Intro
Hi all!
My plan is that under 2022 to take OSCP and PNPT exam. To get the full picture we start from the beginning. Why do I post this? Share knowledge is the simple answer, and I am getting old so I need to document everything I do. I think this is a good way to do it. And I do not want to wait 1 year to share my stuff. So my plan is that I do updates know and then when something happens. Think if I do not pass any of the exam, so what. The sun will come up tomorrow anyway, I hope!
The outcome of somethings can change, I write as I go. But after a journey like this, things can change.
And I hope I get in contact with someone that are in the same boat as me. Create a team on Try Hack Me or Hack The Box? I am open to almost anything! 🙂
I have a ordinary day job that not always include in security stuff, so a lot of evenings and nights are behind what I am today.
I could create 2 post one for each exam path, sure. I do not want to “compare” who has the best product, but for me it is just that the goal here is to pass them both in the same time frame and also get some tips and tricks out there if someone plan to choose one of these exams.
OSCP – https://www.offensive-security.com/pre-reg/
This is the first course that I have taken from Offensive Security, and I hope not the last. Support for the course is done thru Discord. Any troubles with labs in PEN-200 and exam can be done thru https://chat.offensive-security.com/. I did put in some questions in discord, sometimes the community answer fast sometimes not so fast. I am a person that like to do things in order, but in this case if you are stuck on a questions. Put in a questions in Discord and move one. You can do that question later.
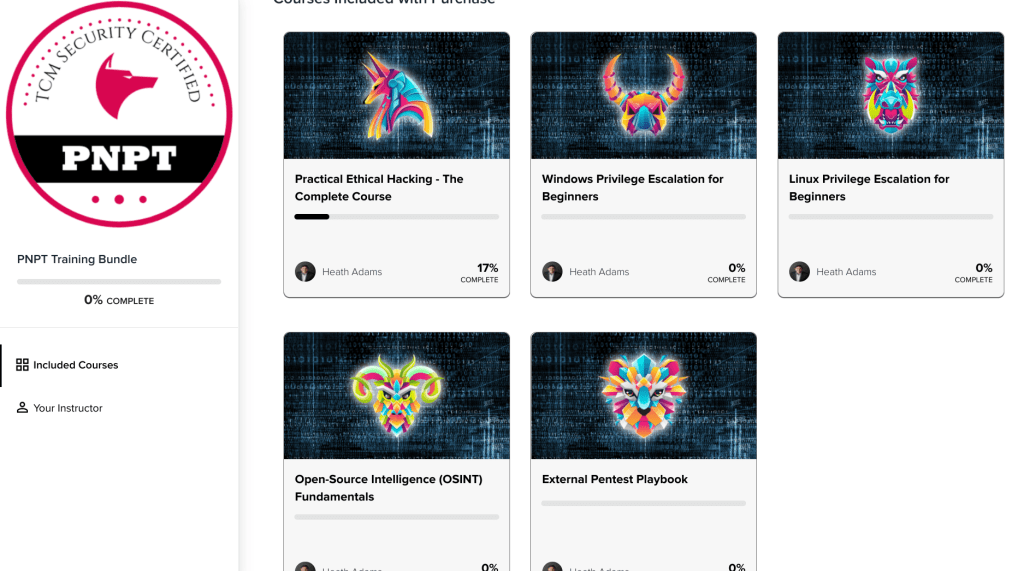
PNPT – https://certifications.tcm-sec.com/pnpt/
I have done TCM courses before he opened his own academy. But my plan is to go thru them again. There are some new stuff like OSINT and Pentest playbook.
Also between everything else, I listen to a lot of security podocast. So I want to fill my life with security to get in 100% in this. Eat, Drink, Sleep, Shit Security!
Some of my podcast that I listen to.
https://blogg.invid.eu/2022/01/06/podcasts-you-need-to-take-a-look-at-darknetdiaries-danielmiessler-inteltechniques-infosecedu-7minsec-coalfirelabs-netspi-breachsense-trustedsec-riskybusiness-thehackscast%ef%bf%bcnakedsec/
Special thanx to https://www.blackhillsinfosec.com/ they are great! Special thanks to John Strand, not the model for being such an inspiration.
https://twitter.com/BHinfoSecurity
https://www.linkedin.com/company/black-hills-information-security/
Below what got me on fire!
https://www.blackhillsinfosec.com/webcast-5-year-plan-infosec/
https://www.blackhillsinfosec.com/webcast-john-strands-5-year-plan-into-infosec-part-2/
The arrangement on this post is like this
- Steps that I am taking
- Course information
- Try HackMe rooms for PNPT and PEN-200
- Timeschedule of the course
- Finnsihing note on the course
- Exam thoughts if I ever pass
- Diary
- Spreadsheet of my time
Have a great 2022!
Steps to get the PNPT and OSCP (I hope this is enough)
PNPT – Practical Ethical Hacking
PNPT – Windows Privilege Escalation for Beginners
PNPT – Linux Privilege Escalation for Beginners
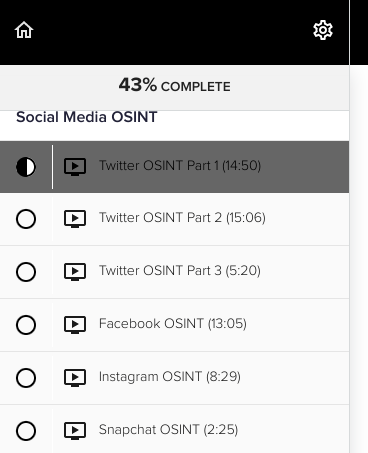
PNPT – Open-Source Intelligence (OSINT) Fundamentals
PNPT – External Pentest Playbook
EXTRA – Python Python 101
OFFENSIVE – PEN100
OFFENSIVE – WEB-100
OFFENSIVE – SOC-100
OFFENSIVE – PEN-103
OFFENSIVE – PEN-210
OFFENSIVE – PEN-200
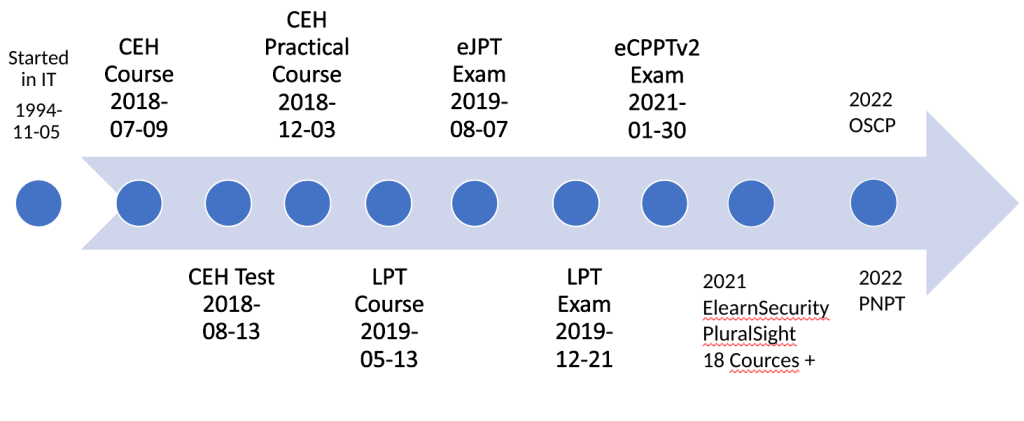
Timeline 1994-2022
To get some idea behind how I came to this place, here is my timeline. Security is in everything. But I started my real journey in security in 2018.
Here is also a reference about my journey, all the courses and certification along the way.
https://blogg.invid.eu/2022/01/06/courses-and-certifications-that-i-have-taking-over-the-years-knowledge-is-the-key/
2018-2021
PNPT
This was pure joy to go thru TCM Security course! I would recommend this to any in IT. The delivery of the course is great and have nothing to complain about.
Timeschedule
- Practical Ethical Hacking – The Complete Course 25 hours.
- Beginner and do all the labs 30-100 hours
- Windows Privilege Escalation for Beginners 7 hours.
- Beginner and do all the labs 7 – 40 hours
- Linux Privilege Escalation for Beginners 7h.
- Beginner and do all the labs 7 – 40 hours
- Open-Source Intelligence (OSINT) Fundamentals
- Beginner and do all the labs 9-15 hours
- External Pentest Playbook 3-5 hours
- Beginner and do all the labs hour
Try Hack Me Rooms for PNPT
Windows PrivEsc Arena
Linux PrivEsc Arena
Attacktive Directory
OhSINT
Vulnversity
Ignite
Mr Robot CTF
Finished PNPT Course 2022-01-12
Perfect course for beginners or advanced IT people. A must to get started or get refreshed in knowledge.
Exam
Coming….I hope
PEN-100
Because I did buy 1 year of subscription I also got access to this.
This is Linux / Windows / Networking fundamentals education with labs. If you know Linux / Windows before this will be an easy one, but it is always good with repetition. So I will go thru that first.
After a couple of weeks into pen-100 I read something on the discord that everybody schould know.
From discord
—START—
Thanks for reaching out, I know that trying to solve something that you don’t know how to solve yet can be frustrating. Let me preface this with saying that there may indeed be material that we can clarify or add to make some of the exercises more evident, and to the extent that we need to do so we will – we use the rate of submission on questions to help us determine what new content we need to add, where to add hints and where to make wording less ambiguous – so we greatly appreciate your
That all said, let’s dive into the question a little bit. Part of the purpose of the PEN-100 material is to quickly become more comfortable with the “I dont know what to do next” feeling. As you elegantly point out, shooting an azimuth is hard and its frustrating not knowing what to do. Unfortunately (of fortunately depending on your perspective) security (and especially offensive/red/attacking security) is, in our view always an exercise in uncertainty. There will always be something that you don’t know, because if there weren’t then security would be easy and there’d be no need for pentesters in the first place! (This is a bit of a straw man and I can delve deeper into what I mean here if you wish.) For now I just want to make the points that a) dealing with uncertainty is a necessity, and b) making it easier or at least more palatable is part of the point of PEN-100 in particular and 100 level content in general.
—END—
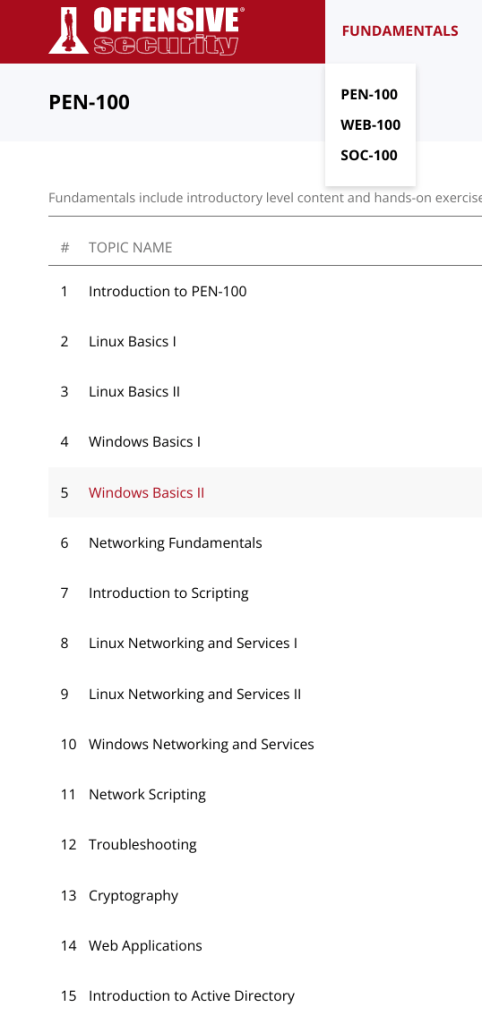
Timeschedule
I think the hours have been calculated if you are a beginner.
So total time in this PEN-100 is 151 hours or 8 hours per day in 19 days.
Update 2022-03-10
Add more 10 hours for the new chapter nr 17 Proxy!
Introduction to PEN-100 3h
Linux Basics I 10 h
Linux Basics II 11 h
Windows Basics I 8 h
Windows Basics II 11 h
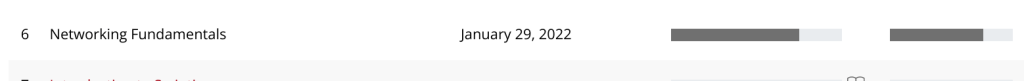
Networking Fundamentals 11 h
Introduction to Scripting 11 h
Linux Networking and Services I 16,5 h
Linux Networking and Services II 11 h
Windows Networking and Services 10 h
Network Scripting 11 h
Troubleshooting 9,5 h
Cryptography 11 h
Web Applications 11 h
Introduction to Active Directory 6 h
Introduction to Proxies 10 h
Finished PEN-100 2022-02-27
Really nice course, some parts for me was hard and some part was easy. The coding part was for me really hard, because I suck at coding. But I learned alot and I can recommend this to everyone.
Exam thoughts
No exam for this course
WEB-100
I have been waiting to do this one. But some chapters are the same as in PEN-100, so you will get some for “free”.
Do not think the course really holds the level I want. But I also understand that it is difficult to teach this as a web fundamental course. Since 40-50% was already ready when you had done PEN-100 was probably less good. Since I’m a noob at this, one would like explanations of things. But that’s probably the thing, find out for yourself. Try Harder 🙂
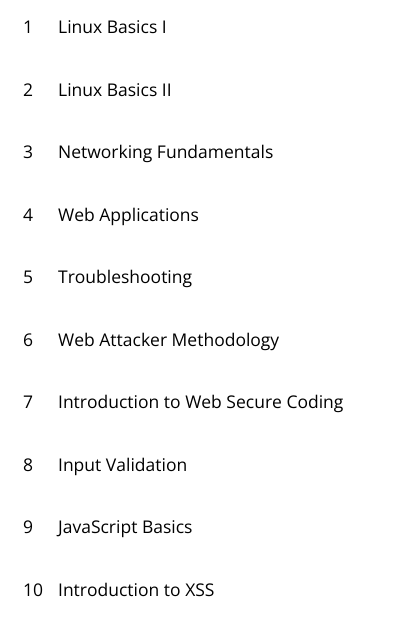
Timeschedule
So total time in this WEB-100 is 81 hours or 8 hours per day in 8 days. But as I said before some chapters are the same as PEN-100. So if you have done PEN-100 before then you “only” have 28,5 hours.
Linux Basics I 10 h
Linux Basics II 11 h
Networking Fundamentals 11 h
Web Applications 11 h
Troubleshooting 9,5 h
Web Attacker Methodology 11 h
Introduction to Web Secure Coding 4 h
Input Validation 4 h
JavaScript Basics 4,5 h
Introduction to XSS 5 h
Almost Finished WEB-100 2022-03-04
I really thoght that this part would be better. But as I write more about this further down I will says this. This is hard and it will be easier if you have coding experince. Some of the questions are “stupid” and so is the answer. Sometimes, it will not take the correct answer (bug). It will get frustrated, but just move on. I will do the few questions left in this part soon. But knowledge is knowledge. Just go thru with it and take notes.
Exam thoughts
No exam for this course
SOC-100
Same as WEB-100 some chapters are the same as in PEN-100, so you will get some for “free”. Below is the different Chapters. And it is alot of reading in this course!

Timeschedule
So total time in this WEB-100 is 141,4 hours or 8 hours per day in 17 days. But as I said before some chapters are the same as PEN-100. So if you have done PEN-100 before then you “only” 37,5 hours to burn infront of a screen.
Linux Basics I 10 h
Linux Basics II 11 h
Windows Basics I 8 h
Windows Basics II 11 h
Networking Fundamentals 11 h
Linux Networking and Services I 16,5 h
Linux Networking and Services II 11 h
Windows Networking and Services 10 h
Enterprise Network Architecture 3,5 h
SOC Management Processes 4,5 h
Toubleshooting 9,5 h
Windows Registry 9,5 h
Introduction to Active Directory 6 h
Introduction to Incident Response 6h
Windows Logging 10 h
Introduction to Vulnerability Tracking 4 h
Finished SOC-100 2022-03-08
This was alot of reading, a lot. The information in this course was very extensive. I would love to be able to download this and use it as a reference. I learned alot in this course, how shall we implement a real SOC from beginning to end. Really nice, even if it has really nothing to do with PEN-200 (OSCP). But knowledge is easy to have on our schoulder. 🙂
Exam thoughts
No exam for this course
PEN-103
This course is free to do. Below is the different Chapters. This will be alot of reading in this course also. There is no question to answer here. But if you are new to Kali Linux this is a realy good beginners guide to Kali Linux. Lets dig in!
Even if I have used Linux as workstation for many years there is new information in this course for everyone I think. The bad thing here is that I can not download and print out, you need to access this online and read it. You can also get the book and print this out.
https://commons.wikimedia.org/wiki/File:Kali-Linux-Revealed-2021-edition.pdf

Timeschedule
I do not have a timeline in this course. First there is no approx time schedule in the course and second I have not finnished it yet. So I will put in the hours here when I am done.
Finished PEN-103 2022–
Coming…
Exam thoughts
Coming i hope….
PEN-210
Now on to some wireless hacking. I really do not know if this can be applied in 2022, but either way it is good to know history before the future (newer technology). This course is really technical and have text and Video. It is higly recommended to have a Kali laptop and try the stuff that are in the course. It make me learn faster anyway. Below is the different chapters in the course. This course can not be downloaded and read offline. So I did copy and past in to joplin, so I can read it offline, this will take around 6 hours to do that at least for me it did. No I am not allowed to share that, do not even ask 🙂

Timeschedule
I do not have a timeline in this course. First there is no approx time schedule in the course and second I have not finnished it yet. So I will put in the hours here when I am done.
Exam thoughts
Coming i hope….
PEN-200
To get this certification is one of the goals in 2022. This course is the last step in my journey this time. The exam for this course is 24 hours, so you need to get prepaired for this. In the course there is a alot of information to get in shape for this. Read it!
I also plan to get physical in parallell with this course. Do some PDF/Video and hacking some machines. I can not wait. 🙂
Try Hack Me Rooms for PEN-200
Brainpan 1
Holo
Windows PrivEsc Arena
Linux PrivEsc Arena
Attacktive Directory
OhSINT
Vulnversity
IgniteMr Robot CTF
Read all the documentation on the help pages. https://help.offensive-security.com/
Here is the answers to all you questions regarding labs and exam and everything else you need to know!
General
If you have the money, sign up for TryHackme and HackTheBox
Of you don’t have the money, do not sign up for these do the free stuff on these plattforms.
The plan for learning this can be explained in words. Read, Listen, Exercises, Labs and Finally exam. This picture is taken from the Offensive Security site. But I will apply this in any test that I will take.

Create your own pentest machine that you will operate from. So you get in the right mod when doing the stuff. Then you will know where the tools are and how they are configured. I use a virtual machine so I can take backups on regular basis.
You can download the content 1 time and one time only. That was decided from Offensive Security, before there was no download at all.
There are 3 parts in this course, Reading, Video and Labs.
I did not find any time schedule in this course but here is the different topics.
Modules PDF / Online Reading
Penetration Testing with Kali Linux: General Course Information
Getting Comfortable with Kali Linux
Command Line Fun
Practical Tools
Bash Scripting
Passive Information Gathering
Active Information Gathering
Vulnerability Scanning
Web Application Attacks
Introduction to Buffer Overflows
Windows Buffer Overflows
Linux Buffer Overflows
Client-Side Attacks
Locating Public Exploits
Fixing Exploits
File Transfers
Antivirus Evasion
Privilege Escalation
Password Attacks
Port Redirection and Tunneling
Active Directory Attacks
The Metasploit Framework
PowerShell Empire
Assembling the Pieces: Penetration Test Breakdown
Trying Harder: The Labs
Modules Video
GETTING COMFORTABLE WITH KALI LINUX
Booting Up Kali Linux
The Kali Menu
Kali Documentation
Finding Your Way Around Kali
Managing Kali Linux Services
Searching, Installing, and Removing Tools
Wrapping Up
COMMAND LINE FUN
The Bash Environment
Piping and Redirection
Text Searching and Manipulation
Editing Files from the Command Line
Comparing Files
Managing Processes
File and Command Monitoring
Downloading Files
Customizing the Bash Environment
Wrapping Up
PRACTICAL TOOLS
Netcat
Socat
PowerShell and Powercat
Wireshark
Tcpdump
BASH SCRIPTING
Intro to Bash Scripting
Variables
If, Else, Elif Statements
Boolean Logical Operations
Loops
Functions
Practical Examples
PASSIVE INFORMATION GATHERING
Website Recon
Whois Enumeration
Google Hacking
Netcraft
Recon-ng
Open-Source Code
Shodan
Security Headers Scanner
SSL Server Test
Pastebin
User Information Gathering
Social Media Tools
Stack Overflow
Information Gathering Frameworks
Wrapping Up
ACTIVE INFORMATION GATHERING
DNS Enumeration
Port Scanning
SMB Enumeration
NFS Enumeration
SMTP Enumeration
SNMP Enumeration
Wrapping Up
VULNERABILITY SCANNING
Vulnerability Scanning Overview and Considerations
Vulnerability Scanning with Nessus
Vulnerability Scanning with Nmap
Wrapping Up
WEB APPLICATION ATTACKS
Web Application Assessment Methodology
Web Application Enumeration
Web Application Assessment Tools
Exploiting Web-based Vulnerabilities
Exploiting Admin Consoles
Cross-Site Scripting (XSS)
Directory Traversal Vulnerabilities
File Inclusion Vulnerabilities
SQL Injection
Wrapping Up
INTRODUCTION TO BUFFER OVERFLOWS
Introduction to the x86 Architecture
Buffer Overflow Walkthrough
WINDOWS BUFFER OVERFLOWS
iscovering the Vulnerability
Win32 Buffer Overflow Exploitation
Wrapping Up
LINUX BUFFER OVERFLOWS
About DEP, ASLR, and Canaries
Replicating the Crash
Controlling EIP
Locating Space for Our Shellcode
Checking for Bad Characters
Finding a Return Address
Getting a Shell
Wrapping Up
CLIENT-SIDE ATTACKS
Know Your Target
Leveraging HTML Applications
Exploiting Microsoft Office
Wrapping Up
LOCATING PUBLIC EXPLOITS
A Word of Caution
Searching for Exploits
Putting It All Together
Wrapping Up
FIXING EXPLOITS
Fixing Memory Corruption Exploits
Fixing Web Exploits
Wrapping Up
FILE TRANSFERS
Considerations and Preparations
Transferring Files with Windows Hosts
Wrapping Up
ANTIVIRUS EVASION
What is Antivirus Software
Methods of Detecting Malicious Code
Bypassing Antivirus Detection
Wrapping Up
PRIVILEGE ESCALATION
Information Gathering
Windows Privilege Escalation Examples
Linux Privilege Escalation Examples
Wrapping Up
PASSWORD ATTACKS
Wordlists
Brute Force Wordlists
Common Network Service Attack Methods
Leveraging Password Hashes
Wrapping Up
PORT REDIRECTION AND TUNNELING
Port Forwarding
SSH Tunneling
PLINK.exe
NETSH
HTTPTunnel-ing Through Deep Packet Inspection
Wrapping Up
ACTIVE DIRECTORY ATTACKS
Active Directory Theory
Active Directory Enumeration
Active Directory Authentication
Active Directory Lateral Movement
Active Directory Persistence
Wrapping Up
THE METASPLOIT FRAMEWORK
Metasploit User Interfaces and Setup
Exploit Modules
Metasploit Payloads
Building Our Own MSF Module
Post-Exploitation with Metasploit
Metasploit Automation
Wrapping Up
POWERSHELL EMPIRE
Installation, Setup, and Usage
PowerShell Modules
Switching Between Empire and Metasploit
Wrapping Up
ASSEMBLING THE PIECES: PENETRATION TEST BREAKDOWN
Public Network Enumeration
Targeting the Web Application
Targeting the Database
Deeper Enumeration of the Web Application Server
Targeting the Database Again
Targeting Poultry
Internal Network Enumeration
Targeting the Jenkins Server
Targeting the Domain Controller
Wrapping Up
Timeschedule
Finished PEN-200 2022–
Coming…
Exam thoughts
Coming i hope….
LETS BEGIN THIS JOURNEY
We start with the setup.
Using Kali as the main machine (vm).
What do I take notes with = Using Joplin
https://joplinapp.org/
What am I using for pentesting management platform = Reconmap
https://reconmap.org/
Why?
Because I want to, and it is free.
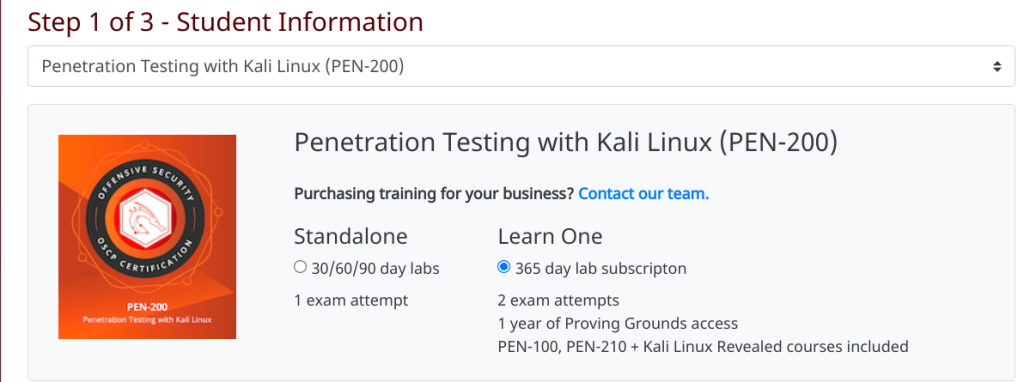
2021-12-30
I registered at Offensive Security Site for 1 year off PEN-200 access. The price at the moment was 1999$ for 1 year.
2021-12-30
Received confirmation of payment

2021-12-30
I also registered for the PNTP exam. The price for that at the moment was 399$. It was really easy to register here and get account.
2022-01-02
Because of holiday I waited 2 days to receive below email. To verify my identity.

2021-01-02
The start of this blogg post and some rest. I will begin the hard work on 2021-01-03
2021-01-03
We start the day with videos from TCM. And at the same time I got email from Offensive Security to access my stuff.
Received email from Offensive Security that I can now start my education!
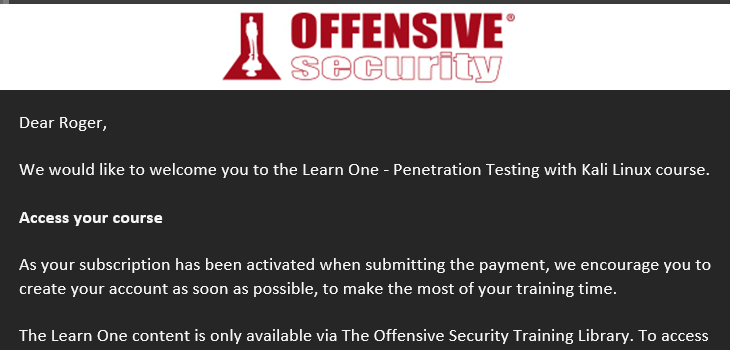
Because I bought the 1 year PEN-200 I also did get PEN-100, WEB-100 and SOC-100

This was a long day almost went thru Practical Ethical Hacking – The Complete Course…Only OWASP left.
I have done this course before, so some chapter I could skip. But still it was 15 hour day. Normal this takes more than 25 hours.

2022-01-04
Today I also joined the Offensive Security Discord channel. Went thru the https://help.offensive-security.com/ pages to see what I needed to know regarding the OSCP Labs and exam.
But also completed the Practical Ethical Hacking – The Complete Course!

2022-01-05
Today I went thru the Windows Privilege Escalation for Beginners. I did not do the labs. I have done this courses before when these were on udemy.
2022-01-06
Today I went thru the Linux Privilege Escalation for Beginners. I did not do the labs. I have done this courses before when these were on udemy. I also stared the OSINT course, this one was new for me! It is time for some wine now peace out!
Open-Source Intelligence (OSINT) Fundamentals

2022-01-07
I think I will start with an hangover…..but we will see…. 🙂
Today was a “small” day” only 30% of the osint course, Back to the beers!
2022-01-08
Free today. Party time! Just some OSINT in the bottle.
2022-01-09
Corona time in the family, so now it is lockdown. But did some hours in the OSINT course.
2022-01-10
Finished the OSINT course and started the External Pentest playbook from TCM-SEC.

2022-01-11
Today it is time to do the Network Threat Hunting Training from ACTIVE COUNTERMEASURES, 6 hours long.

2022-01-12
Today I finished The PNPT training bundle. This is really good and is fair with the price. TCM-Security as done a really good job with the platform. Resume the course when your PC hangs. Simple login tog the plattform. I have done the three first courses before, but it is always good with repetition.

After TCM-Security is finished now it’s off to Offensive security courses. Since I bought 1 year with Offensive Security, I also get access to the PEN-100 WEB-100 SOC-100. So why not start with them?

I know that I need to schedule the PNPT exam….But lets go thru the Offensive Security courses first.
2022-01-13
It was a couple of hours PEN-100 only. Had a long day at work.
2022-01-14
Today it was all PEN-100 for 2 hours. As I said before Covid in family……SUCK!

2022-01-15
Mental preparation….Free today
2022-01-16
6 hours of PEN-100 today. Did the Linux and first part of Windows. Even if you are heavy user of Linux and Windows you will learn something new, I promise.
2022-01-17
Need to put the PEN-100 aside for a couple of days. Something Santa brought this weekend from TCM Security was that you can get 7 day free trial on All-Access Pass. So I did sign up on that and started with Movement, Pivoting and Persistence. In this course you will see C2 like covenant, Metasploit, Phishing, Privilege Escalation and Password Spraying and a lot of more stuff. The first part of this course is about setting your own lab up and running. Great content from TCM Security and The Mayor! I did the course , but no labs. As I said before I will do the practical later.



After this it is time for some Python 101. I hope I will have time to do Python 101 and Python 201 during this week. But I will come back on that.

2022-01-18
I am so bad at this. Even 26 years in IT I was never a programmer and never will be. I feel like I am a newbie, and I am. Fuck Fuck Fuck…..36% of the course only. It is gonna be a long week! If I would do my childhood all over again I would start programming when I was 10.


2022-01-19
To much work today only 30 min of python today. Did also 2 1 hour webinars. One webinar was from Wild West Hackin’ Fest and going thru BurpSuite here is a link https://www.youtube.com/watch?v=-ZrqGaEJ740 Little tired, I hope for more energy tomorrow!
2022-01-20 -2022-01-23
Python Python 101 are finally finished! It has been a pain in the as this one. I am and never will be a coder, that is a fact! But this course did help me understand the basics and how much I admire coders. This course is 5,5 hours but it took me 9,5 hours to get thru! The teacher in this course was Riley Kidd also know as @247CTF


2022-01-24
Back to Offensive Security. Even if this is fundamental stuff it is a reminder that you can forget and you do not know everything.

2022-01-25
Work all Day and evening, then a webcast from @RedSiege. The best about these webcast from USA is the time difference….You can work all day and the webcast starts at 20.00 or 21.00.
2022-01-26
Today is was also alot of work, but I did manage to attend a Webinar today A master class om Offensive MSBuilld with Chris Truncer & Joe Leon. I also did 2 hours of PEN-100, Windows processes, Libaries and Registry. You can think it is basic, but a alot of stuff here you never always do. So it is a god course with labs.


2022-01-27
2 Hours of PEN-100 today finishing of Windows stuff. No off to networking stuff. I like the labs I learn faster when I can use my keyboard. I really long to complete these trainings theoretically so I can start with the real hands on labs.

2022-01-28
Finally I got use of my old CNE certification and Novell Netware course “Networking Technologies”. You can still find books about this
https://www.amazon.com/Networking-Technologies-Complete-McGraw-Hill-Communications/dp/0079123120
OSI is the shit!
Almost all done at the Networking stuff:
2022-01-29 and 2022-01-30
This weekend I did not have to many hours behind the computer, but I manage to get thru most of scripting module. Powershell I hope I finnish on Monday!

2022-01-31
No hacking today private shit
2022-02-01
No hacking today private shit
2022-02-02
I have now done the scripting part and now of to the the more “fun” stuff

2022-02-03
Beer
2022-02-04
More beer
2022-02-05
Even more beer
2022-02-06
Hangover
2022-02-07
2 hours today and did the first networking part.

2022-02-08
3 Hours of PEN-100. Linux networking and got starter with Windows Networking.

2022-02-09
No hacking to today but two webinars that was really good.
@PureStorage

And from @WWHackinfest

2022-02-10
Needed to work today….and tired
2022-02-11
Beer
2022-02-12
Beer
2022-02-13
No hacking today. But osint 50 pages of this really nice book

2022-02-14
Worst day in my path…python coding. 4,5 hours pure hell. I need to turn back the time 20 years and start coding. And still after 4,5 hour not done. This is gonna end bad.

2022-02-15
Today I FINALLY got thru the Networking Script part of PEN-100, and I must admit…I used BurpSuite for some exersices. I must go thru the hard school of coding. But I do not see the time for it right now. Solve the problem ahead coding or not. 6 hours with this. I am gonna dream of python tonight
Today it was also a 2 hour CTF challange from https://www.activecountermeasures.com/
I got 265 points of 265 points. I was not first, but I was not last either. 🙂

2022-02-16
Today was a webinar called “How Certifications Help You Find Great People for Your Security Team” from Wild West Hackin’ Fest. You can watch this on youtube if you like. https://www.youtube.com/watch?v=MgTh7JsxqxY
And I also did 4 hours of PEN-100 and almost finnished chapter 12 only 1 question left, yes you where right, pyhton coding…..my god. So I jumped over that question and did all other and the spent more time on the python script.

2022-02-17
Hi all, today I was home late from work so today no hacking, but I was able to attend a webinar from BlackHills. After watching that I decided to shutdown my computer(s) for today.
How to Burn Out in Infosec (and what to do next) with Corey Ham and Others https://www.youtube.com/watch?v=rfm0Mwq4_t4

2022-02-17
Taking a free day
2022-02-18
Beer
2022-02-19
Beer
2022-02-20
Mental preperation 🙂
2022-02-21
After a weekend off free time of computer I did the troubleshooting,nmap and 30% of the cryptography. These chapters was more my cup of tea! I can see the light in the tunnel! 6 hours…..

2022-02-22
Today i went thru the Cryptography module of PEN-100. Realy nice chapter.
If you have done HTB or Tryhackme this chapter would not take 11 hours. But for a first timer it will take this time. This is not easy to understand if you have not seen this before.

2022-02-23
Work all day and evening, sorry my hacker heart! But still I had time to go to the webinar WWHF | So, You Want to Build a Community in InfoSec ( https://www.youtube.com/watch?v=jFK_BxeOpDE )
2022-02-24
Not so much of PEN-100 today but some hours. Web Applications is really fun. I really enjoy this part. I am really impressive by people that are coding and creating web application. You really need to think about security everywhere.
I also did a webinar from Blackhills How to Detect and Repsond to Business Email. https://www.youtube.com/watch?v=OOGZRpju5B0


2022-02-25
Beer time…
2022-02-26
No computer today. I hope I have the power to do anything on Sunday!
2022-02-27
YEEEEAAAA, The PEN-100 course is done. The Web Application part was really fun. Active Directory part was really a beginners level. But not everyone has Active Directory knowledge.

Now time to jump in the WEB-100 there are some cross chapters from PEN-100 so I already have done some of the WEB-100

2022-02-28
Today was a fun day, loved this chapter with Web Attacker Methodogy. If I have the time I will also do the https://portswigger.net/web-security course and I do not think it is a bad thing when taking this journey. I also manage to do chapter 7 today. As I use to say, not a bad day today!

2022-03-01
This chapter was hard, a big remminder that scripting knowledge is important. I manage to do around 50% of this chapter today. 2 hours of work is better than 0. Need to sleep and empty regex strings out of my head!

2022-03-02
Long day at work and some ordinary work when I came home, but I did manage to enter a webinar from Active Countermeasures (Malware of The Day). Nice stuff as always.

I also manage to do some questions in the section Input Validation. But yeah I know I am not a coder, but some questions are stupid, or I am. I have not made up my mind yet.
ex. Microsoft Word and Excel files (.docx and .xlsx) are examples of what file format?

2022-03-03
Hard day today (in my world at least regarding my path). These chapters was hard for me.
But I did manage to do most of the question. I have some questions left that I will solve soon I think. As I said before coding is my achilles heel. But as I normally say, you need to learn how to crawl before running.

2022-03-04
Got really tired of myself today, I am bad at coding javascript. Javascript is eating my head! So I will go head and start the SOC-100 instead. It is the same with this course. Did you do the PEN-100 more than 50% is already done!

I manage to go thru 1, 5 chapter on this. If you compare PEN-100 or WEB-100 this is alot more reading to do. I like more hands on. But knowledge is knowledge!

2022-03-05
Beer time!
2022-03-06
Mental healthday!
2022-03-07
Did a few chapters on SOC-100 today so only 2 chapters left! Windows logging and vuln tracking left.

2022-03-08
Finishing SOC-100 puhhhh. In SOC-100 you learn to read English text. It is alot to read and go thru. Sure it was alot of reading, but you will learn alot in this course!

Also did some reading of PEN-103 course, the first 5 chapters.
2022-03-09
Today I started on PEN-103 and the first thing I did was to copy and past the material to Joplin so I can read it offline. So not so much hands on in security today. But I did 4 hour of Azure Workshop and 1 hour of webinar with Wild West Hackin Cast Side Channel Attack: Influencing Causality via Exploitation of the Choice Vendor | Ed Miro ( https://www.youtube.com/watch?v=ais6mNDH5Lk )
Offensive Security also updated the courses today 2 more chapter to do!



2022-03-10
Today it was a webinar with VMware vExpert and the content was Security EDR, NDR, NSX and much more. VMware has a great portfolio in the security space if you choose to go that way! Carbon Black is really nice. I did some updates in the documentation in Joplin for the Offensive Security journey!
I could not sleep so I did the new PEN-100 chapter 17 Proxy! Nice chapter, not so advanced. But as always everything is easy if you know it!


2022-03-11
Today it was alot of “ordinary” work so I only did the new chapter in SOC-100 “Snort” . I little tired today. Sleep and take on the hacking tomorrow!

2022-03-12
Beer time and Melodifestivalen. You can google that!
2022-03-13
Day off! No computer
2022-03-14
4 hours of going thru WEB-100, and documenting stuff from that course.
2022-03-15
Today I did a couple of hours in PEN-103, as I said before alot of reading.
And I started also a new course (not normal) but this was really nice, even if it not in my ballpark. I started GRC Analys Master Class
A Cybersecurity Primer
Compliance and Audit Work
Security Awareness Work
Cybersecurity Risk Work
Information Security Governance Work
Getting a GRC Analyst Job

I also did an 1 hour webinar from Active Countermeasures @ActiveCmeasures
https://www.activecountermeasures.com/events/month/
R.I.T.A. (Real Intelligence Threat Analytics) is an open-source framework for detecting command and control communication through network traffic analysis. But how exactly does RITA work? How is RITA able to find beacons and account for jitter?

2022-03-16
Today it was a webinar from WWHF | Hackin’ Cast | It’s Groundhog Day Again – The Cybersecurity Loop | Stephen Spence. https://www.youtube.com/watch?v=YMjqWOc_k-M
Did also finnsihed the GRC Analys Master Class course also.


2022-03-17
Today was a realy nice webinar from BHIS. Watch it on youtube tip of the day!

https://www.youtube.com/watch?v=62hps0XZkN8
2022-03-18
Beer time!
2022-03-19
Mental recovery
2022-03-20
Mental recovery
2022-03-21
PEN-103 for 4 hours today. Not much to say, a lot of reading and documenting the course.
And also 1 hour webinar with Black Hills Information Security
https://www.youtube.com/watch?v=uzbzHDe3mvQ

2022-03-22
My day job work took overhand and no study today!
2022-03-23
Strange evening today, I sleept for 10 hours I must be tired. But I did manage to stay awake for Wild West Hackin Cast webinar on Burpsuite

2022-03-24
Recover time.
2022-03-25
Recover time.
2022-03-26
Recover time.
2022-03-27
Recover time. And some work.
2022-03-28
Today I did make a decision to start the PEN-200 course. So we say goodbye to PEN-100,SOC-100, SOC-100, PEN-103 and PEN-203 for now. I has been almost 200 hours with alot of reading and get in the mood for PEN-200. But now the the real stuff begins. I have now almost 9 month left for study for the PNPT and PEN-200 exam! I hope this will be enough.
I will start to go thru the video. Then then the PDF with the labs. So I manage to do 3 chapters of video today only 22 left!

2022-03-29
No hacking today, needed to attend my homelab today. Setting up gophish and some other web services.
2022-03-30
Today It was workagain, and no hacking. But I manage to attend 2 webinars today.
One from Wild West Hackin cast: It’s Always Something: Creating a Strategic Vulnerability Response Plan with Joe Pierini, Daniel Brown, and Patrick
The other one was from Active Countermeasures: Applying The Threat Hunter’s Runbook With the great Chris Brenton!

2022-03-31 – 2022-04-10
Work – Life – Work – Life and some beers!
2022-04-11
This evening it was cloud 100% 8 hours of AWS training and 8 hours of work a long day.
I hope I can go back to some hacking soon!

2022-04-12
Work, Work, Work and no hacking!
2022-04-13
Work, Work, Work and no hacking!
2022-04-14
Finally got started again! Did 5 hours of training PEN-200. So I manage to get thru below chapters of videos. Next chapter after this day is Buffer Overflows. I can not wait. 🙂

2022-04-15
Basic knowledge of Buffer Overflow chapter is done. Here we went thru how,why a application can be abused by an attacker. Also intriduction to step by steb to abuse an application with ImmunityDebuger. The PEN-200 course is good, but this is hard if you never worked with this before. There are easier way to learn this, for example The Cyber Mentor free stuff on youtube!


2022-04-16
Mental Recovery 🙂
2022-04-17
Mental Recovery 🙂
2022-04-18
Mental Recovery 🙂
2022-04-19
After this weekend I manage to add 2 hours of PEN-100. “Only” ten chapters left of video. Then off to PDF and reading. I hope I can start the labs in june, so I have 6 month of labs and hands on!

2022-04-20
Today as always a-lot of work but manage to do 2 nice webinars. And 1 hour of PEN-200. The first weibinar was from Hackinfest and the second was from Spectorops and was about Bloodhound Enterprise. I did 1,5 chapter of the PEN-200, file transfer and halv Antivirus evasion. Need some sleep. I have 2 days of realy long workdays!
https://specterops.zoom.us/webinar/register/WN_9UZef0yUSQqR7Njqj2Cvbw


2022-04-21
Mental Recovery 🙂
2022-04-22
Mental Recovery 🙂
2022-04-23
Mental Recovery 🙂
2022-04-24
Mental Recovery 🙂
2022-04-25
A really long day today. 6 hours of PEN-200 today! Soon I will be done with the video and will start the labs. I can not wait. Almost 5 full chapters was watched today.

2022-04-26
Today I booked the PNPT exam in August. I hope I have time to go thru the courses 1 more time before the exam. I also manage to end the video part of the PEN-200 around 3 hours. So finally the begining of the labs and after 4 month of preperation and alot of reading and video it is time to get my hands dirty! After the Webinar I manage to do 1,5 chapter of execsices. Nice day!
Also manage to watch a webinar from Microsoft. Microsoft Defender for Cloud!



2022-04-27
Work and tired!
2022-04-28
5 Hours of PEN-200, report writing from the labs that I did. I manage to almost end chapter 3 with labs and questions. I plan also to hand in the lab report, in hope I get 10 points. And I need to practies to write the report fast.

2022-04-29
Mental Recovery 🙂
2022-04-30
Mental Recovery 🙂
2022-05-01
Mental Recovery 🙂
2022-05-02
Work…no hacking
2022-05-03
I got 3 hours of PEN-200 tonight. So I am now staring with chapter 4 next time I open my computer!
Reporting is fun 🙂 And if you going on discord in the PEN-200 channels. There are not just me that is confused 🙂
If you will go for the lab report and get the extra 10 points. Read the the infromation from Offesive Security.
Some sentences you need to know and understand:
To be performed on your own Kali and Windows 10 lab client machines – Reporting is not required for these exercises
To be performed with the Topic Exercises VMs under “Resources” – Reporting is not required for these exercises
To be performed on your own Kali and Windows 10 lab client machines – Reporting is required for these exercises
To be performed with the Topic Exercises VMs under “Resources” – Reporting is not required for these exercises
Lets start with practical tools! But not today. Now sleep.

2022-05-04
Mental Recovery 🙂
2022-05-05
Mental Recovery 🙂
2022-05-06
Mental Recovery 🙂
2022-05-07
Mental Recovery 🙂
2022-05-08
Mental Recovery 🙂
2022-05-09
Mental Recovery 🙂
2022-05-10
Mental Recovery 🙂
2022-05-11
Today it was time to listen to BHIS and Troy Wojewoda the conent was How DNS can be abused for Command & Control. Really nice webinar that you can watch on yotube.
https://www.youtube.com/watch?v=Ogj0iHJCxcI

2022-05-12
No hacking today but 5 hours of Vmware education. This time it was ondemand traning, also the first time trying thins from VMware. Optimize and Scale [V7] is the course name and the goal here is to get the VCP 2022.

2022-05-13
Mental Recovery 🙂
2022-05-15
Mental Recovery 🙂
2022-05-16
5 hours of Vmware education today.
2022-05-17
3 hours of Vmware education today.
2022-05-18
Mental Recovery 🙂
2022-05-19
4 hours of Vmware education today.
2022-05-20
Mental Recovery 🙂
2022-05-21
Mental Recovery 🙂
2022-05-22
Today (Sunday) it was time after a week of study for VCP 7 or VCP-DCV 2022.
And I passed!

Somee history regarding VMware certification
2022 Vmware Certified Professional 7
2017 VMware Certified Professional 6.5 – Data Center Virtualization
2016 VMware Certified Professional 6 – Data Center Virtualization
2011 VMware Certified Professional 5 – Data Center Virtualization
2010 VMware Certified Professional 4 – Data Center Virtualization
2010 VMware Certified Professional 3
vExpert 2022
vExpert 2021
vExpert 2020
vExpert 2019
2022-05-23
After a couple of weeks off hacking for different reasons I am back! We start of today with updating my pc with the VMs. This did take some time. But now my VM:s are up to date!
Kali-Org = Template
Kali-Hack = My machine that I do the labs from
Kali-Darknet = When I need to get information from strange sites 🙂
Kali-Nessus = If I need nessus sometimes I use this
Tailis = When I need to be anonymous 🙂
Osint = This greate machine is from https://inteltechniques.com/ book! Really nice stuff from Mr. Bazzell.

2022-05-24 – 2022-06-27
For different reasons I had a brake from this.
2022-06-27
Today after almost 2 month of hands of security training it is high time to begin.
We started slow with TCM live PNPT
First week is now done on this PNPT Live.
2022-06-27 —-> 2022-07-03
No hacking these days!
2022-07-04
Hi, back again!
Today I went thru PEN103 again, there was some new chapters there. I spent around 4 hours on this today! Bash and started Python…

2022-07-05
There is some new stuff that will help you passing the PEN-200 test. That is PWK-LIVE. It is live streaming on twitch but also accessible thru the Offensive portal.
So today I did first chapter in Pyhton Scripting, PEN-100 (new) and also went thru 4 streaming from the live event.


2022-07-06
Work today.
2022-07-07
12 hours of PEN-100, WEB-100 and SOC-100 to go thru new new content of these cources!
2022-07-08
Today it was time to test my PEN-100 skills 5 hour assessment. I need to say, I must work on my python skills! Thats for sure!
But never the less! I passed!

2022-07-09
Party time!
2022-07-10
Not so much work today, except patchning a lot of servers.
2022-07-11
Long day today 14 hours of PEN-103, wirless hacking. A new blogpost around wireless hacking is in progress.
Also did the PWK Live and TCM Live today



2022-07-12
8 hours of PEN-210 today. This is fun! I have now gone thru the material. This summer is gonna be alot of reading and go thru the material again!

2022-07-13 -2022-08-05
Vaccation and almost no computer at all.
2022-08-06
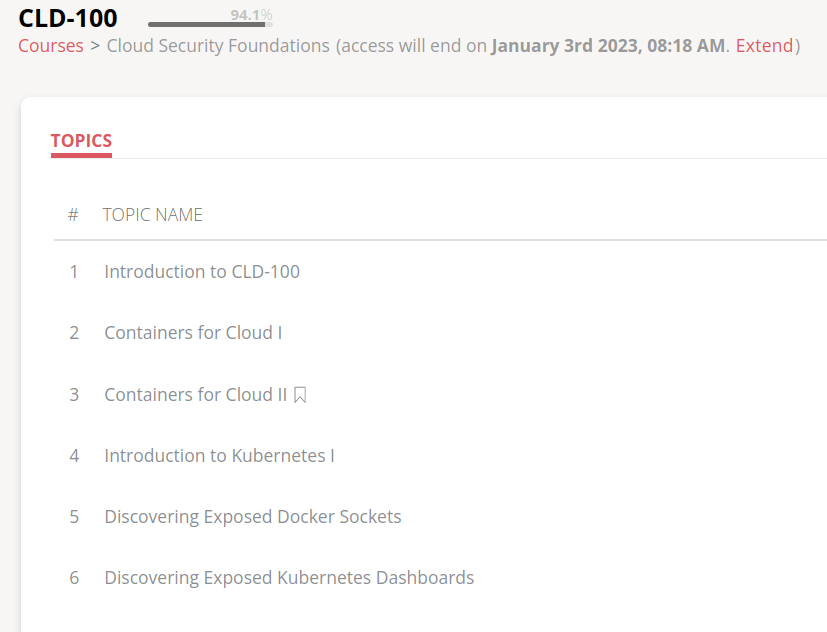
Today I spent 6 hours on CLD-100. The new course for Cloud Security Foundations. Docker, Podman and Kubernetes. This will be fun. I did almost 2 chapters. But stuck on two questions.

2022-08-07
Big day today! I have one week left of my vaccation. So I planned to do the OSWP exam today. 🙂
So the report for the exam is now in the cyberspace (Offensive-Security) and I hope I will retreive an answer in 10 working days.
If I manage to pass I will write a post what to think about and what I struggled with.
2022-08-08
Really fast, Offensive-Security says that it take up to 10 days to get the result. But I got it today. I am pleased to say that I passed! OSWP is done!
2022-08-09 – 2022-08-14
Last week of vaccation no computer.
2022-08-15
Today 6 hours of Offensive Security CLD-100. Great cource if you new to Docker and Kubernetes. The cource name is Cloud Security Foundation and is includen in my 1 yesr subscriotion on PEN-200.
2022-08-16
Today I registered to TCM cource Practical Malware Analysis & Triage. I have only done 30% of the cource today. But It seems great! I will write an update when it is done. I also finnsihed the CLD-100 cource. Shoutout to the teacher @HuskyHacksMK . Greate speed, voice and are really good to explain stuff.
Links from the teacher.
GitHub – https://github.com/HuskyHacks
Twitter – https://twitter.com/HuskyHacksMK
YouTube – https://www.youtube.com/channel/UCtJgZIyoZ0wIKEzctj_8pZQ
Blog – https://huskyhacks.dev


2022-08-17
Today it was 5 hour with Practical Malware Analysis & Triage. Almost done now.
2022-08-18
Today it was only 1,5 hour with Practical Malware Analysis & Triage. The I needed to work in the evning. Strange the goal was to do OSCP but when I read thru this I do anything else but that. That need to change!
2022-08-19
Nice, today I finished Practical Malware Analysis & Triage and even wrote a report that was a last task in that course. This course was great. And I do not want to have this undon. I learned alot! Great work @TCMSecurity and @HuskyHacksMK for this!

2022-08-20
Recovery!
2022-08-21
Today TCM-Security release another traning for a couple dollars. Nice! So now I ended up spending 10 hours on this Sunday with web apps! Web application security and testing!

2022-08-22
Today I finished the Practical Web Application Security and Testing. Really great course to get into pen testing of web application. Recommend this and it is cheap.

2022-08-23
After Practical Web Application Security and Testing there is a capstone (final task). Do a web penetrationtest and send in the report and get that graded by the course teacher @mttaggart. 4 hours on the pentest and report writning.
2022-08-24
Got some tips and tricks on the report that I needed to modify! Just waitning for @mtaggart for the final words.1 hour today on the report and template. I do not love reporting 🙂
2022-08-25
Report writning today also, spend a couple of hours trying to please @mtaggart 🙂 . His course is amazing. And the effort he putting in this are out of this world..
Also did 4 hours of PEN-LIVE and PNPT-LIVE
And 1 hour of Cyber Deception from Active Countermeasures! Great Stuff!



2022-08-26
Report writing for Mr. @mttaggart that is the teacher in Practical Web Application Security and Testing course. 1 hours on reporting.
2022-08-27
4 hours of report writing. This needs to be perfect for the customer. It is important part of vulnerability assessment or penetration test. Tips is to get report from the web and read them. Find a good one or combine different reports and find your structure. This is hard and it is easier if you can talk so someone that is good at this and you can ask question or send him/she your report for grading.
2022-08-28
50% of this book today. Really nice to have in your arsenal of tools. Can recommend this highly.
I always thought in this line of work RTFM meant Read The Fucking Manual but in this case it is Red Team Field Manual
I would love to have this in PDF or any digital format. But as always. Better to create one for your self and have this as reference. Go and get a copy for your self.
@redteamfieldman
https://www.amazon.com/dp/B0B7H8X3XY/
https://www.amazon.com/dp/B0B723YW48/
2022-08-29
PNPT-Live and PEN-LIVE Today 2,5 hours. Tired…need sleep now!


2022-08-30
Today it was time to Active Information Gathering from PEN-200 Course. Need to finish this fast. So I can begin the labs. But gut stuck for 5 hours on this one….Strange problems sometimes. Lets continue tomorrow!

2022-08-31
Hard day today. 7 hours of PEN-200, but troubleshooting for 5 hours. My fault but as I always say, do not give up! I was lucky today, wife was on a trip so I had all night for me, myself and PEN-200. 🙂
2 chapters done, could have been 4….

2022-09-01
5 hours of web today in PEN-200. Web is really fun. Used both Burp and ZAP

2022-09-02
No hacking today.
2022-09-03
Beer time
2022-09-04
Free day!
2022-09-05
Today it was time to get into PEN-200 again. Need to hurry this up. I think I am about 6-8 weeks behind my schedule. I thought I was having Aug-Dec to do the labs. But no no….What takes time is the reporting of the exercise. I can just do the flag stuff, but I think I learn more if I do the report and solve all the questions. I did manage to put in 5 hours in the course today. Stuck at web application attacks!

2022-09-06
7 hours of PEN-200. Finnsihed the Web part and started with Buffer Overflow. This I think gonna take some time. There is a lot of text to go thru. I would recommend other sites to learn Basic Buffer Overflow also. In the text part of PEN-200 it can be to much information, so nice to see someone talking about it.
Links:
https://www.youtube.com/watch?v=1S0aBV-Waeo
https://www.youtube.com/watch?v=ncBblM920jw

2022-09-07
Work…
2022-09-08
Work….
2022-09-09
5 hours of buffer overflow…my god what am I doing!

2022-09-10
10 hours of buffer overflow today. I can see the light in the tunnel, I think.

2022-09-11
No hacking today.
2022-09-12
Work.
2022-09-13
Went up 03:00 and drove to Stockholm. It is time for SEC-T and some education.
The first two days it is education time. Hacking Enterprises from in security. Two great guys from UK. They also do Password cracking 101 please watch this amazing course. And do not forget to follow Will Hunt @Stealthsploit and Owen Shearing @rebootuser.
This course fits like a glove!
https://in.security/technical-training/hacking-enterprises/

2022-09-13
Second day and sorry to say last day of Hacking Enterprises. This course will get 10 of 10. If you have the opportunity to attend this one do not miss this, you will not be disappointed. The lab environment is up to date, even Windows 11. I also got access to the lab for 2 weeks and access to a ctf environment.
Also it was 1 hour of Offensive Security Academy live stream this time.


2022-09-14
SEC-T First Day. This is a security conference in Stockholm. You can read all about it on there web page https://sec-t.org/.
Trammell Hudson
Hacking your dishwasher, or cloudless Home Connect appliances
Nicklas Keijser & Mattias Wåhlen
Russian Cyber Warfare in Ukraine
Jonathan Leitschuh
Scaling the Security Researcher to Eliminate OSS Vulnerabilities Once and For All
Eric Michaud & Tom Smith
Crypto Vuln Cornucopia From the archives of Team Kairos Enhanced Edition
Lucas Lundgren
Four Horsemen of Cyberwarfare: 4) Pestilence A Informational Vulnerability Turned into a Weapon of Mass Destruction.
Edwin van Andel
Popopizza How to break the Dutch police bodycams for fun and pizza
Olle Segerdahl
Why you dont need a Red Team test
Alve Björk
SEC-T Badge 2018 solution
Mikhail Shcherbakov
CodeQL in the hands of Bug Hunters
Tomas Rzepka
I C(M) what you got there
Skjortan
I will not buy this attendee list, it is scratched
Klondike
Lets fix the missing step in the academy to industry job pipeline
2022-09-15
SEC-T Second Day.
Martin Herfurt
Project TEMPA Demystifying Teslas Bluetooth Passive Entry System
Joseph Katsioloudes
Secure your code like NASA with Security as Code (SaC)
Yossi Sassi
When SysAdmin and Hacker unite: 21 One-Liners to make you convert from bash to Powershell
Anastasios Pingios
Nation-state actors No, its not all about phishing
Richard Johnson
eBPF ELFs JMPing Through the Windows
Mikko Hyppönen
Thinking About The Unthinkable Closing Keynote
2022-09-16 – 2022-09-18
Beer, Octoberfest
2022-09-19
1 hour of preparations, Preparing for the OSCP Exam with AD. All people out there this webinar is a must for doing OSCP!
2022-09-20
Buffer Overflow for 3 hours
And also 2 hours with In.Security and there free Catch Me If You Can – Seeing Red Through Blue

2022-09-21
1 hour off Offensive Security PEN-200

2022-09-22
2 hours of Cyber awareness from In Security. Great presentation, very important to get knowledge out there.Here is the link: https://in.security/technical-training/cyber-awareness/
And it is free!

2022-09-23
PNTP Exam
2022-09-24
PNPT Exam
2022-09-25
Report writing for the PNTP Exam. This was fun. I have sent in the 65 pages long report. Waiting to get feedback if I will pass and schedule a debriefing. If I do not get forward I hope for a nice feedback on why and what I can do better! Cross your fingers!
2022-09-26
Work today!
2022-09-27
PNPT Debreif today. I Passed! Read my review: https://blog.invid.eu/2022/09/27/pnpt-exam-review-and-how-did-i-approach-the-exam-delivered-by-tcmsecurity-thecybermentor-cybersecurity-hacking/
2022-09-28
No hacking today.
2022-09-29
2 hours of OSA – PEN – 200 today.

2022-09-30
No hacking today! Other studies hardware vendor stuff.
2022-10-01
I feel like I am 1,5 month behind my schedule. I think it is gonna be hard to pass OSCP in December. To little time. But we will see, Never Give Up can take you far on your journey.
Today it is gonna be some vendor stuff. Need to take a cert for the company.
2022-10-02
Vendor exam, FAILED…. You have to fail to succeed.
https://www.entrepreneur.com/growing-a-business/you-have-to-fail-if-you-want-to-succeed/413166
2022-10-03
Family time, my little princess turned 20! No hacking today!
2022-10-04
Vendor study….no hacking 😦
2022-10-05
Vendor study….no hacking 😦
2022-10-06
Vendor study….no hacking 😦
2022-10-07
Vendor study….no hacking 😦
2022-10-08
Party 🙂
2022-10-09
Party 🙂
2022-10-10
Vendor study….no hacking 😦
2022-10-11
Exam day for HPE0-V15….PASS PUHHH Now back to hacking PLEASE!
2022-10-12
Working…..Not with security 😦
2022-10-13
Work
2022-10-14
Party
2022-10-15
Party
2022-10-16
Free
2022-10-17
Finally some security
Priv Esc * 4

2022-10-18 -2022-10-31
Work No hacking!
2022-11-01
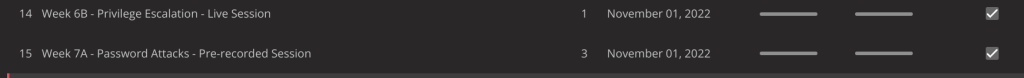
2 hours of video. Privilege Escalation and Password Attack! Finally.
2022-11-01 2022-11-05
Work, Work
2022-11-05 – 2022-11-11
Vmware Exolorer 2022 in Barcelona!

2022-11-12
Work and some rest
2022-11-13 – 2022-12-15
Work…..This is not good for OSCP exam this December! 😦
2022-12-16
Fixing my laptop, update vm:s and so on. Because it is time for OSCP on Saturday!
This is not gonna work, but I need to try, and my subscriptions ends in Decemeber. Not one lab machine is done and not even the full course. But I can not throw away the exam voucher.
2022-12-17
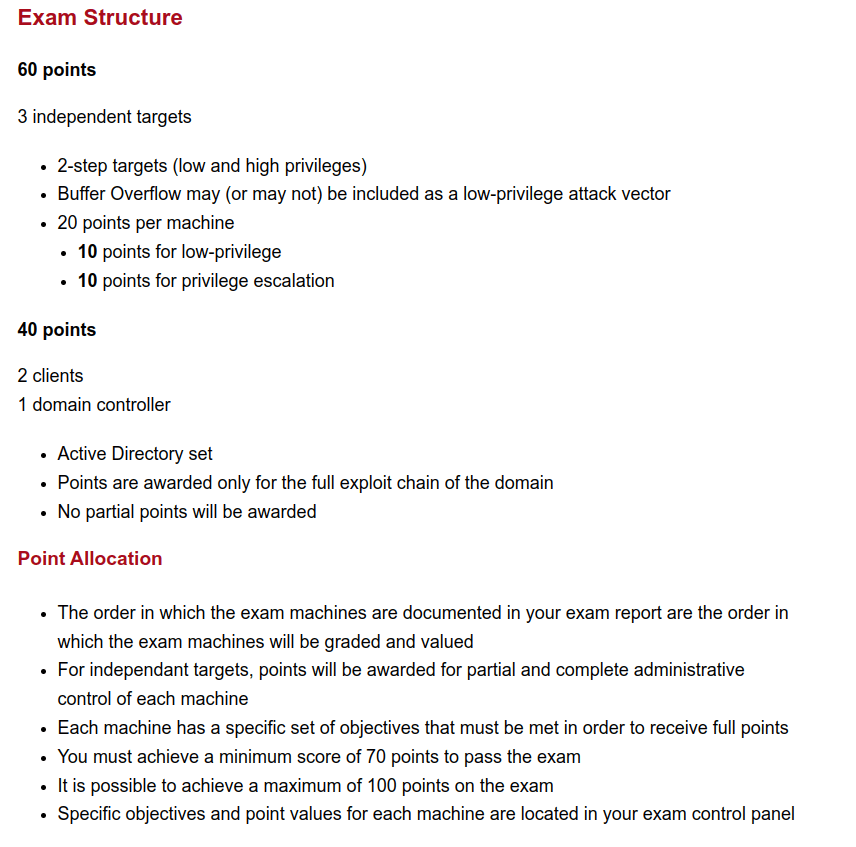
PEN-200 or OSCP exam today. Was able to use my work place for the test. I was schedule to start 10:00 CET, but there was some issue with the login portal for me, so I got started 15 min late. No problem for me….
As I told you before, I am not planing to pass the first time. To little study for that.
2022-12-18
24 hours later, without any sleep and infront of the computer all the time. 10 min in total for toilett 🙂
I did the AD stuff = 40 points
I did 1 independent machine = 20 point
50% of the time I was stuck on the 2 independent machines. Did not get anything from them, FUCK!
So in total 60 points and I needed 70, so only if I had done the labs and excersises I would be home.
But we need someting to do in 2023, right? 🙂
This is not an excuse, just the facts.
Course only 55%

Labs 0%

https://help.offensive-security.com/hc/en-us/articles/360040165632-OSCP-Exam-Guide
2022-12-19
You got mail!

2022-12-20 – 2022-12-31
Work and some free time.
2023-01-01
This years goals for me is OSCP in some way….
2023-01-02
Work
2023-01-03
Because my Offensive Security 1 year subscription ended today. I was planing to do the web100 assesment but when I logged in to the site I was to late. No access! Need to speak to my boss to buy 1 more year 🙂
But I schedule the KLCP exam for today and failed that also, this is not good. Can I have to much going on, need to focus more? No, lets burn some braincells and do Pentester Academy instead 🙂
Started today after work for 3 hours of Web Application course, did manage to go thru 35 videos in this course. There are 82 videos in this course. When I have done a little bit more work with this I can post what I think about Pentester Academy.

2023-01-04
Work today
2023-01-05
Work today
2023-01-06
Today is holiday so it is time for some bootcamp from PentesterAcademy
6 hours of webapp bootcamp

Here are some of the stuff that is in the bootcamp today


2023-01-07
Free from IT
2023-01-08
Free from IT
2023-01-09
Time to end this bootcamp!
Today it was 4 hours of traning including

2023-01-10
I started the Pentetser Academy Webapplication course 2023-01-03 now do some more videos.
2023-01-11
The end of the Web Application Pentesting course from Pentester Academy there was alot of content here and I have put some more infromation in my little hacker head. In this security world there is so many things you wanna know, is there a limit?
The content was like this:
HTTP Basics
Netcat Lab for HTTP 1.1 and 1.0
HTTP Methods and Verb Tampering
HTTP Method Testing with Nmap and Metasploit
HTTP Verb Tampering Demo
HTTP Verb Tampering Lab Exercise
HTTP Basic Authentication
Attacking HTTP Basic Authentication with Nmap and Metasploit
HTTP Digest Authentication RFC 2069
HTTP Digest Auth Hashing (RFC 2069)
HTTP Digest Authentication (RFC 2617)
HTTP Statelessness and Cookies
HTTP Set-Cookie with HTTPCookie
Session ID
SSL – Transport Layer Protection
SSL MITM using Proxies
File Extraction from HTTP Traffic
HTML Injection Basics
HTML Injection in Tag Parameters
HTML Injection using 3rd Party Data Source
HTML Injection – Bypass Filters Cgi.Escape
Command Injection
Command Injection – Filters
Web to Shell on the Server
Web Shell: PHP Meterpreter
Web Shell: Netcat Reverse Connects
Web Shell: Using Python, PHP etc.
Getting Beyond Alert(XSS)
Javascript for Pentesters: Introduction and Hello World
XSS: Cross Site Scripting
Javascript for Pentesters: Variables
Types of XSS
Javascript for Pentesters: Operators
XSS via Event Handler Attributes
Javascript for Pentesters: Conditionals
DOM XSS
Javascript for Pentesters: Loops
Javascript for Pentesters: Functions
Javascript for Pentesters: Data Types
Javascript for Pentesters: Enumerating Object Properties
Javascript for Pentesters: HTML DOM
Javascript for Pentesters: Event Handlers
Javascript for Pentesters: Cookies
Javascript for Pentesters: Stealing Cookies
Javascript for Pentesters: Exceptions
Javascript for Pentesters: Advanced Forms Manipulation
Javascript for Pentesters: XMLHttpRequest Basics
Javascript for Pentesters: XHR and HTML Parsing
Javascript for Pentesters: XHR and JSON Parsing
Javascript for Pentesters: XHR and XML Parsing
File Upload Vulnerability Basics
Beating Content-Type Check in File Uploads
Bypassing Blacklists in File Upload
Bypassing Blacklists using PHPx
Bypassing Whitelists using Double Extensions in File Uploads
Defeating Getimagesize() Checks in File Uploads
Null Byte Injection in File Uploads
Exploiting File Uploads to get Meterpreter
Remote File Inclusion Vulnerability Basics
Exploiting RFI with Forced Extensions
RFI to Meterpreter
LFI Basics
LFI with Directory Prepends
Remote Code Execution with LFI and File Upload Vulnerability
LFI with File Extension Appended – Null Byte Injection
Remote Code Execution with LFI and Apache Log Poisoning
Remote Code Execution with LFI and SSH Log Poisoning
Unvalidated Redirects
Encoding Redirect Params
Open Redirects: Base64 Encoded Params
Open Redirects: Beating Hash Checking
Open Redirects: Hashing with Salt
Securing Open Redirects
Cross Site Request Forgery Basics
Cross Site Request Forgery Trigger Tags
CSRF Multi-Step Operation Handling
Mitigating CSRF with Tokens
CSRF and XSS
CSRF Token Bypass with Hidden Iframes
Insecure Direct Object Reference
Insecure Direct Object Reference (Burp Demo)
2023-01-12
No hackiing today, just work! 🙂

2023-01-13 – 2023-01-15
Alomost hacking today. Got my new laptop today. I am moving from Dell XPS 13 to Dell XPS 17 with nvidia 3060
Need to move all data from my old one to new. Install new vm:s. Even if I am runing Linux it is alot of work.

Installed Nvidia Drivers and CUDA and got this on hashcat

Not to bad….
2023-01-16
Work today and 100 pages of PEN-200 pdf. As I said before my 1 year subscription is in the past so now pdf reading. Also started a very interesting API course AND it is free.
Please check out:
https://university.apisec.ai/library

2023-01-17
New PC on the way. Need to install som stuff!
2023-01-18
Work and hospital with dog, no hacking
2023-01-19
Work and hospital with dog, no hacking. But I made 1 hour of webinar at least…

2023-01-20 – 2023-01-24
Work, Work Work
2023-01-25
2 hours of web education from INE…Not so advanced, but repetition is the key right?

2023-01-26 – 2023-01-30
Work and work, and some free time. And manage a webinar from blackhills

2023-01-30
To much work but I manage to get 1,5 hour of API hacking

2023-01-31 – 2023-02-01
Work, Work
2023-02-02
Today webcats time, another great one from BlackHills

2023-02-03
Work, Work
2023-02-04
00.00 Time for OSCP attempt nr 2. This time I think it went better, and I did send in ~70 pages report. The exam day for me was 19,5 hours with the reporting part included. Lets hope I can start a new chapter and after 511 hours of traning Let It Be Done!

2023-02-04
Tired today, I do not know why? I am only 48 and still going strong….
2023-02-05
Coming…
Spreadsheet of my time
Will be a link to a real one, when I am done!
I am not done, but here is the link for below time list
https://github.com/RogerBergling/blog.invid.eu/blob/main/PNPT-OSCP-TIME.pdf



Wow this is some mission you are on with all these certs is a particular order! Hopefully you attain the OSCP eventually.
I’m currently working through the PWK labs. Started studying in January. My path was:
3 months THM – Beginner, Web & Offensive Paths
3 months PG – Worked through all TJ Nulls boxes on Proving Grounds Practice
3 months PWK – Where I currently am in the middle of it.
Exam in September probably.
LikeLike
I wish the same for you! Keep hacking! 🙂 Keep me posted how the exam went! I will cross my fingers for you!
LikeLike