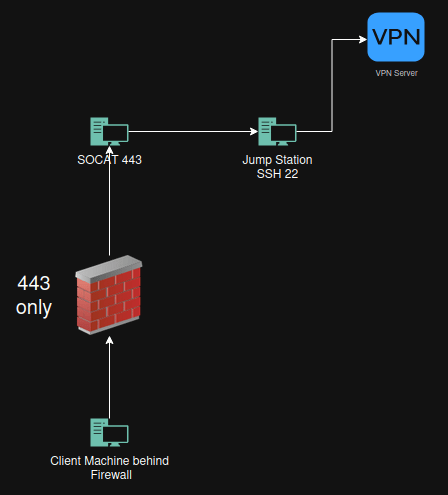
Goal Bypass firewall to get out with ssh Bypass firewall to use VPN client inside network that blocks for example Fortinet vpn client on port 443 Bypass firewall to get access to get to a machine inside my own network. Why this works Why This Works Simply running SSH on port 443 does not bypass... Continue Reading →
Hacking APIs: Understanding, Challenges, and Best Practices
I was doing a talk about Hacking APIs @ Plattform Summit 2025. Here is the presentation and all the commands. Applications / Toolshttps://www.apisec.ai/https://cloud.apisecapps.com/https://www.usebruno.com/ Educationhttps://www.home.apimasters.io/learnhttps://www.apisecuniversity.com/ crAPIhttps://github.com/OWASP/crAPI/bhttp://crapi.apisec.ai/loginhttp://crapi2.apisec.ai/login Information:https://danaepp.com/https://nordicapis.com/api Installation Install kali BurpSuitesudo apt-get install burpsuite Brunohttps://www.usebruno.com/downloadssudo apt-get install ./bruno_2.11.0_amd64_linux.deb FireFoxFoxyProxy Burpsuite Certifcatehttp://burpsuite Mitmproxy Certificatehttp://mitm.it Postmansudo wget https://dl.pstmn.io/download/latest/linux64 -O postman-linux-x64.tar.gz && sudo tar -xvzf postman-linux-x64.tar.gz -C /opt &&... Continue Reading →
What do I think of the Hacking Enterprises 2025 Edition course from In.Security with Will Hunt?
Offensive security courses are everywhere these days, but very few truly deliver a deep, hands-on experience that feels like the real deal. I recently completed the Hacking Enterprises 2025 Edition course from In.Security, led by Will Hunt, and after taking it twice now, I’m excited to share what makes this course stand out. Personal Experience... Continue Reading →
What do I think of the Detection Engineering for Beginners course from TCM Security with Anthony Isherwood?
I recently finished the Detection Engineering for Beginners course by TCM Security, taught by Anthony Isherwood. As always, I’ll keep this post short and focused just like the course claimed to be "for beginners"… more on that below. My Thoughts Let’s start with this: not every course is for everybody and that’s perfectly fine. The... Continue Reading →
What do I think of Security Operations (SOC) 101 from TCM Security with Andrew Prince
It’s not often that a course leaves me this impressed. Security Operations (SOC) 101 by Andrew Prince over at TCM Security is one of the most comprehensive courses I’ve taken in a long time and that’s saying a lot. This course doesn’t just cover SOC. It dives deep into everything surrounding it endpoint security, phishing... Continue Reading →
What do I think of Practical Windows Forensics course from TCM Security with Markus Schober
It’s been a while since my last post! Life and work got in the way, but I’m back and hoping to put out many more posts this year! Now, let’s dive into this amazing course—ractical Windows Forensics from TCM Security, taught by Markus Schober. If you're interested in Windows forensics, digital investigations, and incident response,... Continue Reading →
Securing LLM & NLP APIs: Lessons from APIuniversity
Securing LLM & NLP APIs: Lessons from APIuniversity As the use of large language models (LLMs) and generative AI continues to grow, so does the importance of understanding how to secure these technologies effectively. Recently, I completed the Securing LLM & NLP APIs course from APIuniversity, an essential training that arms developers, data scientists, and... Continue Reading →
What do I think of passing the ASCP exam from Apisec University
Passing the ASCP (API Security Certified Professional) exam is a notable achievement for anyone in the field of API security. APIsec University provides a structured and comprehensive approach to prepare for this challenging exam, and I can vouch for its effectiveness. Here are my thoughts on the experience and some advice for future candidates.Sign up... Continue Reading →
What do I think of the Practical Phishing Campaigns course from TCM Security with Aaron Wilson
Who should take this course? The Practical Phishing Campaigns course from TCM Security is tailored for a wide range of individuals within the cybersecurity domain. If you're a penetration tester, security analyst, or system administrator looking to enhance your phishing campaign skills, this course is ideal for you. It's also beneficial for those who have... Continue Reading →
What do I think of Practical Bug Bounty course from TCM Security with Heath Adam, Alex Olsen, and Jonah Burgess from Intigriti
The Practical Bug Bounty course by TCM Security, led by Heath Adams, Alex Olsen, and Jonah Burgess from Intigriti, is a thorough exploration of hacking and web application security. Alex's extensive knowledge and Heath's significant community contributions are evident throughout the course. Despite its focus on bug bounty hunting, the course offers a wide range... Continue Reading →
What do I think of Practical Web Hacking course from TCM Security with Alex Olsen
Web security is an ever-evolving field, requiring continuous learning and adaptation. TCM's course "Practical Web Hacking," led by the exceptional instructor Alex Olsen, is designed to equip cybersecurity enthusiasts and professionals with hands-on knowledge and skills to tackle real-world web security challenges. This blog post delves into what this course offers, who should consider enrolling,... Continue Reading →
What do I think of API Authentication course from APIsec University with Jacob Ideskog from Curity
In the ever-evolving landscape of digital interactions, ensuring secure communication between clients and servers is paramount. API authentication and authorization are fundamental concepts that protect sensitive data and ensure that only authorized users can access specific resources. In this blog post, we will explore key aspects of API authentication and authorization, drawing insights from the... Continue Reading →
What do I think of Practical API Hacking Testing course from TCM Security with Alex Olsen
Hi! As someone who has recently completed the Practical API Hacking Testing course from TCM Security, taught by Alex Olsen, I wanted to share my thoughts and experiences. This course is designed to provide comprehensive knowledge and practical skills for testing and securing APIs, an increasingly critical area in cybersecurity. As a final word I... Continue Reading →
Just completed the Securing API Server Course from @apisecu with Anthony Aragues! 🛡️ Fantastic insights into API security. Highly recommend it for anyone in the field. #APIsecurity #CyberSecurity @Burp_Suite #OWASP
Enhancing API Server Security: Best Practices from APISec University Introduction: API servers play a pivotal role in modern application architecture, enabling seamless communication between different software components. However, with this convenience comes the responsibility of ensuring robust security measures to safeguard sensitive data and prevent unauthorized access. In this blog post, we'll delve into various... Continue Reading →
Secbutler is cool tool to have in your toolbox when doing fun stuff like Pentesting, CTF or just having fun. Cheatsheets, listeners, revshells and more.
Hi! Link to tool: https://github.com/groundsec/secbutler Exploring Secbutler: A CLI-Based Security Tool I recently stumbled upon a gem in the realm of cybersecurity tools – Secbutler from Groundsec. In a world saturated with graphical interfaces and web-based platforms, Secbutler caught my attention for its command-line interface (CLI) approach. Now, you might be wondering, why make an... Continue Reading →
What do I think of Programming with AI – Mini Course from TCM Security with Heath Adams
Hi! Embarking on the journey of programming with artificial intelligence doesn't require an extensive background in coding wizardry. In fact, TCM Security's "Programming with AI - Mini Course" with Heath Adams is meticulously designed to be accessible to individuals with a basic understanding of programming fundamentals. Whether you're a cybersecurity enthusiast, a software developer, or... Continue Reading →
What do I think of Mobile Application Penetration Testing course from TCM Security with Aaron Wilson
Hi! In a world dominated by mobile apps, the importance of securing them cannot be overstated. My journey into mobile application pentesting began with a realization of the vulnerabilities these apps may harbor. Seeking a comprehensive course, I stumbled upon the TCM Security Mobile Application Penetration Testing course , and little did I know it... Continue Reading →
Knowledge schedule for 2024.
Embarking on the journey of 2024, I've already shared glimpses of my set goals, and now, it's the opportune moment to intricately document this path. This endeavor serves not only as a testament to my personal aspirations but also as an inspiration for you—proving that the pursuit of your dreams is not only worthwhile but... Continue Reading →
What are the plans for 2024 for my infosec knowledge update?
Remeber that repetion is the mother of knowledge. --Roger-- I have not been very active on the blogg in 2023, sorry for that. I hope I can change that for 2024 What is the goals for 2024 There has been some changes for 2024 regarding education budget, so I will need to do some changes for... Continue Reading →
Learn how to hack and how to secure your api, and do it for free. API Penetration Testing, OWASP API Security Top 10 and Beyond, API Security Fundamentals, Cross Origin Resource Sharing (CORS) and Error Disclosure.
Hi! It has been some time now between the posts, but life is getting in the way. The hard thing about security is that you will never learn enough you will need to educate your self all the time, new stuff comes out, new technology. It is nice that knowledge is easy to carry. 🙂... Continue Reading →
Passed this fantastic course API Penetration Testing Course from @apisecu with @hAPI_hacker. This is my review after finishing the course. #hacking @Burp_Suite #zapproxy #hacking #api @owasp
Hi! Today I want to say a few words about a course I finished yesterday night! This review could have been a one liner: Take this course, if you don’t you are missing something really cool! Big shout out for making this possible. Really great work! https://www.apisecuniversity.com/ Corey J. Ball https://www.linkedin.com/in/coreyjball/ https://twitter.com/hAPI_hacker Dan Barahona https://www.linkedin.com/in/rdbarahona/ https://twitter.com/danbarahona But I want... Continue Reading →
PNPT Exam review and how did I approach the exam. Delivered by @TCMSecurity @thecybermentor #Cybersecurity #hacking
I must start saying that this exam was great. I started doing practical exam during my Novell eDirectory 991 course back in the days. And I loved them. This is another exam that I must say goes to my heart. I love the practical stuff. One other thing to say about this exam is that... Continue Reading →
Review on Practical Web Application Security and Testing from @TCMSecurity and @mttaggart learn @owasp #hacking #education #almostfree
Hi! I do this one more time then I need to go back to the original schedule read here : https://blog.invid.eu/2022/01/06/my-ocsp-and-pnpt-journey-from-the-beginning-during-and-i-hope-the-end-tcmsecurity-thecybermentor-offsectraining-pnpt-oscp-joplinapp-reconmap-bhinfosecurity-strandjs-hacking-pentesting/ I did find this course very helpful so I need to say a few words. This course was amazing. One thing stands out from any other web course. After you finish the course you... Continue Reading →
Review on Practical Malware Analysis & Triage from @TCMSecurity and @HuskyHacksMK #malware #hacking #education #almostfree
Hi It is not often I do a post a review of web courses except in my journey post https://blog.invid.eu/2022/01/06/my-ocsp-and-pnpt-journey-from-the-beginning-during-and-i-hope-the-end-tcmsecurity-thecybermentor-offsectraining-pnpt-oscp-joplinapp-reconmap-bhinfosecurity-strandjs-hacking-pentesting/ But I did find this course so dam good that I need to shout it out. This course was amazing. I learned alot, new stuff for me. Matt Kiely @HuskyHacksMK who was the teacher is amazing,... Continue Reading →
How did I pass OSWP exam? Tips and Tricks. @offsectraining #PEN-210 #hacking #pentesting #wireless #INVID #dyslexia
Hi! Today I received my first certification from Offensive-Security (not counting PEN-100). If someone else is in progress of taking this course or thinking about it here are my tips and tricks. Here are some links from offensive security that you shall read if you will attend an exam from Offensive-Security. Verification https://www.credential.net/bac14e8c-24e1-43c5-a2c7-8d0751543caa Links https://help.offensive-security.com/hc/en-us/articles/360046904731 https://proctoring.offensive-security.com/student/login https://help.offensive-security.com/hc/en-us/sections/360008126631 https://help.offensive-security.com/hc/en-us/articles/360050299352 https://www.offensive-security.com/legal-docs https://help.offensive-security.com/hc/en-us/articles/360046293832 ... Continue Reading →
How to crack wireless networks. To get ready for PEN-210 OSWP certification. (For educational purpose only) @offsectraining #INVID Gruppen #OSWP #PEN-210
Time to do some wireless hacking. If you read my other posts you know that I am on a mission get OSCP. But sometimes you need to do something else. This is my attempt to do something else 🙂 Todo what I do in this post you need some hardware. At least a network card... Continue Reading →
What you need to know to prepare for OSCP exam? Or what I need to know. Labs, Reporting and Exam requirements. #OSCP #pentesting @offsectraining
Hi! I am preparing for the OSCP exam, and there is alot of information out there. I needed to know what I am suppose to know before I take the exam. If you are about to do this exam please read the links, I know there is a lot text, but it is important. My... Continue Reading →
Governance, Risk and Compliance (GRC) Analys Master Class with @Gerald_Auger #SimplyCyber @NIST #cybersecurity #education
I did take a small break today from Offensive Security today and found a realy nice course, not so practical but still very important. If some of below words is picking your brain this course is for youA Cybersecurity Primer, Compliance and Audit Work, Security Awareness Work, Cybersecurity Risk Work, Information Security Governance Work, Getting... Continue Reading →
Eat, Drink, Sleep and Shit security. How in a “easy” way keep you updated on what is happening out there. @BHinfoSecurity @ActiveCmeasures @WWHackinFest @intigriti #security #knowledge
How do you keep you updated on what is happening out there, I have some tools and workflow that will keep you busy. One thing you need to think about, not everything on the internet is the truth.The hard thing here is that there is endless information out there, but yo do not need to... Continue Reading →
My OSCP and PNPT journey from the beginning, during and I hope “the end”. @TCMSecurity @thecybermentor @offsectraining #PEN-100 #PEN-103 #PEN-200 #PEN-203 #WEB-100 #SOC-100 #PNPT #OSCP @joplinapp @reconmap @BHinfoSecurity @ActiveCmeasures @WWHackinFest @strandjs #hacking #pentesting
Intro Hi all! My plan is that under 2022 to take OSCP and PNPT exam. To get the full picture we start from the beginning. Why do I post this? Share knowledge is the simple answer, and I am getting old so I need to document everything I do. I think this is a good... Continue Reading →
Courses and Certifications that I have taking over the years. Knowledge is the key.
If you are interested in any just send me an email if you want information about them. This is mostly a reference page to other bloggposts. BHIS Webcast: Things NOT to Do in Pentest Reports: Tips, Tricks 2023-02-03 Future Red Team Rants: A breakdown in three parts 2023-01-26 All About Ansible - A Suite of... Continue Reading →
Open-Source Vulnerability Assessment and Pentesting Management Platform @reconmap #pentesting #opensource #hacking #opensource #cybersecurity
Hi again! Time to look at reconmap. We in this line of work love abbreviation, so I call this OVAPMP (Vulnerability Assessment and Pentesting Management Platform). I was looking for a tool/system documenting my work regarding vulnerability scans, pentest and bug bounty work. I have tried different kind of solutions, I think I have found the... Continue Reading →
DarkWeb tools, how to install and run @torproject @TebbaaX @splitgraph @sn1persecurity @DarkSearchApp #pentest #readteam #hacking
Hi! It is time to go dark. In this post we are gonna take a look at different tools that is out there for the not so light web. This post is not for you to learn how to go dark, it is for people to learn how things works. Do not go and do... Continue Reading →
Install, build and run Sn1per. Testing the free version. @Sn1perSecurity #attacksurface #infosec #assetmanagement #attacksurfacediscovery #bugbounty #platform #netsec #offsec #redteam #pentest #attacksurfacemanagement
Hi all out there. It is time to take a look at sn1per. A tool that automate opensource stuff for us. As always we start with the steps Install some os in my kase running kaliGet the docker fileBuildRun sn1per installation wget https://raw.githubusercontent.com/1N3/Sn1per/master/Dockerfile docker build -t sn1per . Below is gonna take some time to... Continue Reading →
How to approach security by learning or really any learning (my way) @albinowax @jaybeale @ralphte1 @goteleport @CyberDefenders @BanjoCrashland @BHinfoSecurity @dayzerosec @NakedSecurity @cert_se #pentest #PENTESTING #redteam #infosec
First thanx to all mention in this post! The hard thing about security is the wide range of stuff you have to learn if you wanna be the best. That is the goal you should have, I want to be the best. But the downside of this is that how do I learn everything, I... Continue Reading →
My thoughts about C2 and the tests @C2_MATRIX @metasploit @c2_matrix #Covenant @BYT3BL33D3R @BHinfoSecurity #PENTEST #PENTESTING #REDTEAM #INFOSEC #autossh #ssh
Hi, this will be a short one. But I must put down in words what my thoughts are about the C2 tests that I have been doing for some time now. Not so hard to set up and get it running. If you want to play around there are some really good blog post out... Continue Reading →
Fith step in setting up C2 environment. Using socat as front to SILENTTRINITY. Command and Control my way. @c2_matrix @byt3bl33d3r @porchetta_ind #pentest #pentesting #redteam #infosec
Now we are gonna look at SILENTTRINITY from @byt3bl33d3r I think this will be the last test of Command and Controll application. I have other stuff to do. But I hope you all had a good read and set some things in motions for you. Here is the link that you can read and download... Continue Reading →
Fourth step in setting up C2 environment. Using socat as front to Covenant. Command and Control my way. @c2_matrix #Covenant #pentest #pentesting #redteam #infosec
It is time for part 4 in this series to set up a Command and Control, and this time I am trying out C2 server Covenant. You can go and read about Covenant here https://github.com/cobbr/Covenant. A picture says more than 1000 words so lets start with that! Covenant Short list install kaliapt-get updateapt full-upgradesystemctl enable... Continue Reading →
Third step in setting up C2 environment. Using socat as front to merlin. Command and Control my way. @c2_matrix @merlin_c2 #pentest #pentesting #redteam #infosec
It is time for part 3 in this series to set up a Command and Control, and this time I am trying out C2 server Merlin. You can go and read about Merlin here https://github.com/Ne0nd0g/merlin. A picture says more than 1000 words so lets start with that! Merlin The short step by step list install... Continue Reading →
Second step in setting up C2 environment. Using socat as front to autossh. Command and Control my way. @c2_matrix #autossh #ssh #pentest #pentesting #redteam #infosec
It is time for part 2 in this series to set up a Command and Control, and this time I am using ssh for creating reversed ssh tunnel to my C2-1 server. So I can run ssh from a client machine and take over this machine from my C2-1 server. A picture says more than... Continue Reading →
First steps in setting up C2 environment. Using socat as front to metsaploit. Command and Control my way. @c2_matrix @metasploit #pentest #pentesting #redteam #infosec
Hi, I know that is been a while since the last post, but life got in the way. But it is time now. My goal in these coming post is to setup different Command and Control systems and try them out. Information about different C2 can be found on this fantastic site https://www.thec2matrix.com/ So as... Continue Reading →
New version of hashcat is out. Time to test version 6.2.0 @HASHCAT #LINUX4HACKERS #HASHCAT #LINUX #INFOSEC #HACKING #PENTEST #PENTESTING #REDTEAM #NVIDA #BRUTEFORCE #NVIDA #TESLAM60
Hi all! There is a new version of Hashcat out for you to try! Here you can download it https://hashcat.net/hashcat/ 312 different algorithms to use. The different attack modes are: Straight, Combination, Brute-force, Hybrid dict + mask, Hybrid mask + dict and Association Fixes There is 26 bugfixes in this release. New attack mode: Association... Continue Reading →
Attending Cyber Threat Hunting Level 1 w/ Chris Brenton | 4-hours and want to run the VM in QEMU/KVM this is how I got it to work. @ActiveCmeasures #activecountermeasures #AIHunter #ThreatHunting #Beacons #Activecountermeasures @Zeekurity
Hi all! If you are like me attending the Threat Hunting Training Course named Cyber Threat Hunting Level 1 w/ Chris Brenton | 4-Hours on Thursday and want to run the virtual machine in qemu/kvm native do it like this. Download and read the below link! https://www.activecountermeasures.com/cyber-threat-hunting-training-course/ As always start with the short version! Convert... Continue Reading →
CEH Master, LPT, eJPT and eCPPTv2. My thoughts about the exams ,courses and how I got there. @ECCOUNCIL @eLearnSecurity @ReadynezSocial @hackthebox_eu @RealTryHackMe @BHinfoSecurity @RedSiege @WWHackinFest @ActiveCmeasures
I am gonna try to explain how my dedicated my life to work and what it takes for me to get this far. This is gonna be about the penetrations exams that I took, but I would not have passed these if I did not took the Novell Netware Networking course back in the days.... Continue Reading →
Passing the eCPPTv2 certification from eLearnSecurity. 10 answers for you to pass the exam. Thanx to @eLearnSecurity @RealTryHackMe #eCPPTv2 @thecybermentor #infosec #hacking #pentest #pentesting #redteam #hackthebox #linux4hackers #blackbox
Got the eCPPTv2 Certification today. Nice way to start the year with. 7 days of penetration testing and 7 days of report writing. Total of 14 days. This is the schedule that you get. The penetration test is in form of black box. You can use what tool you want. Why invent the wheel again?... Continue Reading →
Adding automating pentest tools for WebApi to my hacking rig. Astra and Fuzzapi. @bsdbandit @RedSiege @TimMedin @Fuzzapi0x00 #OpenSource #Security #WebServices #API #webapi
This blog will be relatively short, but I thought the webinar I listened to was so interesting that I have to write about it. Webinar from Red Siege yesterday evening (21.00 Swedish time) regarding hacking webapi. Link: https://www.redsiege.com/api/. This was presented by @bsdbandit. I was blown away, this is really cool stuff. I was the... Continue Reading →
Explain in my own way how to do basic Buffer Overflow. With help from @RealTryHackMe #BufferOverlow #Hacking #INFOSEC #LINUX4HACKERS #pentest #pentesting #redteam
First this is not advanced BufferOverflow, more for me to write down and document what I did at tryhackme to get BufferOverflow Prep working. We start of what you need. Windows 7 box with ImmunityDebugger and mona installed. Access to the application ocsp.exe. You can do this online with tryhackme or download the application your... Continue Reading →
Why would you use masks with hashcat when you crack hashes in brute force mode. @hashcat #LINUX4HACKERS #HASHCAT #LINUX #INFOSEC #HACKING #PENTEST #PENTESTING #REDTEAM #NVIDA #TESLAM60 #NTLM #BRUTEFORCE
In this post I will try to explain why it is important to use masks when you crack password from hashes with hashcat. The machine that I run hashcat on has 2 Tesla M60 card and running Linux. Why do I not use longer password in this test, I do not want to wait 7... Continue Reading →
How to export/crack SAM database with internal Windows tools if you do not have access to mimikatz / hashdump / metasploit. As a bonus we also look at cached domain hashes. #LINUX4HACKERS #HASHCAT #LINUX #INFOSEC #HACKING #PENTEST #PENTESTING #REDTEAM #NVIDA #TESLAM60
Hi! I wanted to dump hashes on a Windows 10 box without any external tools. This is how I did it. We start at first with the short version Export SAM with reg.exeConvert SAM with impacket-secretsdump to get to the hashesUse hashcat to crack the hashes We start first with exporting the sam database with... Continue Reading →
Using MindMap application when doing pentest or ctf! Up for you to decide. #MindMaps #freesoftware #kali #linux4hackers #linux #infosec #hacking #pentest #pentesting #redteam @kalilinux #ctf #bugbountytips @insilmaril
I was thinking about a nice and easy way to save a penetration test and come up with this.Use a MindMap application.There is a alot of MindMap application out there. I am running Linux on my machine so I ended up with VYM. (http://www.insilmaril.de/vym/)The nice thing about VYM is that it is free and comes... Continue Reading →
Installing Crowdsec on my hacking rig. How to block unwanted connections. Like bruteforce attacks on ssh. @Crowd_Security @DanielMiessler #hacker #bruteforce #ssh #cybersecurity #Security
I was reading on Daniel Miessler website and got really excited about his article about replacement to fail2ban. https://danielmiessler.com/study/crowdsec/?mc_cid=970356fcef&mc_eid=fa6207cba8 ). Please subscribe to his newsletter, really nice reading. Daniel explains this application in detail and I want to show how I did the installation on my machines. Some difference are there. I wont say it... Continue Reading →
How to install and run Salt from @SaltStack in my hacking rig. @VMware @thehackscast @thatch45 #saltconf @DjJimmyChunga #hacker #automation
Hi again! Today we are gonna take a look at Salt from Saltstack. On Sunday I was walking the dog and was listening to the podcast thehacks. I got very inspired by the podcast and wanted to really try this. I have never seen this product before. I have done some other tests in my... Continue Reading →
Install LogonTracer in my hacking rig. #blueteam @jpcert_en #LogonTracer #ubuntu #linux #infosec #logging #hacking @Docker #logontracer @neo4j
It is time to test LogonTracer from @jpcert_en you can get your copy from https://github.com/JPCERTCC/LogonTracer From the website:LogonTracer is a tool to investigate malicious logon by visualizing and analyzing Windows active directory event logs. We start with a new installation of ubuntu. The servername for this is Logon. The installation is not in this post.... Continue Reading →
Add linux and windows machines to SecurityOnion Kolide Fleet @securityonion #opensource #qsquery #fleet @Kolide #linux @BHinfoSecurity
We have now come so far that we want to add things in my installation of SecurityOnion. And we will start with how to add Linux and Windows boxes to Kolide Fleet. I do not know if this is the right way but after a couple of hours I was able to see the vm:s... Continue Reading →
Installing Security Onion 2.3 in my hacking rig. @securityonion #opensource @Elasticsearch #zeek #grafana #qsquery #wazuh #thehive #playbook #kibana #squert #snort #cortex #fleet #suricata #logstash @BHinfoSecurity @elastic @TheHive_Project @grafana
I must thank @BHinfoSecurity to get my interest in this. There webinars is great, especially 30 minutes before the real webinar begins.Now lets get started. As you have seen I did installation of 16.04 version before. My mistake, to tired! No I have to do this again with the new version. Like 16.04 version this... Continue Reading →
Installing Security Onion 16.04 in my hacking rig. @securityonion #opensource @Elasticsearch #zeek #kibana #squert #snort @BHinfoSecurity @debthedeb
Hi, now after some other installations in my "lab" it is time to look at logging. I got really inspired by webinars from BlackHills, so a big shout out to them. They are doing great work to spread there knowledge to others!And soon I WILL get my backdoor and breaches card game! I do not... Continue Reading →
Hachcat benchmark numbers with a VM with Tesla M60 card PCI passthru. #ubuntu #linux4hackers #hashcat #linux #infosec #hacking #pentest #pentesting #redteam #invida #teslam60
I am running hashcat in a VM (ubuntu 20.04) with a PCI passthru NVIDIA TeslaM60 card. This is my first rig with a graphics card so I have no referense to the numbers below. But here is my benchmark test so you can compare. Running Cuda so I can access all memory on the card.... Continue Reading →
How to access internal machines with ssh tunneling. Tunnel rdp thru a jumpstation with ssh. #infosec #hacking #pentest #pentesting #redteam #linux4hackers #kali #parrotos #linux #linux4hackers #ssh
This is follow up of the previous post regarding my rig. How do I access this where ever I am? I use SSH tunneling for that. If I loose connection for some reason I always use tmux on the target so I can reconnect to the same session as before. We start with a picture,... Continue Reading →
How did I create hacking rig for ethical hacking. Based on VMware with Tesla M60. #infosec #hacking #pentest #pentesting #redteam #hackthebox #tryhackme #linux4hackers #ctf #kali #parrotos #linux #godaddy #linux4hackers
My goal with this project was to create a hacking rig that I can use when doing hackthebox, tryhackme and other ctf:s. I was lucky to get my hands on a server with Tesla M60 card. My other goal was also to have a server that I can use in phishing tests, and show others... Continue Reading →
How to get IPv6 and IPv4 support with proxychain4 running kali. #hack #kali #linux #infosec #hacking #pentest #pentesting #redteam #proxychain4
I wanted to use proxychain with IPv6, ended up with this configuration. If you have not install proxychain4 do that now! Tor configuration file add below /etc/tor/torrc SocksPort [::1]:9050 SocksPort 127.0.0.1:9050 ClientUseIPv6 1 ClientPreferIPv6ORPort 1 ClientPreferIPv6DirPort 1 Proxychain4 configuration file. Add the information below in the file under [ProxyList] /etc/proxychain.conf socks5 :: 9050 socks4 127.0.0.1... Continue Reading →
Spam-test. Test if your email adress / domain are on any blacklist or if anything is wrongly configured. Check for spf,dkim and other stuff. #pentesting #blueteam #cybersecurity #spam #tester
This is a simple way to test if your email security is ok. Open a web browser and access https://mail-tester.com and copy the destination email on the page. Then send a email to that address that you got from the page Then go back to the web page and press Then check your score. (wait... Continue Reading →
Buffer Overflow, how do I prepare for Penetration Testing Professional V5 buffer overflow part. @eLearnSecurity #bufferoverflow #infosec #hacking #pentest #pentesting #redteam #hackthebox #INVIDGruppen #INVID
I am not a programmer from the beginning so I struggle a lot with buffer overflow part of the PTP course. I can not turn back time 25 years and start study programming so how do a old dog learn buffer overflow? This is what I do. Watch Videos, I learn faster if someone tells... Continue Reading →
How to set up juice-shop @ heroku for free. Then begin hacking your own web application. @heroku @owasp #infosec #hacking #pentest #cybersecurity #webhacking
Update 2022-08-25 Seems that this is not gonna be free anymore 🙂 https://blog.heroku.com/next-chapter I was watching a YouTube video from https://twitter.com/thecybermentor and wanted to spread the word to my 2 followers. This is a great way to get started with web application hacking. You will set up your own environment in seconds. After the deployment... Continue Reading →
Create file with hostnames from website with cewl, then scan the webserver for vhosts with Metasploit vhost_scanner to find hidden virtual hosts on webserver. #infosec #hacking #pentest #pentesting #redteam #hackthebox #ctf #linux4hackers
We start to collect possible hostnames from websites with Cewl cewl http://10.10.10.1 -w cewl.txt You can also use some other switches like -d = deph to look on the website for words -m = minimum wordlengh -w = outputfiel So that the final command can look like this: cewl http://10.10.10.1 -d 5 -w cewl.txt When... Continue Reading →
CORE-IT is a FREE virtual conference hosted by Chappell University. The online event begins March 24th at 9 am Pacific Time. #wireshark #nmap #darknet @torproject #kismet #tcp #dns @LauraChappell https://www.engagez.net/coreit1#lct=entrance
I got an email regarding a free Virtual Conference 2020! Could be something real nice! https://www.engagez.net/coreit1#lct=entrance Agenda here: https://coreit.s3.amazonaws.com/CORE-IT_Agenda-v1f.pdf https://coreit.s3.amazonaws.com/CORE-IT_Agenda-v1f.pdf https://coreit.s3.amazonaws.com/CORE-IT_Agenda-v1f.pdf https://coreit.s3.amazonaws.com/CORE-IT_Agenda-v1f.pdf https://coreit.s3.amazonaws.com/CORE-IT_Agenda-v1f.pdf
Fishing with Raspberry Pi, Kali, Auto connect to VPN, Auto register domain with GoDaddy, Automatic SSL cert with Letsencrypt, Run Golang, Run Gophish @letsencrypt @golang @kalilinux @GoDaddy #kali #raspberrypie #linux #infosec #hacking #pentest #pentesting #redteam #gophish
This is just for demo, I used root as user, you should perhaps consider other user to do this. Installation of Kali Download Kali Image https://www.offensive-security.com/kali-linux-arm-images/ Flash the SDCARD with etcher on you Kali box or any other burning program. Put the sdcard in the PI and boot OpenVPN Autostart Download opvpn conf file from... Continue Reading →
How to exploit Active Directory ACL based privilege escalation path with Bloodhound and aclpwn.py. Then collect the hashes, if you are lucky to get that level of access with secretdump.py #kali #kalilinux #hacking #pentest #pentesting #redteam
This was done from Kali box. Of course the Sharphound was ran on a compromised computer. Used application Bloodhound and Sharphound ( https://github.com/BloodHoundAD/SharpHound ) aclpwn ( https://github.com/fox-it/aclpwn.py ) Steps to do it Get output with sharphound and put that on our kali box use -all when run the Sharphound. Start neo4j and bloodhound import the... Continue Reading →
How to turn of power management on the wifi in kali 2010.1 (or any other distro using NetworkManager). @kalilinux #kali #kalilinux #linux #NetworkManager
Sometimes there are issues with speed, performance, lost of connection to access points. This can be helpful in some configurations. Before: iwconfig wlan0 wlan0 IEEE 802.11 ESSID: Mode:Managed Frequency:5.26 GHz Bit Rate=6 Mb/s Tx-Power=20 dBm Retry short limit:7 RTS thr:off Fragment thr:off Power Management:on Link Quality=56/70 Signal level=-54 dBm Rx invalid nwid:0 Rx invalid crypt:0... Continue Reading →
Compile an exploit on ParrotOS for Windows 32bit. @ParrotSec #infosec #hacking #pentest #pentesting #redteam
I needed to compile an exploit in ParrotOS. Did not have a Windows machine at the moment. In this case it was MS03-26 for 32 bit. Before we begin we need to install some applications in ParrotOS sudo apt install mingw-w64 searchsploit ms03-026 searchsploit -m exploits/windows/remote/100.c x86_64-w64-mingw32-gcc 100.c -o shell.exe -lws2_32
Git pull with subdirectories. Instead of every subdirectory one by one.
If you have for example a github directory in our home directory and want to update all the applications at the same time, instead of going in to every subdirectory and git pull from there. You can do every subdirectory at the same time for i in */.git; do ( echo $i; cd $i/..; git... Continue Reading →
How did my journey to Licensed Penetration Tester (Master) Certification begins and ends. My own thoughts. #LPTMaster #penetrationtesting #infosec #eccouncil @ReadynezSocial @ECCOUNCIL
My journey began 2018-07-09 at Readynez ( Örenäs Slott) a rely warm summer week for Sweden anyway, almost 30 degrees Celsius. Here is what I think about about the journey that I choose to take. CEH Course There is a lot talk about this course on social media. But for a beginner like me this... Continue Reading →
CEH Practical – LPT Master – CTF – Notes in general
CEH Practical - LPT (Master) - CTF Notes I have gather these notes from internet and cources that I have attended . Special thanks to: JENS GILGES https://www.linkedin.com/in/jens-gilges-1aa719151/ I used this site as notepad to remember things, not to get you an answer. So if you don’t like it, don’t read it.... Continue Reading →
CEH Practical #CEH @ECCOUNCIL
I have read many things about that CEH is not that good, but I think otherwise. I think everyone in IT schould attend a cource like this. You learn alot, some basic some advanced stuff. You need to start from somewhere, and this is a good starting point. You need to learn how to walk... Continue Reading →