In this post I will try to explain why it is important to use masks when you crack password from hashes with hashcat. The machine that I run hashcat on has 2 Tesla M60 card and running Linux. Why do I not use longer password in this test, I do not want to wait 7 days just to show a point. It is also depends on what type of hashes that you will crack. In this example we use NTLM hashes.
You will brake hashes faster if you know the password policy for example. If the password policy says at least 6 characters and one number you can save a lot of time cracking hashes because you know how to build the mask for hashcat.
We start with the password that we will use to test my theory.
love
HIGH
l#ow
H#IG
#L%r
The NTLM hashes for above password are like this:
85DEEEC2D12F917783B689AE94990716
6E21570B203F2D9AE145932A8FF2D3E9
985F751BFDC910F62C8BBE48C1E86D1A
2FD0F98F072F7085DF0BB31D9C9FA4EA
833DF42D998CF3A345796D5F69D82015
Create a file with above hashes. I called it hash1.txt , hash2.txt, hash3.txt, hash4.txt and hash5.txt
echo 85DEEEC2D12F917783B689AE94990716 > hash1.txt echo 6E21570B203F2D9AE145932A8FF2D3E9 > hash2.txt echo 985F751BFDC910F62C8BBE48C1E86D1A > hash3.txt echo 2FD0F98F072F7085DF0BB31D9C9FA4EA > hash4.txt echo 833DF42D998CF3A345796D5F69D82015 > hash5.txt cat hash1.txt hash2.txt hash3.txt hash4.txt hash5.txt 85DEEEC2D12F917783B689AE94990716 6E21570B203F2D9AE145932A8FF2D3E9 985F751BFDC910F62C8BBE48C1E86D1A 2FD0F98F072F7085DF0BB31D9C9FA4EA 833DF42D998CF3A345796D5F69D82015
If we want we can just use hashcat as is and use the guess.mask that is by default and see how many of above NTLM hashes we can crack. We will now try every hash to crack without any mask file. Standard brute force method with workload set to 3 and disable potfile so we don’t already have the hash in the database.
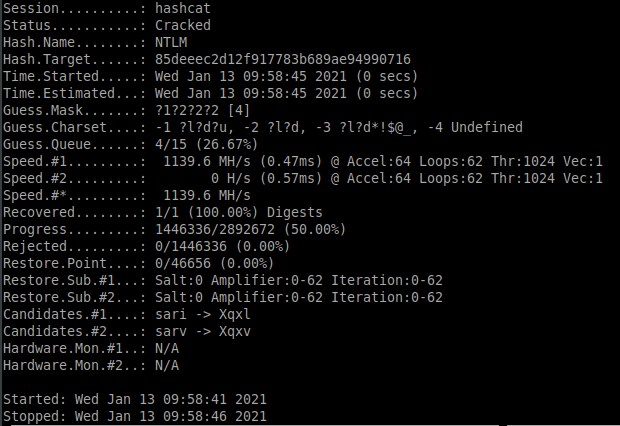
hash1.txt
./hashcat.bin -a 3 -w 3 -m 1000 ./hash1.txt –potfile-disable
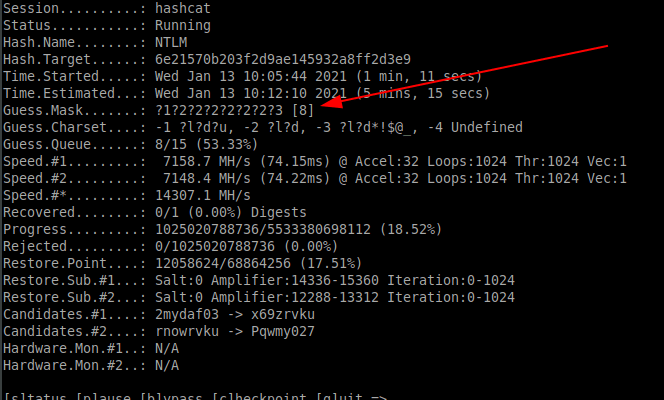
hash2.txt
As we can see below this can not be cracked using standard hashcat.
./hashcat.bin -a 3 -w 3 -m 1000 ./hash2.txt --potfile-disable
hash3.txt
As we can see below this can not be cracked using standard hashcat.
./hashcat.bin -a 3 -w 3 -m 1000 ./hash3.txt --potfile-disable

hash4.txt
As we can see below this can not be cracked using standard hashcat.
./hashcat.bin -a 3 -w 3 -m 1000 ./hash4.txt --potfile-disable

hash5.txt
As we can see below this can not be cracked using standard hashcat.
./hashcat.bin -a 3 -w 3 -m 1000 ./hash5.txt --potfile-disable

So as we can see with standard hashcat without anything special only one hash can be cracked
85DEEEC2D12F917783B689AE94990716
6E21570B203F2D9AE145932A8FF2D3E9
985F751BFDC910F62C8BBE48C1E86D1A
2FD0F98F072F7085DF0BB31D9C9FA4EA
833DF42D998CF3A345796D5F69D82015
Cracked Not Cracked Not Cracked Not Cracked Not Cracked
Now it is time to look at what can masks do for us for cracking hashes
What is a mask then? A mask describes how the password looks like in character by character.
?l - a single lowercase character
?u - a single uppercase character
?d - a single digit
?s - a single special characterExample for password HIGH the mask should look like this:
?u?u?u?u
How can I create large mask file copy and paste? No, there is a tool that I use that is called pack. The tools is created by https://github.com/iphelix the tool can be downloaded from https://github.com/iphelix/pack
Please read the page https://github.com/iphelix/pack and you will understand how this works.
So lets assume you know that all password is from 1-5 character and can contain lowercase uppercase digit and special charcters. How can you create such a file.
Create mask file with every possibility 1-5 characters.
python2 ../policygen/policygen.py --minlength 1 --maxlength 5 -o hash.hcmask

Then we use that mask to crack hash2.txt, hash3.txt, hash4.txt and hash5.txt and see if this works.
./hashcat.bin -a 3 -w 3 -m 1000 ./hash2.txt ./hash.hcmask --potfile-disable

./hashcat.bin -a 3 -w 3 -m 1000 ./hash3.txt ./hash.hcmask --potfile-disable

./hashcat.bin -a 3 -w 3 -m 1000 ./hash4.txt ./hash.hcmask --potfile-disable

./hashcat.bin -a 3 -w 3 -m 1000 ./hash5.txt ./hash.hcmask --potfile-disable

So conclusion
We can crack password it is all about hardware. As you can imaging the mask file can get really large.
When we use mask file we get all the hashes cracked.
85DEEEC2D12F917783B689AE94990716
6E21570B203F2D9AE145932A8FF2D3E9
985F751BFDC910F62C8BBE48C1E86D1A
2FD0F98F072F7085DF0BB31D9C9FA4EA
833DF42D998CF3A345796D5F69D82015
Cracked
Cracked
Cracked
Cracked
Cracked
Another example if you know that the password policy is 8 characters and min 1 lower 1 upper 1 digit and 1 special. You can create a mask file like this:
python policygen.py --minlength 8 --maxlength 8 --minlower 1 --minupper 1 --mindigit 1 --minspecial 1 -o hash.hcmask
Or you can create a mask file from a password list that you already have:
python statsgen.py rockyou.txt -o rockyou.masks
Thanx for today!
//Roger

Leave a comment