Hi all out there.
It is time to take a look at sn1per. A tool that automate opensource stuff for us.
As always we start with the steps
- Install some os in my kase running kali
- Get the docker file
- Build
- Run
sn1per installation
wget https://raw.githubusercontent.com/1N3/Sn1per/master/Dockerfile

docker build -t sn1per .
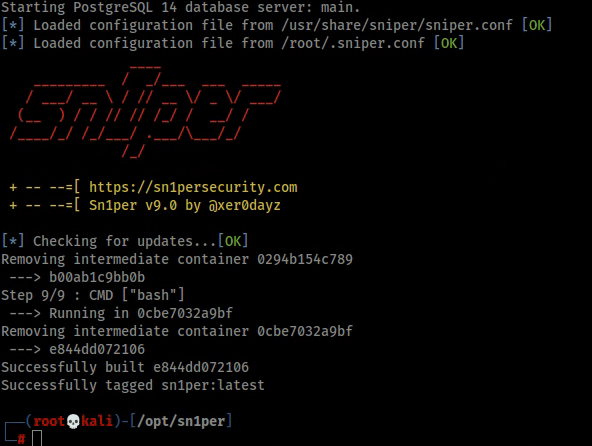
Below is gonna take some time to complete go get some coffe.
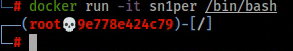
Start up sn1per docker container
docker run -it sn1per /bin/bash
Install vim and dnsutil
In my installation these where missing, so I installed them.
apt-get install vim
apt-get install dnsutils

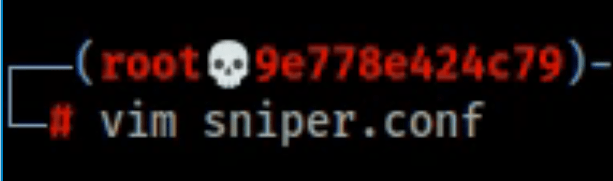
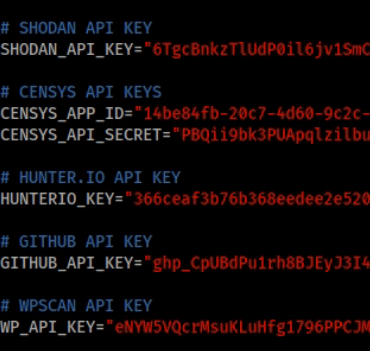
Add api plugins
When I did this I edit /root/.sniper.conf file
What does this application automate for us?
- DNS
- Finding HTTP Headers
- Tcp port scan
- Web fingerprinting
- Site Links
- Checking for WAF
- Gathering HTTP info
- Checking ssl certificate
- Checking for ssl insecure stuff
- Webspider
- Wayback machine
- Looking for extensions
- Static snalysis
- XSS analysis
- SSRF analysis
- Redirect analysis
- RCE analysis
- IDOR analysis
- SQL analysis
- LFI analysis
- SSTI analysis
- Downloading java script files
- Javascript Links
- Linkfinder
- Common File/Directory brute force
- Dirsearch
- Smuggler HTTP http reqest smuggling
- Nuclei scan
- NMAP scans
- Osint
- more stuff that you will need to find out for your self
Run it
Read the documentation but the run command for me was:
./sniper -t domain.name

When I tried it, I did make the web server crash and the webserver lost the connection to the database. 😦
So be careful what you run against.
Something to think about when doing a scan.
If you run against a machine with fail2ban installed, you will get banned.
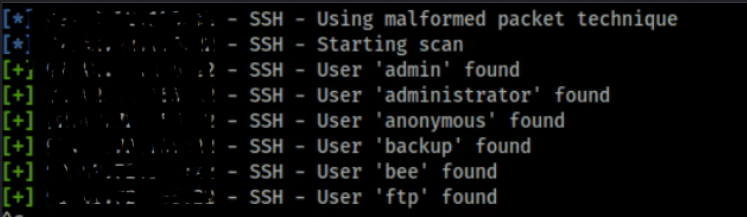
There where false postive also when I ran it on a machine that had ssh on it.
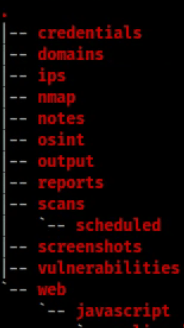
When the scannings is done, you will get a directory structure that shows your findings.
My thoughts
Is there another way, without this. Yes there is, you can run every tool manually. Or make you own scripts to automate stuff. Then you will have more control, but you will burn a couple of hours on that. But as a educational purpose, why not create a script by your self?
But they are doing a great job putting it together. I hope to get the funds to buy the pro version!
After that I hope get a post up compering the free versions vs paid version!
Here are some useful information that I got when contacting them
To learn more about Sn1per Professional, please review our sn1persecurity.com website, especially our Blog Section: https://sn1persecurity.com/wordpress/blog/
Youtube:
https://www.youtube.com/c/Sn1perSecurity
Pro Bundle in store: https://sn1persecurity.com/wordpress/product/sn1per-professional-v9-0-command-execution-add-on-v2/
All Sn1per Community questions/concerns are handled via GitHub. Be sure to review the wiki for basic assistance/troubleshooting. In particular you’ll want to check out ‘Sn1per Configuration Options’
https://github.com/1N3/Sn1per/wiki
That was all for now!
Keep hacking!
//Roger

Leave a comment