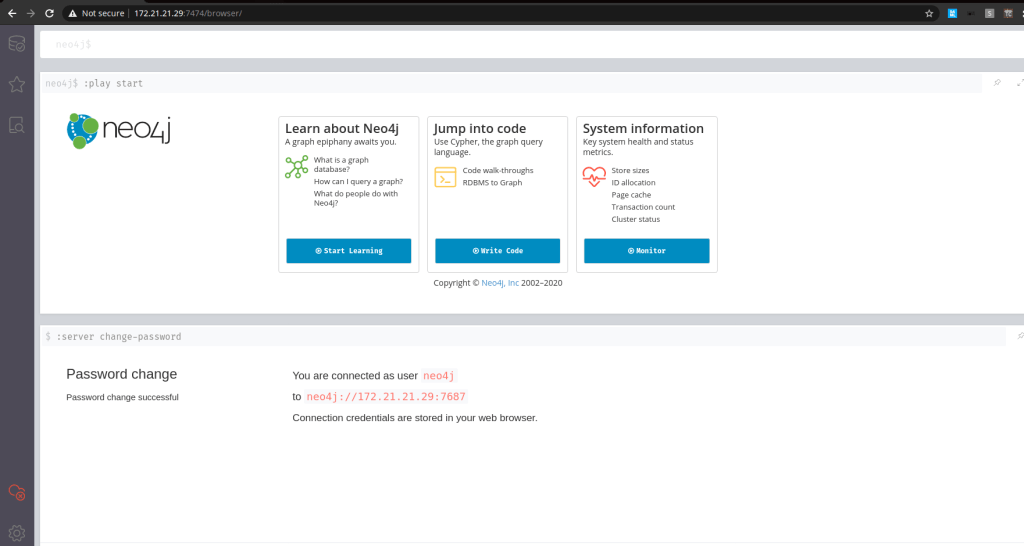
Access neo4j with username: neo4j and password: password
Access LogonTracer
Clear the “demo” database from neo4j
MATCH (n) OPTIONAL MATCH (n)-[r]-() DELETE n,rUse above command in neo4j

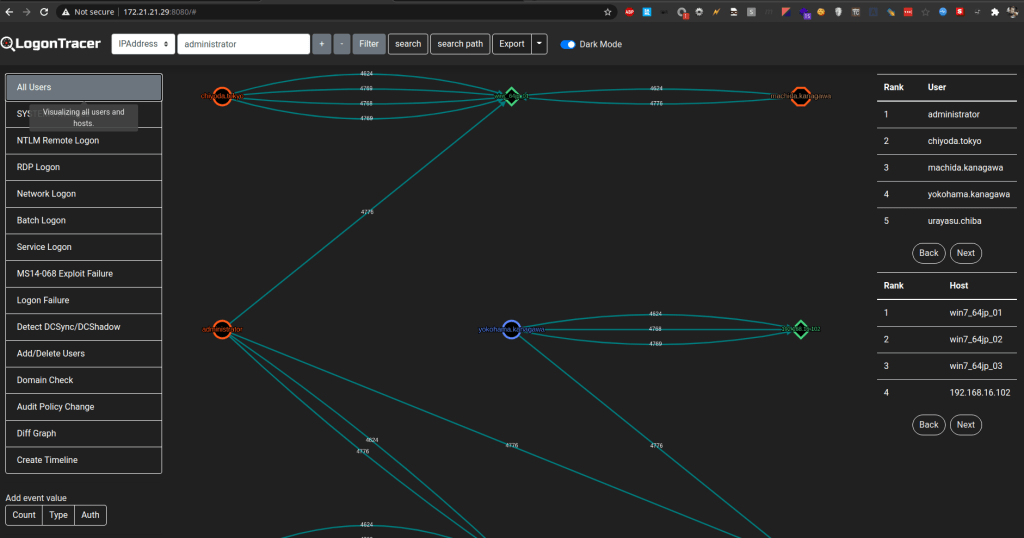
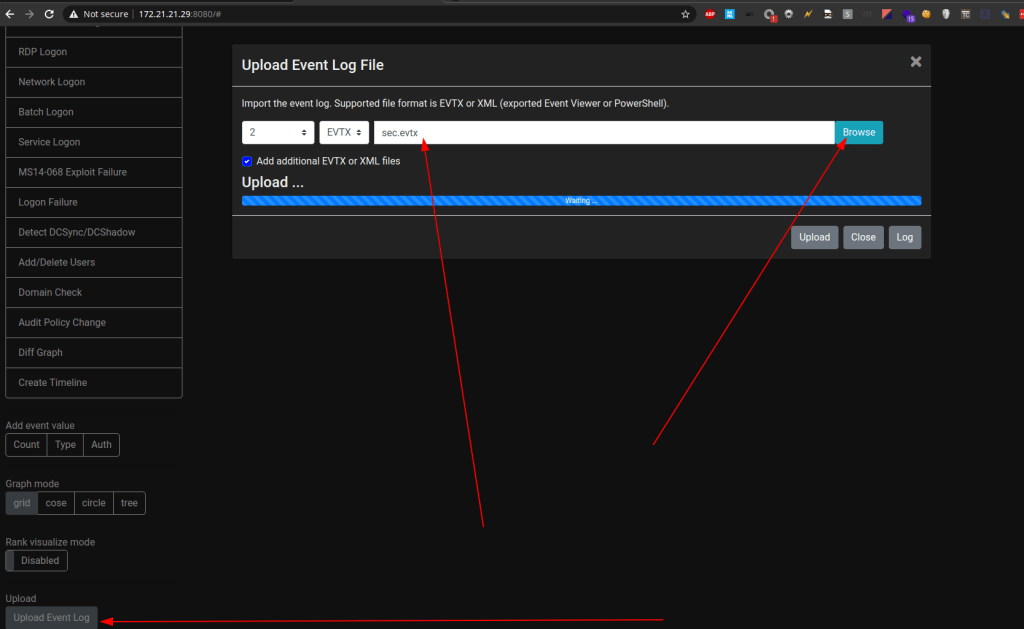
Import event log files from windows.
- Export evtx log files from windows
- import the to LogonTracer
After import we can search for the goodies!

I hope this will help someone to get started with LogonTracer.

Leave a comment